It turns out that credit card information in iPhone can be stolen via public wireless LAN
Depending on the public wireless LAN, the portal site may be launched by the browser after connecting. If you log in to the service from here, you will be able to use Wi-Fi for free, but we found a vulnerability that makes it possible to extract credit card data and personal information from iPhone using this function .
Evil Wi-Fi captive portal could spoof Apple Pay to get users' credit card data | Ars Technica
http://arstechnica.com/security/2015/06/evil-wifi-captive-portal-could-fool-users-into-giving-up-apple-pay-data/

Companies researching mobile securityWanderaThe research team found a vulnerability "I can display a fake login screen when using an automatic Wi - Fi login function on an iOS device". If you exploit this vulnerability, you can forcibly launch your portal site when connecting to Wi-FiCaptive Portal"Technology to display a page very similar to" payment screen of Apple Pay "when connecting an iOS terminal to Wi-Fi, it is possible to display personal information of a user who attempted to connect to Wi-Fi and credit card information It is possible to steal it.
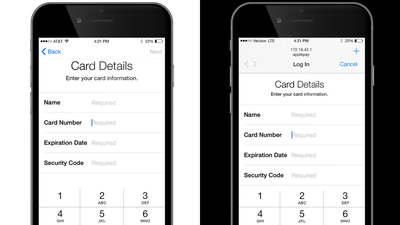
Here is the place where the payment screen of Apple Pay (left) and the settlement screen of fake Apple Pay callable by Captive Portal (right) are arranged. Although the page headings and input fields are almost the same layout, since the fake page is launched as the login screen, you can see that "Log In" is displayed in the title bar. Although it can be avoided if you look carefully, if Wi-Fi runs out during the settlement procedure of Apple Pay, if this screen is displayed at the point where you reconnect it, you can accidentally enter credit data etc. There is sex. It is also possible for attackers to place this page near the POS system where the Apple Pay compatible terminal is located or on Wi-Fi in a densely populated area.

This is a vulnerability "It is possible to display a fake login screen when an iOS device uses the automatic Wi - Fi login function", so it is the greatest measure to turn off Wi - Fi when it is not necessary I will. Wandera suggests "Apple and Google should put a meaningful alert when the portal site is launched" so that users are not deceived by such a signature.
In addition, Ars Technica reporting this vulnerability confirms with Apple's spokeswoman, but at the time of writing the article, Apple has not received a reply.
Related Posts:
in Mobile, Posted by darkhorse_log