An example in which 99% of Android terminals are affected "Master Key" vulnerability was introduced
Devices equipped with Android OS, such as smart phones and tablets, are in the worldNearly 1 billion units are usedAlthough it is confirmed that a vulnerability in which 99% of these are affected is being exploited, it is reported by Symantec.
First time confirming an Android "Master Key" vulnerability exploit first | Symantec Connect Community
http://www.symantec.com/connect/ja/blogs/android-18
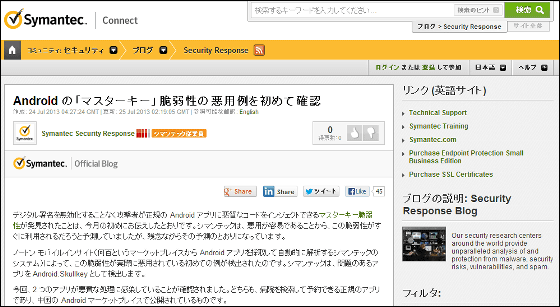
For Android applications, you need a digital signature to prove that "the code is provided by the official issuer", and when you run the application, "This application will exercise these rights, but OK Do you have permission? " However, it is clear in the beginning of July that there is a vulnerability to hide malicious code in a regular application without falsifying the information of this digital signature, and to be able to execute the function through the authority acquired by the regular application It was done.
Uncovering Android Master Key That Makes 99% of Devices Vulnerable »Bluebox Security
http://bluebox.com/corporate-blog/bluebox-uncovers-android-master-key/
At this point, Symantec has examined, there are many applications that have not used an exploit vulnerability, but use it unintentionally. I was calling for implementation extremely simple and dangerous by affecting 99% of Android terminals, indeed around 900 million, but unfortunately it appeared as expected .
According to Symantec, the vulnerability has been exploited to embed malicious code is an application for Chinese users, six have been confirmed so far. If malicious code hidden behind these applications is executed, the terminal may be controlled remotely, important information such as a phone number may be stolen, and furthermore, the mobile security application will be invalidated.
Example of application
At the moment, it seems that things that have targeted Japanese users have not appeared yet, but it seems that it will take a considerable amount of time for patches to come from each terminal manufacturer or carrier.
Related Posts:
in Software, Smartphone, Posted by logc_nt