Security camera Wyze Cam revealed a vulnerability that was accessible to anyone for three years

by Davidlamma
In March 2022, it became clear that the camera made by security camera maker Wyze had a vulnerability that made it accessible via the Internet and that it could be executed remotely. It is said that these vulnerabilities were discovered in 2019 and have already been addressed at the time of article creation, but older models can not be fixed because support has ended, and security companies that discovered the vulnerabilities We are appealing to stop using the applicable camera.
Wyze Cam flaw lets hackers remotely access your saved videos
https://www.bleepingcomputer.com/news/security/wyze-cam-flaw-lets-hackers-remotely-access-your-saved-videos/
Wyze knew hackers could remotely access your camera for three years and said nothing --The Verge
https://www.theverge.com/23003418/wyze-cam-v1-vulnerability-no-patch-bitdefender-responsible-disclosure
A vulnerability in Wyze's camera was discovered in 2019 by researchers at Romanian security firm Bitdefender. The vulnerability is that when you insert an SD card into Wyze's security camera, its symbolic link is automatically created in the www directory with no access restrictions. In other words, anyone can access the video, images, and audio stored on the SD card via the web server.
In addition, the SD card also stores the device log file, which contains the UID (device identification number) and encryption key. There was also a remote execution vulnerability because it could be accessed externally.
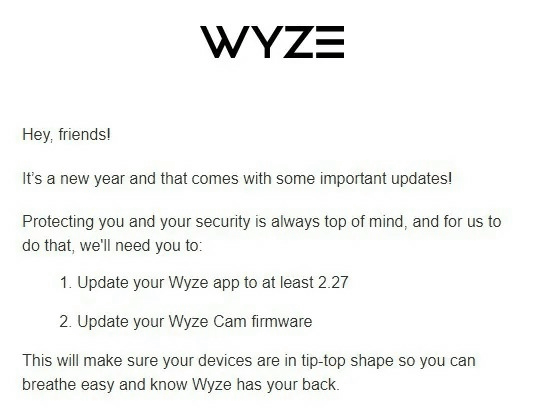
The anyone-accessible vulnerability was addressed in the September 24, 2019 security update as ' CVE-2019-9564 '. The remote execution vulnerability has been fixed in the November 9, 2020 update as ' CVE-2019-12266 '. The handling of SD cards, which caused a number of vulnerabilities, was fixed in the firmware update delivered on January 29, 2022.

However, a series of security updates were only available in Wyze Cam v2 and v3 released in February 2018 and October 2020, not in Wyze Cam v1 released in August 2017. Wyze Cam v1 will end support in 2020 and Wyze has not fixed the issue, leaving the remote execution vulnerability permanently unfixed in Wyze Cam v1. In addition, Wyze Cam v1 was announced to be discontinued in January 2022, before the vulnerability was revealed.
Bitdefender, who discovered the vulnerability, said, 'Vendor-side logistic and hardware restrictions are urging Wyze Cam v1 to be deprecated. We recommend that you stop using this hardware as soon as possible.' increase.
Regarding this, Wyze did not explain the security risk to the user and said, 'Continuing to use Wyze Cam v1 after February 1, 2022 is risky, so Wyze does not recommend it and is completely self-sufficient. I will be responsible for it. '
Sean Hollister, a reporter for the IT news site The Verge, said he was using Wyze Cam v1. You wouldn't think of it as a serious vulnerability. '
Hollister also criticizes that not only was Wyze not revealing the vulnerability discovered by Bitdefender to users, but it was unusual for Bitdefender to not disclose it for nearly three years. It is true that publishing the survey results before the vendor provides the patch has a high security risk, but usually it is said that the release date is usually set to 1 to 2 months after contacting the vendor.
Regarding this, Bitdefender said, 'We usually have a grace period of up to 90 days, but the vulnerabilities we have discovered are so serious that it is potentially possible to publish this report without Wyze's awareness and mitigation. We have determined that it will have an unknown impact on millions of users. '
'If these vulnerabilities were bad enough to discontinue Wyze Cam v1 in January 2022, users should have known it as of 2019,' Hollister said. He revealed that he had immediately discarded the Wyze Cam v1 that he had been using, and expressed his anger, saying, 'I will never use Wyze's products again.'

Related Posts: