Malware "NotPetya (GoldenEye)" that caused system down of central banks, state-run communications, Chernobyl nuclear power plant has become a major fashion at the world level

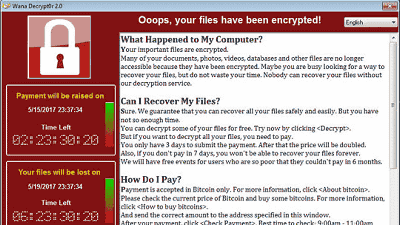
In May 2017 "Wanna Cry"Malware called a major epidemic worldwide has brought about a great deal of damage to medical institutions and automobile manufacturing lines. About 1 month after the outbreak of that WannaCry new malware "NotPetyaAppeared. We are eroding all over the world in a progressive form while showing great influence and high infectious power, such as driving government agencies and power companies to malfunction.
New ransomware outbreak - Kaspersky Lab official blog
https://blog.kaspersky.com/new-ransomware-epidemics/17314/
A new ransomware attack is infecting airlines, banks, and utilities across Europe - The Verge
https://www.theverge.com/2017/6/27/15879480/petrwrap-virus-ukraine-ransomware-attack-europe-wannacry
Another Massive Ransomware Outbreak Is Going Global Fast
https://www.forbes.com/sites/thomasbrewster/2017/06/27/ransomware-spreads-rapidly-hitting-power-companies-banks-airlines-metro/
Hacker Behind Massive Ransomware Outbreak Can not Get Emails from Victims Who Paid - Motherboard
https://motherboard.vice.com/en_us/article/new8xw/hacker-behind-massive-ransomware-outbreak-cant-get-emails-from-victims-who-paid
Initially, Kanspersky Lab's analysis of "Ransomuware" who was wreaking newly was reported as "a subspecies of Ransomware" Petya ". However, after analyzing Kaspersky Lab, Avast, etc., it turned out that it was a completely new Rangsumware borrowing the code of Petya. As a result, the so-called "NotPetya" is given as a new species that is not Petya. The security company Bitdefender is NotPetyaName "GoldenEye"I am attaching.
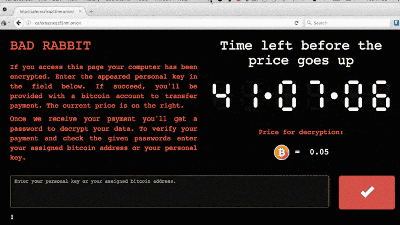
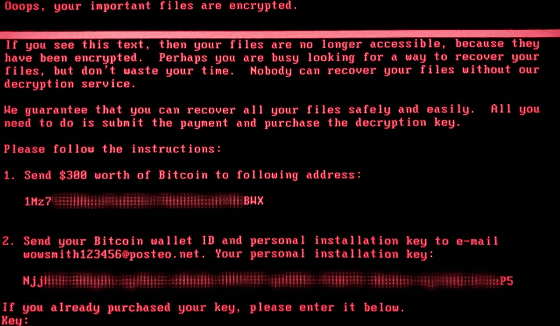
Similar to WannaCry, NotPetya encrypts the entire data when infected with the system, and if you want it to decrypt it, it will cost $ 300 (about 33,000 yen) virtual currencyBitcoin (bit coin)I will give you an indication of transfer. Then, we request that you transmit the bit coin wallet ID and key you received with money after completing the remittance.
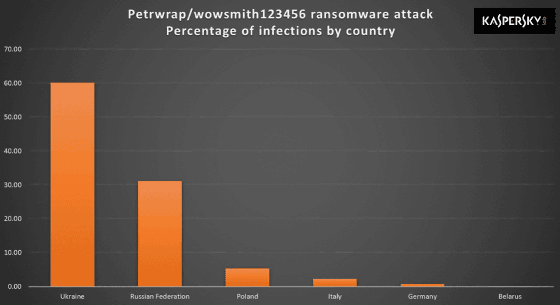
NotPetya is spreading mainly in Europe, and the most serious damage is Ukraine. In addition to central banks, state-run telecommunications companies, subways, airports, POS terminals, ATMs, etc., it also infects the Chernobyl nuclear power plant system. We are in the situation that the radiation monitoring system of nuclear power plant is switched to manual operation.
In addition, the Ukrainian government is seeking calm response from the people, attaching a movie of an animated character that does not move to anything, "There is no need to become a panic.The government copes with this utmost effort to solve this problem I am doing it "Tweet on official publicity Twitter.
Some of our gov agencies, private firms were hit by a virus. No need to panic, we're putting utmost efforts to tackle the issuePic.twitter.com/RsDnwZD5Oj
- Ukraine / Україна (@ Ukraine)June 27, 2017
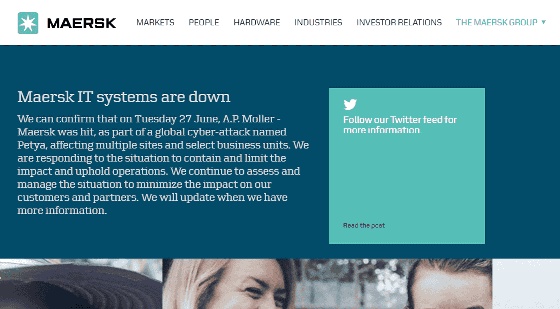
Apart from Ukraine, Maersk, a shipping company in Denmark, Rosnoft, an oil company in Russia, WPP in the UK, and other companies have revealed that they are suffering from NotPetya.
The appearance of NotPetya spreading in the world can be confirmed with CNET's movie.
Nasty Petya ransomware spreading fast (CNET News) - YouTube
According to security researcher's analysis, NotPetya used an attack exploited by Wanna Cry "Eternal BlueIt is thought that it is utilized. This EternalBlue vulnerability attack is a tool that is said to have been developed by the government agency NSA of the United States and the Windows SMBv1 server exploits the security flaw when processing a specific request so that arbitrary Run the code.
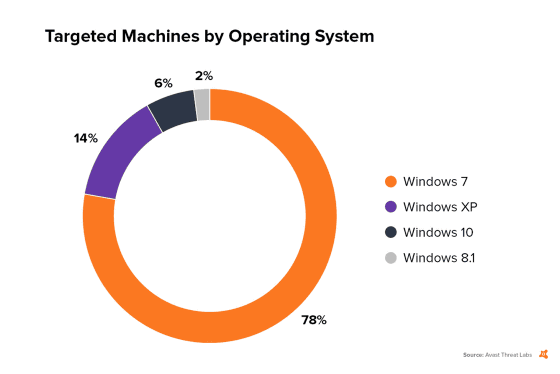
EternalBlue itself has already been fixed with security patches released urgently by Microsoft, but the damage continues to expand due to the existence of a system that has not been blocked by vulnerabilities. According to Avast's survey, 78% of Windows 7, 14% of Windows XP, 6% of Windows 10, and 2% of Windows 8.1 are targeted by NotPetya.
It has also been reported that the infection speed of NotPetya is a phenomenal level. For this reason, it is pointed out that there is a possibility of rapidly spreading within the local network once entering the system.
Spreads SUPER fast - saw org 5K systems hit in under 10 minutes.
- Dave Kennedy (ReL1K) (@ HackingDave)June 27, 2017
Restarts computer with ransom message (MBR).
Avast has confirmed that there are at least 38 million PCs in the world that remain vulnerable to EternalBlue as of the 3rd week of 2017, and the damage could further expand in the future .
Furthermore, it is seen to be behind NotPetyaAttacker's email account blocked by German PostoDid. For this reason, even if remitting "ransom" bit coin it is reported that the encryption cancellation request mail will not be delivered to the attacker, so it is reported that the encryption is no longer canceled.
Related Posts: