Pointed out that it is not necessary to break through the two-step verification when disabling the two-step verification of the Google account

' Two-step verification ', which uses the authentication code sent to the device or email address associated with the account in addition to the normal password to access the account, is an important system for improving security. However, 'the result of engaged specifications of the principal of errors and system, the Google account password manager two-step authentication of, had been released without being caught in a two-step authentication by hackers' for the case that, of software developers Amos Mr. explains.
Beware the Google Password Manager-fasterthanli.me
https://fasterthanli.me/articles/beware-the-google-password-manager
Disabling Google 2FA Doesn't Need 2FA
https://www.infoq.com/news/2020/07/google-password-2fa-woes/
Amos, a hacker who has disabled two-step verification for Google's password manager, admits that he is mostly responsible for the failure. Amos needed to use macOS to run the builds of the software he worked on, but Amos himself didn't have a device capable of running macOS. So Amos rented a cloud OS machine that can use macOS without an Apple device and ran the build.
Amos used a service called NoMachine that allows users to remotely access virtual desktops. Mr. Amos, who used NoMachine to operate the virtual desktop of macOS, said that he accidentally saved his login information to Safari after logging in to his Google account from Safari. Amos regrets the act as 'stupid' and 'shouldn't have been done' and admits it was his mistake.
And luckily, a hacker who was doing a port scan looking for the attack destination discovered TCP Port 4000 which is the default port of No Machine used by Amos. I don't know if it launched a brute force attack or guessed the local user password, but in some way it broke into NoMachine's virtual macOS desktop, which Amos was using.

When Amos reconstructed the hacker's behavior after the incident was discovered, the hacker noticed that there was a Google session before after breaking into NoMachine's virtual desktop and tried to log in to Gmail. Since Gmail was an 'expired session', Google seems to have requested 're-enter password', but the password saved in Safari was automatically entered there.
Of course, Amos had two-step verification set up for his Google account, so any attempt to log in to the account on a new device would require two-step verification, which would prevent unauthorized login. However, in this case, the hacker used NoMachine's virtual desktop ``the same as Amos logged in to his Google account'', so it was not considered as a suspicious device and two-step verification was not done. That.
The hacker logged in to Mr. Amos's Google account and accessed the 'password of the website logged in from Chrome' stored in the account. Fortunately, Amos basically uses a different password manager, and the passwords stored in Google's password manager were mostly for less important websites. As a result, the attack did not cause much financial damage, but it was not the only problem, Amos said.

Mr. Amos noticed the hacking when he was notified of his smartphone saying 'There was a login attempt from the Buenos Aires IP address' and was requested to perform two-step verification. Maybe a hacker accidentally made a mistake or tried to log in from a place other than usual, so Google detected a suspicious login and blocked it.
In this one case, Amos noticed that he was exposed to a hacker's attack, but when he later looked at Google's account settings, he found that the two-step verification of the Google account was disabled. Discovery. Until he looked at his account settings, Amos didn't realize that two-step verification was turned off for his Google account. Amos said, 'I didn't receive any notifications! There was no email or phone. Worst of all , a hacker needs my two-step verification credentials to disable two-step verification. I didn't .'
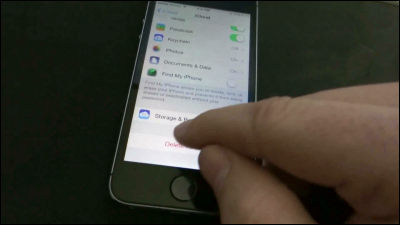
If you are logged in to your Google account, you can disable 2-step verification simply by selecting the item in 'Security' and checking the popup window. Therefore, if there is a 'special situation in which a third party can log in to your Google account by going through the two-step verification that you have set up' like this time, you can use the two-step verification itself without breaking the two-step verification. It will be invalidated.
Amos acknowledges that it was his fault that the hacker was able to log in to the Google account, but regarding the point that 'two-step verification is not necessary to disable two-step verification', Google's specifications Pointed out that there is a problem with. Amos recommended using a third-party password manager if possible, or setting a passphrase separate from your Google account password.

Related Posts:
in Web Service, Security, Posted by log1h_ik