What is "super cookie" that ignores the privacy mode of the browser?

In order to browse the website, it is necessary to use web browsers such as Internet Explorer, Google Chrome, Firefox, Safari, etc. In order to protect privacy information, browsing history,Cookie(cookie),temporary fileDo not leavePrivacy modeExist. However, even if you use the privacy mode, you ignore these functions and track the behavior of users "Super cookieA new technique called "Newly created" was created.
Browsing in privacy mode? Super Cookies can track you anyway | Ars Technica
http://arstechnica.com/security/2015/01/browsing-in-privacy-mode-super-cookies-can-track-you-anyway/

Some web browsers such as Chrome and Firefox have a function called privacy mode that does not leave browsing logs, cookies, temporary files etc on the browser. This is "Secret Window" for Google Chrome, "InPrivate Browse" for Internet Explorer, "Private Browsing" for Firefox, "Private Browsing" for Safari, and even with a mobile browser for smartphones These functions are available.
Users who are interested in the privacy side often use the privacy mode to prevent the website from tracking actions or identifying access sources.
However, as a software consultant,RadicalResearchSam Greenhalgh devised a very simple way to invalidate its effect and track the user's behavior even if the user uses the privacy mode. This is a relatively new security mechanism known as "HTTP Strict Transport Security(HSTS) "so that users can trace who is viewing what content from where they are watching, even if the user is browsing with privacy using privacy mode.
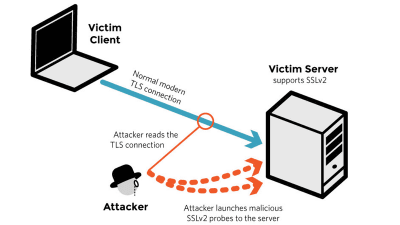
In the first place, HSTS means that in the case of access to the domain currently connected to the web browser by the server,HTTPSIt is a security mechanism that communicates to use. By sending a request to the server, by adding a flag to the header received by the browser, HSTS encrypts the connection with the subsequent website side using the HTTPS protocol. Also, once encrypted, it encrypts all subsequent connections, so it is also a security mechanism that protects users from attacks like downgrade attacks.
However, Sam Greenhalgh has devised a way to track user's behavior even in private mode using this HSTS, named "HSTS super cookie" at the following linkProof of conceptdoing.
RadicalResearch HSTS Super Cookies
http://www.radicalresearch.co.uk/lab/hstssupercookies/
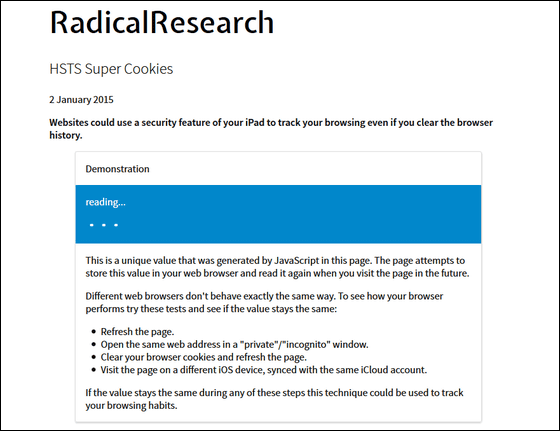
When you access Sam Greenhalgh's published link above, a separate tracking ID is displayed in the blue part for each user. This is automatically generated from the information on the web browser that the user is using. This data is once stored in the browser automatically once it is generated, just the function of cookie itself works.
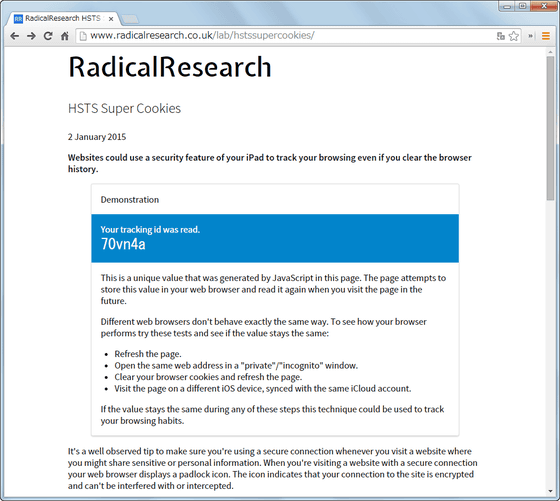
On the page, "Update page" "Open same page in the same browser's normal mode and privacy mode" "Delete browser cookie to update page" "On different iOS devices using the same iCloud account Open the same page "is written, and if the same ID is displayed, it means that browsing is being tracked. Just by updating the page, it is normal for the same ID to be displayed because the cookie is not deleted and readable so it is natural that the same ID is displayed, but if the same ID is displayed in the privacy mode which should not be able to acquire cookie, The cookie on the browser side is read.
Three steps of "Update page", "Open same page in the same browser's normal mode and privacy mode", "Delete browser cookie and update page" tried using Google Chrome, Update "and" Open same page in the same browser's normal mode and privacy mode "did not change the ID, and it was found that the behavior was tracked perfectly even in the private mode.

Super cookie is able to track user's browsing, even if the user is using private mode, unless the user has taken any special measures. However, with the latest version than Firefox 34.0.5, the ID changes as it becomes private mode, so tracking with super cookie is impossible. In addition, as a method for not being tracked by super cookie during web blazing, there is a simple way to say "delete cookie of browser before switching to privacy mode" is introduced.
Related Posts:
in Web Service, Posted by logu_ii