The possibility that it is easy to break through the password by letting AI guess the password

byDennis M 2
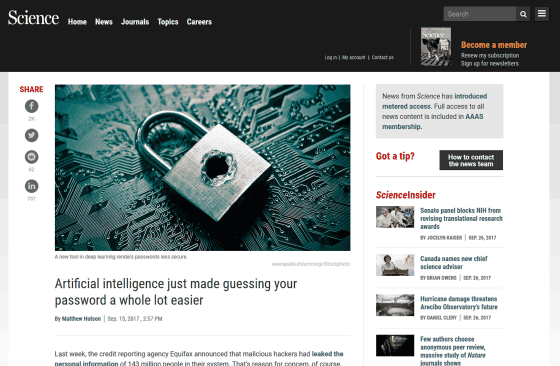
In order not to let out important informationDo not set an easy passwordAlthough countermeasures such as measures are being done, new studies have indicated the possibility that an attacker can easily guess the target password by using artificial intelligence.
[1709.00440] PassGAN: A Deep Learning Approach for Password Guessing
https://arxiv.org/abs/1709.00440
Artificial intelligence just made guessing your password a whole lot easier | Science | AAAS
http://www.sciencemag.org/news/2017/09/artificial-intelligence-just-made-guessing-your-password-whole-lot-easier
A method of "guessing a password in artificial intelligence" has been developed for a long time, and in addition to a brute force method of merely combining a random character string until it coincides with a password which becomes a correct answer, a method of forcibly deleting a password from a password leaked in the past There are also ways to guess the generation method. By combining these methods, depending on the website90% accuracy or betterIt is said that passwords can be guessed with, but you have to keep coding manually for several years before doing the attack.
On the other hand,Stevens Institute of TechnologyResearchers succeeded in raising this speed by using deep learning. Researchers used Generative Advisory Networks (GAN) which use two neural networks "generator" and "discriminator". In GAN, generator generates an artificial image that is similar to the training data, discriminator identifies whether the image is an image of the generated a generator whether the training data. By repeating this, the generator will be able to create images closer to the training data.
Giuseppe Ateniese who conducted the study compared the relationship between the generator and the discriminator to the relationship between counterfeiters and the police, and as the ability to identify the police increases, the counterfeiters raise their arms so that the works can not be distinguished It is similar to going on.
The research team created a GAN called "PassGAN" and made PassGAN learned with tens of millions of passwords that flowed out from the game site. After that, let PassGAN generate several hundreds of new passwords, and count how many generated passwords coincide with the password that flowed out from LinkedIn. At this time, the result was compared with the results of the password search program "John the Ripper" and "hashCat".
As a result of the test, in the case of only PassGAN, the probability of matching Password on LinkedIn is 12%. Meanwhile, the match rate of passwords generated by the comparison target program is 6 to 23%. In other words, when using PassGAN alone, the match rate is not high so far, but it turned out that by combining PassGAN and hashCat, the matching rate is increased to 27%.

byWorld's Direction
Martin Arjovsky, a researcher at computer science at New York University, said the study revealed that "crackers can gain great advantage by adapting simple machine learning". On the other hand, it is pointed out that similar results can be obtained by assisting hashCat with simpler machine learning without using GAN. In this regard, Mr. Ateniese is planning to investigate before peer reviewing.
However, Mr. Ateniese is PassGAN at this stage only to aid hashCat, but I see that I can cross hashCat by iterating learning. hashCat obeys certain rules and can generate up to 650 million passwords by itself, but PassGan is able to create rules infinitely because it is possible to create rules themselves.

byJay Wennington
"AlphaGo has devised a strategy that experts could not think of.This also suggests that if we give enough data to PassGAN we can create rules that human beings could not think of "Arjovsky says.
Related Posts: