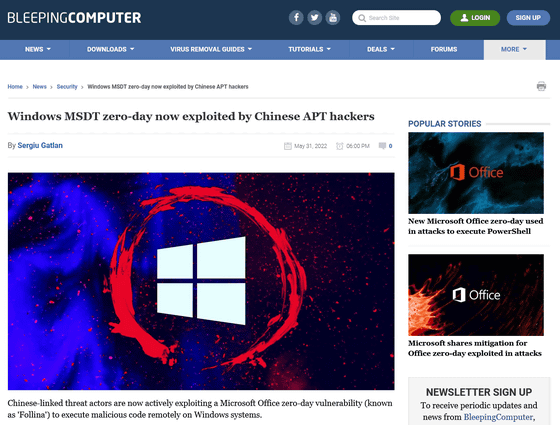
China-related threat actors are exploiting the zero-day vulnerability 'Follina' found in Microsoft's diagnostic tools

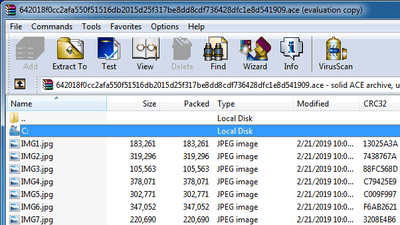
A zero-day vulnerability, commonly known as 'Follina,' which enables remote code execution via the diagnostic tool 'Microsoft Support Diagnostic Tool (MSDT)' simply by opening or previewing a Word document, is a threat actor related to China. Has been reported to be abused.
Windows MSDT zero-day now exploited by Chinese APT hackers
Microsoft shares mitigation for Office zero-day exploited in attacks
https://www.bleepingcomputer.com/news/microsoft/microsoft-shares-mitigation-for-office-zero-day-exploited-in-attacks/
Follina — a Microsoft Office code execution vulnerability | by Kevin Beaumont | May, 2022 | DoublePulsar
https://doublepulsar.com/follina-a-microsoft-office-code-execution-vulnerability-1a47fce5629e
'Follina' is a common name given by researchers who analyzed the file, and the identifier given by Micorosft is 'CVE-2022-30190'.
This zero-day vulnerability was first reported to Microsoft on April 12, 2022 by crazyman_army. According to crazyman_army, a Micorosft representative replied, 'We have determined that this is not a security issue.'
It says pic.twitter.com/Z2AN7nq6hr
— Crazyman_army (@CrazymanArmy) May 30, 2022
— Crazyman_army (@CrazymanArmy) May 30, 2022
In May, it was confirmed that this vulnerability was used by a Chinese-related threat actor 'TA413' to attack the international Tibetan community.
As a workaround, Microsoft has listed a way to disable the MSDT protocol.
As a method, start a command prompt with administrator privileges, execute 'reg export HKEY_CLASSES_ROOT \ ms-msdt ms-msdt.reg' to back up the registry key, and then 'reg delete HKEY_CLASSES_ROOT \ ms-msdt / f'. Will disable the protocol.
If you want to enable it, you can restore the previous backup with 'reg import ms-msdt.reg'.
Related Posts:
in Security, Posted by logc_nt