Fingerprint authentication can break through with a success rate of 80% if it is a high-precision fake fingerprint

Since the launch of TouchID on the iPhone 5s launched in 2013, fingerprint authentication has become a fairly popular biometric authentication.
Talos Blog || Cisco Talos Intelligence Group-Comprehensive Threat Intelligence: Fingerprint cloning: Myth or reality?
https://blog.talosintelligence.com/2020/04/fingerprint-research.html
Attackers can bypass fingerprint authentication with an ~ 80% success rate | Ars Technica
https://arstechnica.com/information-technology/2020/04/attackers-can-bypass-fingerprint-authentication-with-an-80-success-rate/
The Cisco Talos Intelligence Group has released a movie showing what types of fingerprint authentication are available and how they can be broken through.
Presentation: Fingerprint cloning — Myth or reality?-YouTube
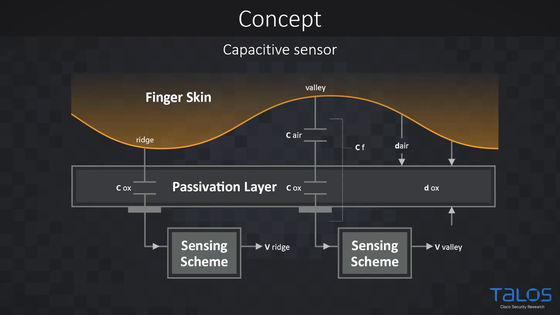
There are various mechanisms for fingerprint authentication. The capacitance method reads the difference in the amount of charge due to the unevenness of the fingerprint with a sensor and recognizes the distance between the unevenness of the fingerprint.
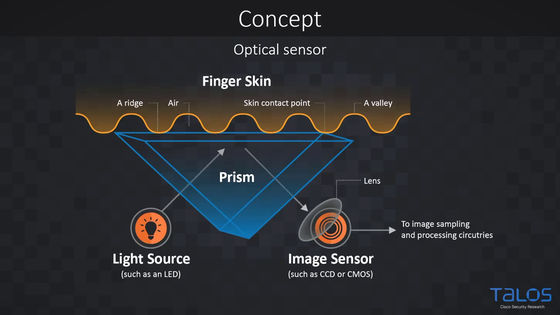
The optical system irradiates light to a fingerprint, reflects it off a prism, reads it with an image sensor, and detects the fingerprint.
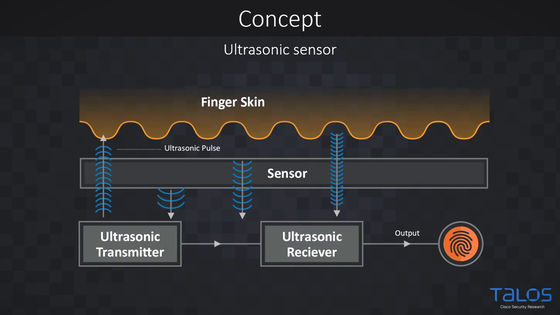
The ultrasonic method applies ultrasonic waves to a fingerprint and detects the fingerprint based on the strength and direction of the returned wave.
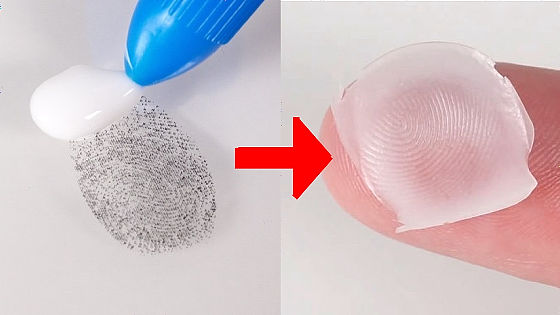
If you get the fingerprint you want to break through in some way ...
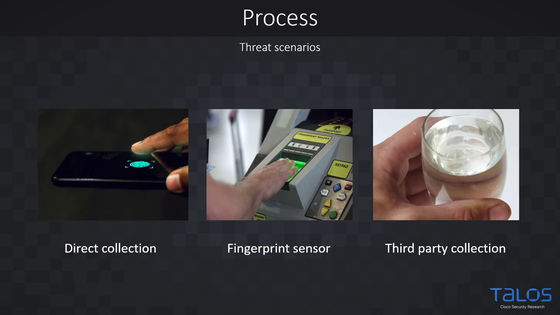
Optimize through image processing and make a mold.
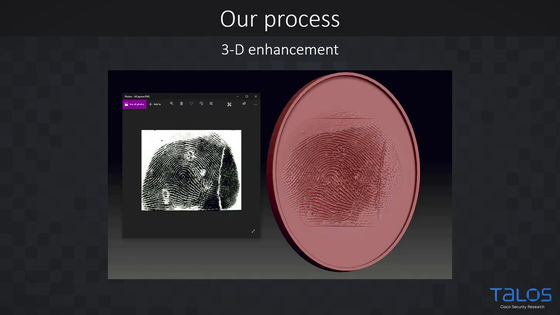
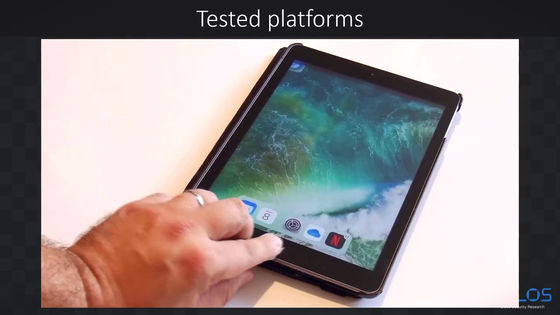
Applying the fake fingerprint created in this way to your finger and performing fingerprint authentication on your smartphone…
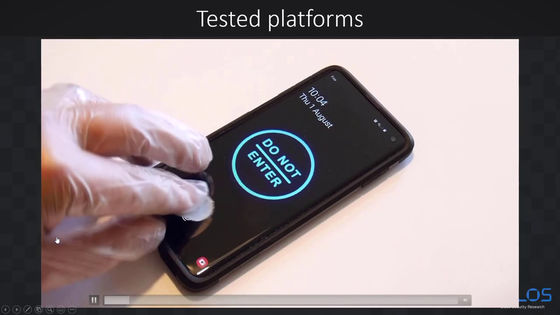
Successful breakthrough.
Even on iPad ...
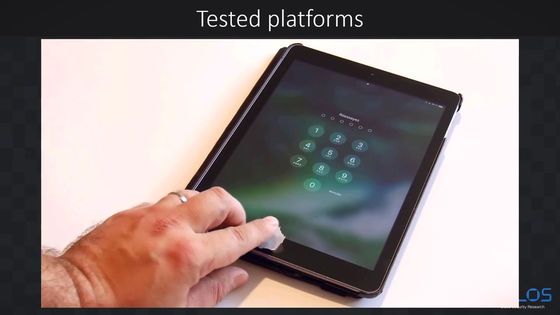
Breakthrough.
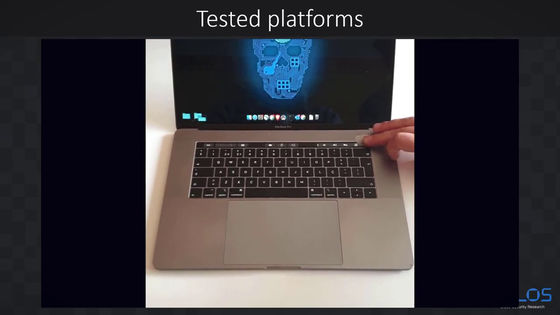
The same goes for Mac.
Even with a fingerprint lock padlock ...
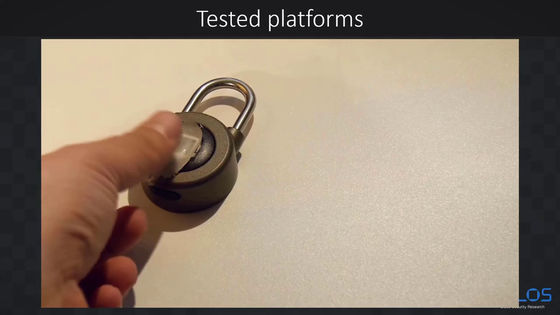
Of course it can be released.
The Cisco Talos Intelligence Group has conducted experiments on a number of devices, including the fifth-generation iPad, iPhone 8, and Samsung S10. As a result, the breakthrough success rate was about 80% on average.
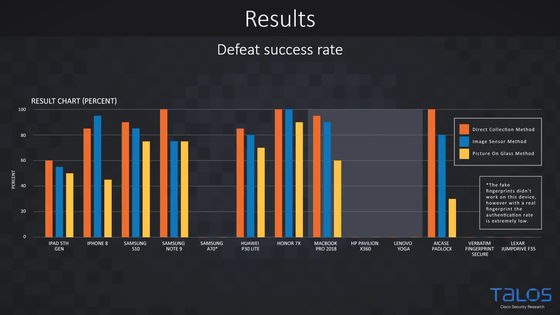
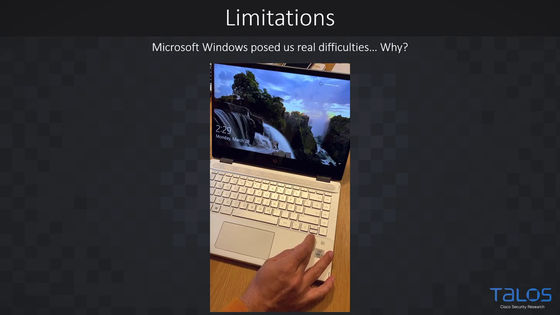
On the other hand, it seems difficult to break through fingerprint authentication on Windows.
Although the success rate was as high as about 80% on average, this is a number due to the creation of fake fingerprints with high accuracy, and the work to achieve it was difficult and boring.
Based on a variety of information, the Cisco Talos Intelligence Group commented that fingerprint authentication is at a sufficient level for ordinary people to use for privacy protection. However, if the attacker has sufficient motivation to aim for the person's fingerprint, such as when handling important information, and may invest money, use a strong password and token instead of fingerprint authentication. Recommended two-factor authentication.
Related Posts: