The trend of cyber attack is malware that misused NSA tool infected with more than 500,000 PCs

ByMario Antonio Pena Zapatería
Cyber Security MediaThe Hacker NewsAccording to 2017, malware made using the tools of the National Security Agency (NSA) which leaked was prevalent among cyber criminals. More than 500,000 PCs are infected by malware using this tool and are damaged.
Cryptocurrency Mining Malware Infected Over Half - Million PCs Using NSA Exploit
https://thehackernews.com/2018/01/cryptocurrency-mining-malware.html
It is no exaggeration to say that 2017 was the year of information leakage and ransom attack by ransom malware (Ransomware). Cryptographic currency-related malware is "a high rate of return option" for cyber criminals, and threat changes in cyberspace are occurring.
According to some security companies, "Eternal BlueA new malware that performs encryption currency mining diffused by a tool called "Reporting" has been reported. EternalBlue is a tool manufactured by NSA,Stolen from NSA by hacker group shadow brokers and released, Which was prevalent in more than 150 countries RansomuueaWanna CryIt was also used.

ByApe Lad
According to a researcher at security company Proofpoint, many Windows PCs around the world are using malware "SmominruInfected with the encryption currencyMoneroThe botnet to mining is formed. If you earn millions of dollars (about hundreds of millions of yen) for this botnetIt is estimated. Smominru itself is made using NSA's tools and is vulnerable to the "Server Message Block (SMB)" protocol used on Windows "CVE-2017-0144It is what used it. At least as of May 2017, Smominru's botnet was formed by more than 526,000 infected PCs. According to the researchers, it is thought that many of the infected PCs were servers before Windows security patch was applied.

ByWhywhys
Smominru's botnet has been estimated to have mined $ 3.6 million (about 400 million yen) of Monero, and the operator who is manipulating the botnet got 24 Monero per day, or 8,500 dollars (about 940,000 yen) We have acquired equivalent currencies by mining and take away computing resources of millions of PCs. The high percentage of botnet infected PCs is Russia and India, and Taiwan's PC.

By401 (K) 2012
Smominru's botnet infrastructure control host is a DDoS attack protection agentSharktechIt is protected by the service of the company. Sharktech received notification, but the company ignored the notification of cheating.

ByLeszek Leszczynski
According to Proofpoint's researchers, cybercriminals use at least 25 PCs to scan the Internet to find vulnerable Windows PCs, and use NSA tools and remote desktop protocol Vulnerability"CVE-2017-0176I used to spread the botnet.BitcoinCybercriminals seem to have dramatically increased their interest in Monero, as mining has consumed a lot of computing resources.
For reference, Bitcoin can advance mining more advantageously as more computation resources are involvedHuge mining factoryIs created and necessary to expand its scaleGraphic board skyrocketing and difficult to obtainIt is happening that you become.
Infiltrate the world's largest mining plant digging Bitcoin, a cryptic currency that continues to soar, to approach the horrific reality of mining sites that overwhelm 25,000 machines - GIGAZINE

According to Proofpoint's researcher, in order to efficiently minerize Monero, it is not enough for desktop PCs alone, and the use of a wide range of botnets is a profitable result for botnet operators There is that. This Smominru's botnet is tenacious and uses all means available to enlarge it, for example, many methods of recovering after "sinkhole" which is latent in the PC, for example, are found, and the botnet and its infrastructure Considering the operator of botnet that enables resilience and remarkable profit, these activities are ongoing and it can be predicted that the infected PC is latent.
Another security company CrowdStrike has another infected encryption currency fileless malware, commonly known as "Wanna MineWe have posted it on the blog, and NSA tool EternalBlue is also used for this malware. A PC infected with WannaMine is forced to mining the encryption currency Monero. WannaMine, a fileless malware, does not download related applications and does not leave them on the PC, so it is difficult to detect WannaMine by antivirus programs.
CrowdStrike's researcher said about this method "This malware keeps computing resources under pressure when infecting enterprise servers and stops enterprise server operations for several days to several weeks, such as crashing systems and applications In addition to that, cybercriminals widely force the browsers of the website to force miningCryptojackingWe adopt the method called. It is a method of mining the encryption currency using browsers' CPU power with browser based JavaScript ".
A method similar to this method is a popular torrent website that was discovered in September 2017The Pirate Bay"Is a technique that used CPU resource for virtual mining of the CPU without consent to the viewer and method to hide in free Wi-Fi discovered in December 2017,Laptop connected to Starbucks Wi-Fi arbitrarily virtual miningNew cases are being born one after another that consume computation processing resources without consent, such as examples that are allowed to participate in.
Will the popular site become a source of income instead of virtual currency mining and advertisement with the CPU power of the viewer using the large number of accesses? - GIGAZINE

A laptop connected to Starbuck's Wi-Fi was being allowed to participate in mining virtual currency without permission - GIGAZINE

CrowdStrike's researcher said, "In recent reports, attacks by cryptographic currency malware have introduced NSA tool EternalBlue, and researchers advise users to update their systems and software. In 2017 Microsoft distributes security patches to malware created using EternalBlue. "
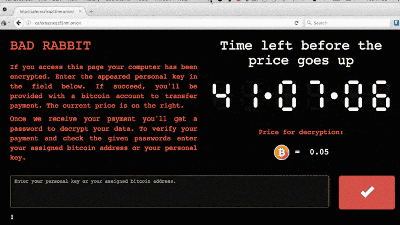
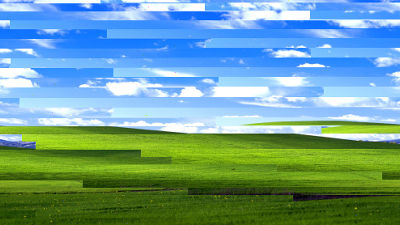
As malicious Wanna Cry, made with Eternal Blue in June 2017, caused too many victims, Microsoft is an exceptionally unusual OS, security is an unsupported OSWe also distribute security patches to Windows XP and this "malicious attack on national level"There was a situation to deal with.
Security update to Windows XP, patch prepared for "national level attack" to be manually downloadable by June Windows Update - GIGAZINE
In 2017 cyber crime "Ransomware" and "Encryption currency malware" produced a lot of victims and damages. Although it can not be predicted clearly what kind of cyber crime is in 2018, in the case of Ransomware "Wanna Cry", it will not hurt if it hits even a patch that was released more than two months before it appeared There are many cases that are not available, and backing up data that becomes a hostage against Ransomware is effective. Although it is fundamental, in 2018 it seems better to go frequently instead of handling the security patch management of PCs and servers, updating security software, and backup.

ByChristiaan Colen
Related Posts:
in Software, Web Service, Security, Posted by darkhorse_log