Infection damage of malware 'Bad Rabbit' which encrypts data and requests ransom is rapidly expanding
In 2017 "Wanna Cry"When"ExPetr (NotPetya)Two malware, the world's most prevalent, have been raging, but as the third wave "Bad RabbitIt is confirmed that malware called "rapidly expanding mainly in Europe" is rapidly expanding.
Bad Rabbit: A new ransomware epidemic is on the rise - Kaspersky Lab official blog
https://www.kaspersky.com/blog/bad-rabbit-ransomware/19887/
Bad Rabbit ransomware - Securelist
https://securelist.com/bad-rabbit-ransomware/82851/
Bad Rabbit: New Ransomware Attack Rapidly Spreading Across Europe
https://thehackernews.com/2017/10/bad-rabbit-ransomware-attack.html
New Ransomware 'Bad Rabbit' Spreading Quickly Through Russia and Ukraine - Motherboard
https://motherboard.vice.com/en_us/article/59yb4q/bad-rabbit-petya-ransomware-russia-ukraine
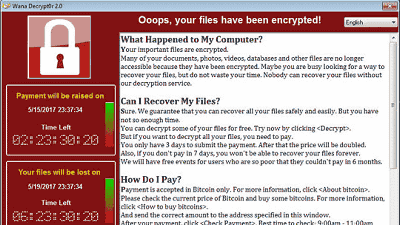
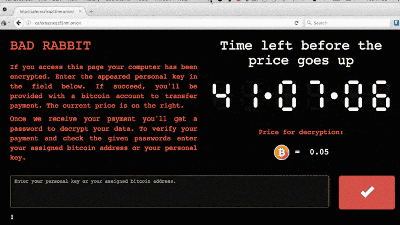
"Bad Rabbit" is a malware infected rapidly in Europe such as Ukraine, Turkey, Germany, mainly in Russia, if saved data is encrypted when it infects, if you want the data to be decrypted the virtual currency bit It is threatened with paying 0.05 BTC (about 32,000 yen at the time of article creation) with coins. DiskCryptor is used for encryption, and data is encrypted with RSA 2048.
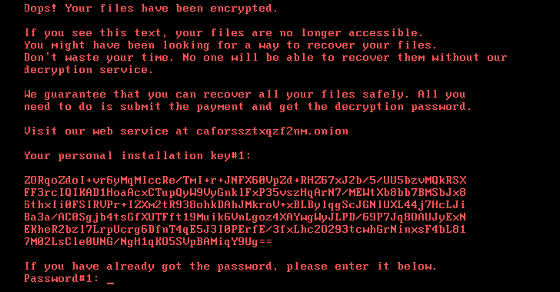
For PCs infected with Bad Rabbit, a warning screen will appear prompting you to pay a bit coin after logging in to Tor's designated web site and a countdown showing a payment deadline of about 40 hours will be done. In addition, it will threaten to raise the decryption cost this time when the deadline expires.

More than 200 organizations and organizations already infected with Bad Rabbit have been confirmed, including Russian news agency Interfax and others.
#BadRabbit# cryptorattacked a number of Russia's major media.@interfax_newspic.twitter.com/5iLNs 131 Ml
- Group - IB (@ Group IG - GIB)October 24, 2017
Interfax has tweeted that the server is down due to a cyber attack.
Из-за хакерской атаки в работе серверов Интерфакса возник сбой. Технические службы предпринимают все меры для восстановления работы систем.
- Интерфакс (@interfax_news)October 24, 2017
In addition, Security R & D Group - IB has revealed that Bad Rabbit is attacking Fontanka, government agencies in Ukraine and Odessa Airport in addition to Interfax.
According to the initial analysis of Kaspersky Lab, it is known that Bad Rabbit is infected by manual execution of a fake Adobe Flash Player installer (install_flash_player.exe) embedded in the site. And Kaspersky Lab says that the news media web site contains an installer with malware. ESET security researchers also pointed out that Bad Rabbit infection routes include not only fake Flash Player installers but also open source softwareMimikatzTo exploit the possibility of spreading infection in a data sharing system using the SMB protocol of Windows.
Related Posts: