A movie showing that fingerprint authentication can be easily broken through with a 'fake fingerprint' that can be made for 500 yen
Many people should be using fingerprint authentication as an authentication method for PCs and smartphones. However, in fact, the movie shows that fingerprint authentication is unnecessary, and if you have a photo of a terminal that is dirty with fingerprints, you can easily break through with a 'fake fingerprint' created for about $ 5 (about 550 yen). increase.
Your Fingerprint Can Be Hacked For $ 5. Here's How. --Kraken Blog
You can see how easily fingerprints can be forged by watching the following movie.
Kraken Security Labs Bypasses Biometric Security With $ 5 In Materials --YouTube
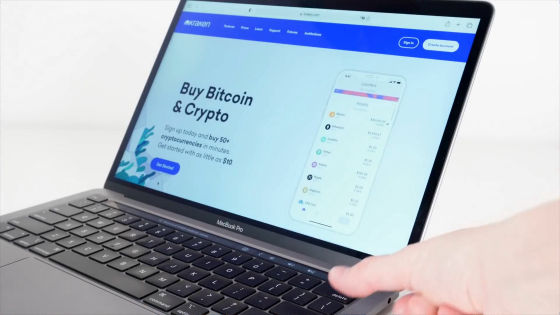
Many PCs and smartphones are equipped with a biometric authentication function. The following PCs have an authentication function on the upper right of the keyboard, and when you put your thumb on it ...

The PC has been unlocked. Such fingerprint authentication is very convenient because you don't have to remember or type in a long password.
However, fingerprint authentication can be easily imitated. It's easy to think that in order to break through fingerprint authentication, it is necessary to collect fingerprints from the person's finger in some way, but it is not necessary, and all you need is a photo of your PC screen that is dirty with your fingerprint.
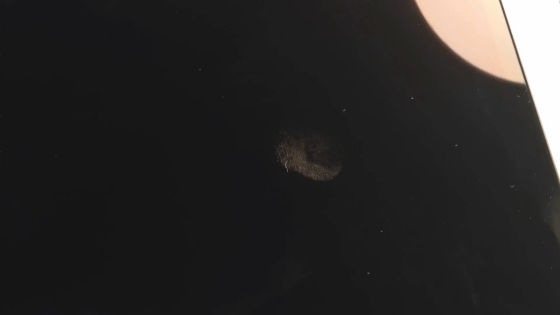
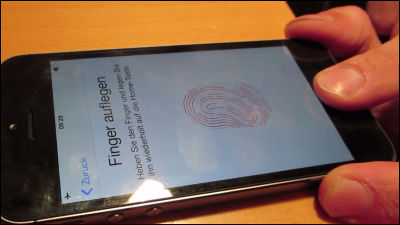
Or even fingerprint stains on your smartphone are possible.

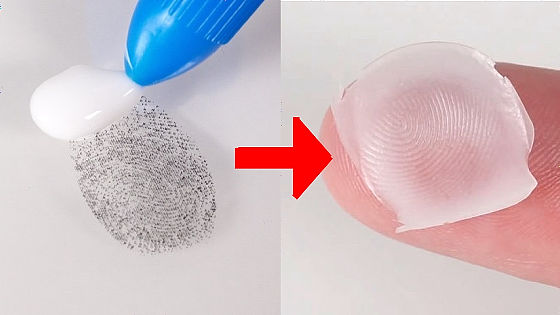
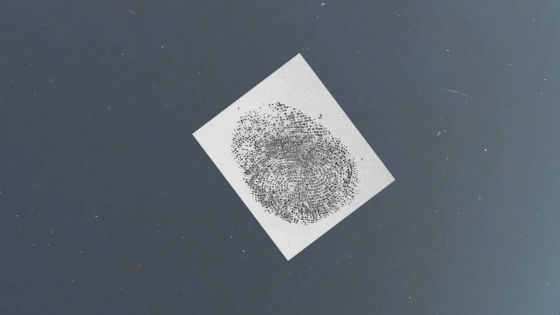
You can use Photoshop to image your fingerprints in as little as an hour. This is the 'negative' of your fingerprint.
Print fingerprint negatives on

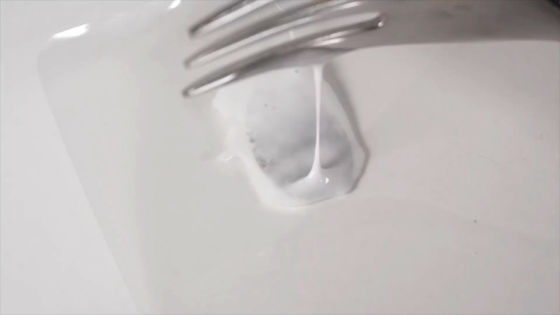
Drop the adhesive ...

Use a fork to spread the glue over the fingerprint.
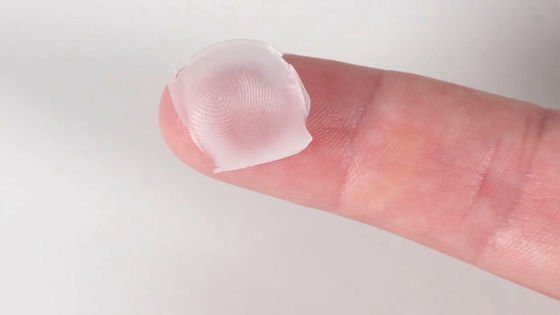
When the adhesive dries, the fake fingerprint is complete.
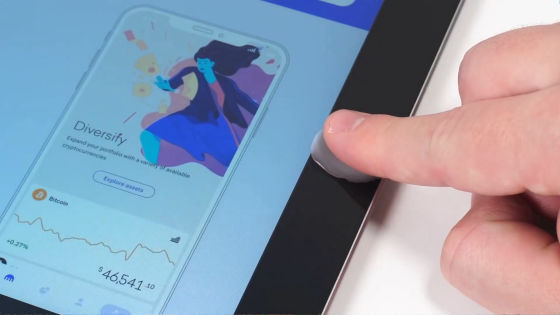
In the movie, I actually used a fake fingerprint to unlock the tablet.
The PC can also be unlocked.

The digital asset exchange Kraken, which published the movie, said in a blog that 'fingerprint authentication should not be considered a'strong password alternative'' 'fingerprints are yours, but relatively easy to abuse. You can. You should consider using it in combination with two-step authentication. '
Related Posts: