The most common route for data leakage from companies is 'copy and paste in web browsers'

Until now, 'attachments,' 'uploads,' and 'file sharing' have been considered risky routes for data leaks from companies to the outside world, but a recent survey has revealed that the most common case is 'copy and paste from a web browser.'
Why The Browser Has Become the Enterprise's Most Overlooked Endpoint - LayerX
Copy-paste now exceeds file transfer as top corporate data exfiltration vector | SC Media
https://www.scworld.com/news/copy-paste-now-exceeds-file-transfer-as-top-corporate-data-exfiltration-vector
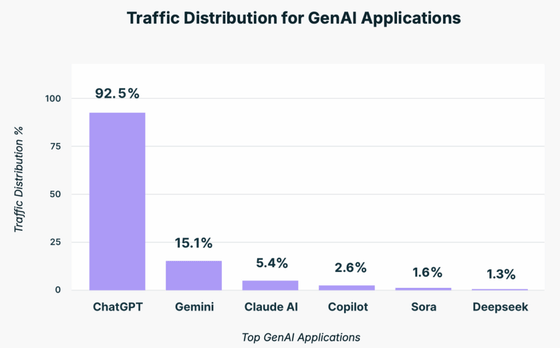
According to the 2025 Browser Security Report compiled by security firm LayerX , the vast majority of employees at surveyed organizations use generative AI tools, with 92.5% using ChatGPT. Gemini was next at 15.1%, followed by Claude AI at 5.4%, Copilot at 2.6%, Sora at 1.6%, and DeepSeek at 1.3%.
77% of users pasted data into prompts, 40% of uploaded files contained personal identifying information or card details, and 82% used personal accounts rather than company-provided accounts.
LayerX states that, up until now, data leaks from companies have mostly occurred via email, file sharing, and SaaS (Software as a Service) , and that the idea of data leaking via copying and pasting from a browser was completely unthinkable. While progress is being made in implementing data loss prevention (DLP) controls, the current situation is that the use of AI is spreading faster than companies can keep up.
LayerX points out that the emergence of AI-powered browsers such as OpenAI's ChatGPT Atlas and Perplexity's Comet also increases the risk.
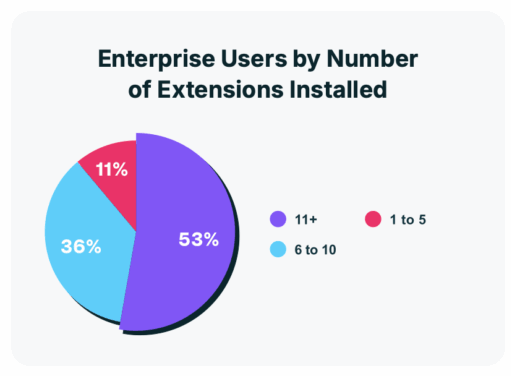
Of course, copying and pasting when using AI is not the only risk. Personal identification information and card information have also been leaked via instant messaging and SMS. Furthermore, the widespread use of unsecured browser extensions also increases security risks. 99% of respondents said they have at least one extension installed, and 53% have installed 11 or more.
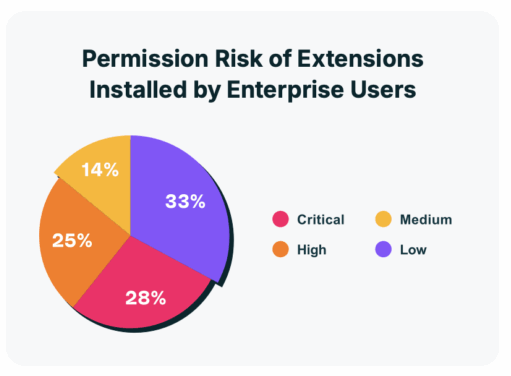
A total of 53% of users granted extensions 'high' or 'very high' permissions, posing a risk. 54% of browser extension developers can only verify their identity through a free email account, such as Gmail, and 51% of extensions have not been updated in over a year. However, LayerX recommends that enterprises and organizations should monitor extension usage, as granting high permissions gives extensions access to cookies and tokens.
Related Posts: