Researchers discover flaws in Amazon and Google's DNS services, leaving important company information missing
Black Hat 2021: DNS loophole makes nation-state level spying as easy as registering a domain | Wiz Blog
https://www.wiz.io/blog/black-hat-2021-dns-loophole-makes-nation-state-level-spying-as-easy-as-registering-a-domain
Amazon and Google patch major bug in their DNS-as-a-Service platforms --The Record by Recorded Future
https://therecord.media/amazon-and-google-patch-major-bug-in-their-dns-as-a-service-platforms/
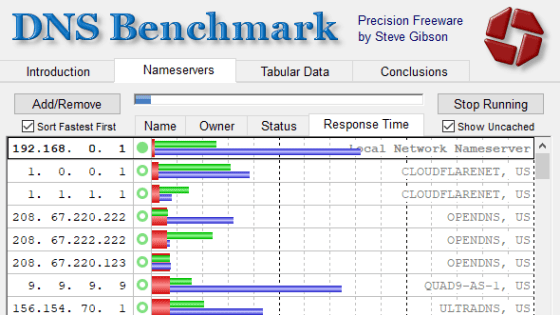
DNS services such as Amazon's Amazon Route 53 and Google's Cloud DNS reduce the burden of managing your own DNS servers and software, and also offer benefits such as increased redundancy and reliability. Companies that use DNS services typically register their internal domain name with a DNS server when signing up. Once this is done, corporate employees will query the hosted DNS server for their IP address when they visit internal pages.
DNS service users can register any domain name, but Wiz researchers have discovered that some DNS services allow you to specify the 'domain name of the DNS server itself provided'. did. In fact, when researchers specified the domain name of a large number of DNS servers owned by Amazon Route 53, they were able to partially hijack the DNS server and receive a huge amount of DNS traffic.
The DNS traffic that could be received was about dynamic DNS updates on Windows machines to automatically keep DNS records up-to-date when the IP address changed. It seems that this function is mainly used in large networks that host internal services and have its own internal server, and said that the traffic received this time also included important corporate information. ..
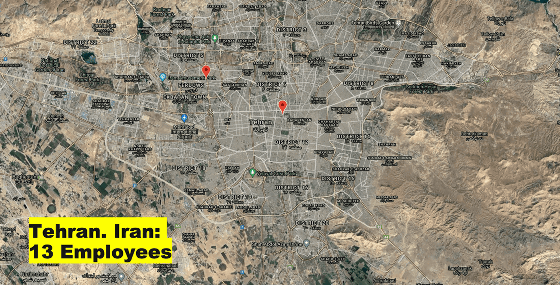
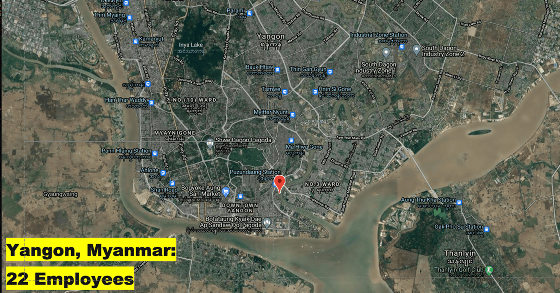
During the 14-hour test period, researchers received information from a total of more than 15,000 institutions and companies, including 45 US government agencies, 85 international organizations, and large Fortune 500 companies. This information contained a wealth of information such as IP addresses, computer names, employee names, and office locations. For example, the image below maps the location of an office or employee of a large company where a researcher intercepted DNS traffic. In this way, in addition to being able to investigate the scope of corporate activities in detail ...
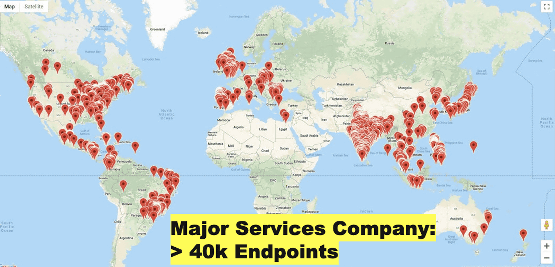
In countries such as Iran and Myanmar, which are subject to sanctions by the Office of Foreign Assets Control (OFAC) of the US Treasury, it was possible to identify companies that appear to be illegally conducting business activities. It is also possible that intelligence agencies could use these data to look at the connections between companies and government agencies to identify companies that act as government contractors.
Researchers are aware of this issue with three DNS services, including Amazon Route 53 and Google's Cloud DNS, and Amazon and Google have already updated and addressed it, and the remaining one DNS service is also patching. And that. In addition, researchers believe that as many as 12 DNS services may be vulnerable to similar attacks.
Regarding this issue, researchers point out that not only the DNS service but also Microsoft's default option, which allows DNS dynamic updates to pass through the local network and reach the Internet, is also a problem. When foreign media The Record contacted Microsoft about the matter, a spokeswoman said he recommended that companies follow the guidance below.
How to configure DNS dynamic updates on the server Windows --Windows Server | Microsoft Docs
https://docs.microsoft.com/en-us/troubleshoot/windows-server/networking/configure-dns-dynamic-updates-windows-server-2003
Related Posts:
in Web Service, Security, Posted by log1h_ik