Discovering the awful vulnerability that the iPhone / iPad will enter infinite restart loop

ByOmar Jordan Fawahl
For events dealing with encryption and information securityRSA ConferenceIt was revealed that iPhone and iPad equipped with iOS 8 or later are exposed to new vulnerabilities. It is known that if this vulnerability is exploited, a bug occurs that iOS can not be restarted indefinitely or applications can not be started.
"No iOS Zone" - A New Vulnerability Allows DoS Attacks on iOS Devices »
https://www.skycure.com/blog/ios-shield-allows-dos-attacks-on-ios-devices/
This vulnerability is named "No iOS Zone" and provides mobile specialized security servicesSkycureThings discovered. Actually this vulnerability allows you to check how the iPhone / iPad restarts indefinitely from the following movie.
IOS SSL Cert. Parsing Bug Uncovered by Skycure: Endless Reboot Cycle - YouTube
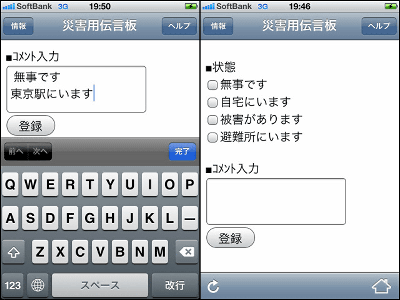
Apple's logo is displayed and booting up.

It changes to lock screen and shows the usual operation ... ...

Immediately after that the screen will be dark, Apple's logo will be displayed again and restart will start.

When thinking that the restart is over and the lock screen is displayed ......

I started restarting again. There is no way to strike a hand with this.

Also, if "No iOS Zone" is exploited, even if launching of iOS can be done without problems, a bug that the application crashes and can not be opened when launching an application to use the Internet has also been confirmed , The state can be confirmed from the following movie.
IOS SSL Cert. Parsing Bug Uncovered by Skycure: Crashes Most Apps - YouTube
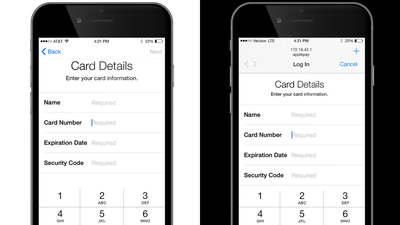
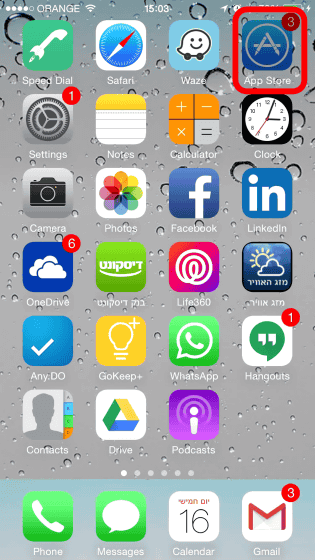
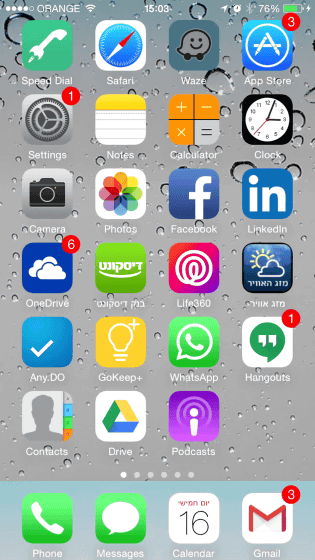
From the home screen, tap "App Store" in the upper right to launch.
The screen changes for a moment ... ...
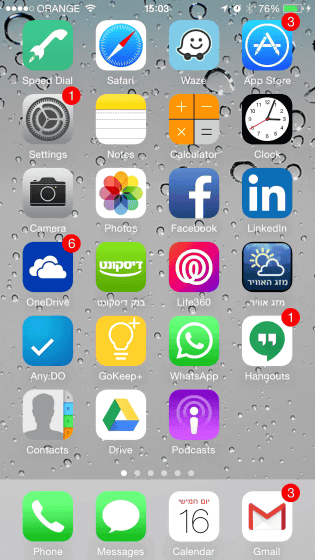
I will return to the home screen immediately.
Tap "LinkedIn" this time and start up.
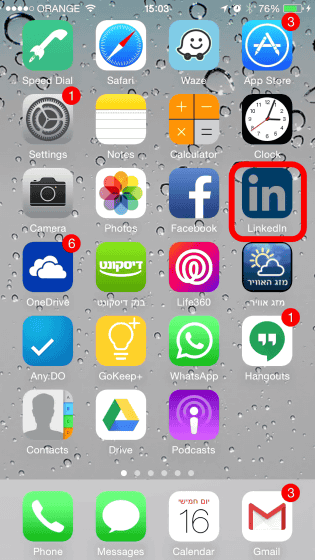
Although LinkedIn startup screen is displayed ......

I crashed and returned to the home screen without booting up.
The vulnerability "No iOS Zone" revealed this time relates to SSL communication of iOS 8, and the above trouble occurs when the terminal tries to connect to the server. We know that the presence of Wi-Fi spots is a big concern for this behavior, but even if you are not actually connected to any Wi-Fi hotspot, you can use iOS terminals There are risks occurred simply because there is.
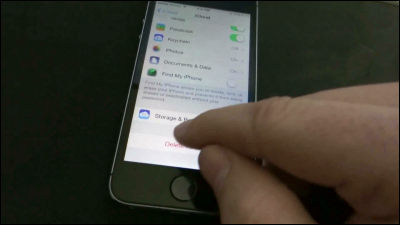
The high risk of being affected is an iOS terminal that contracts with a mobile carrier and uses a line. A terminal contracted with a carrier is automatically set to connect to some network, for example, if you are contracting with AT & T in the USA, it is set to connect automatically to the network "attwifi" , There is no way to cancel on the user side, so there is a high risk of bugs occurring.
Skycure does not disclose the details of how to exploit No iOS Zone, and currently cooperates with Apple to work on fixing vulnerabilities. As a workaround for vulnerability, Skycure recommends the following three methods.
· Block iOS device from suspicious Wi-Fi network or move out of Wi-Fi network
· Update to iOS 8.3
· Avoid connecting to a free Wi-Fi network
Related Posts: