A serious vulnerability common to major OSs such as Windows and macOS was discovered, the cause was mis-specification interpretation of CPU architecture by OS vendor
OS operating on Intel CPU architectureHypervisor, It is said that there is a possibility that privilege escalation may occur by not performing appropriate processing, an information security organization under the US Department of Homeland SecurityUS-CERTI am calling attention. Windows · macOS has already addressed this vulnerability by updating.
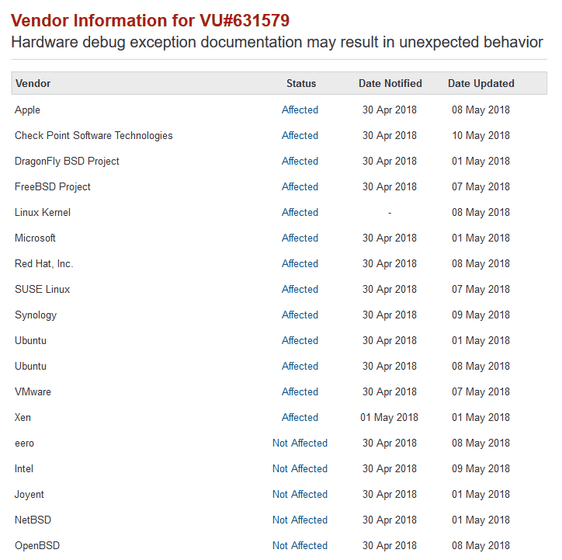
Vulnerability Note VU # 631579 - Hardware debug exception documentation may result in unexpected behavior
https://www.kb.cert.org/vuls/id/631579
Multiple OS Vendors Release Security Patches After Misinterpreting Intel Docs
https://www.bleepingcomputer.com/news/security/multiple-os-vendors-release-security-patches-after-misinterpreting-intel-docs/
The vulnerability "CVE-2018-8897" discovered this time is caused by improper checking and processing of exception conditions in major OS and hypervisor such as Windows, mac OS, and Linux. According to US - CERT, depending on the flow of exceptional instruction, there is a possibility that debug exception handling may be carried out in the highest privilege ring 0 hierarchy, and by exploiting this vulnerability, It is pointed out that there is a possibility of accessing and causing the system to crash.
In the table below, the one stated as "Affected" in the Status column is the OS / hypervisor subject to this security problem.
As for the cause of the vulnerability, in the report report "It is a serious vulnerability,Intel specification sheetIt is pointed out that the OS vendor overlooked it because it is not clearly written about the cooperation of the warning of the POP SS command and the MOV SS command and the interrupt gate semantics ".
Microsoft took place on 9th MayWindows monthly security updateIn thisDealing with vulnerabilitiesApple is also a security update for macOS High Sierra 10.13.4 on April 24thResponded. On Linux,Red Hat Enterprise Linux·Xen·DragonFly BSDEtc.DistributionResponse is being advanced for each.
Related Posts: