What is the structure of China's net new weapon · big gun "The Great Cannon"

BySpolster
It occurred in March 2015The biggest DDoS attack on history to GitHubAlthough the site has failed for five days, it has been pointed out that the organization of the Chinese government level is involved in the background of this attack. Under such circumstances, a report released by cybersecurity-related companies is that an organization that is suspected of involvement by the Chinese government in a large-scale cyber attack mainly conducted in the Asia-Pacific region "APT 30"Is involved,"The Great Cannon"The existence of a net attack system called" It was revealed.
APT 30 and the Mechanics of a Long-Running Cyber Espionage Operation «Threat Research | FireEye Inc
https://www.fireeye.jp/blog/threat-research/2015/04/apt_30_and_the_mecha.html
China's Great Cannon
https://citizenlab.org/2015/04/chinas-great-cannon/
Based on the US-based cyber security company that created the report "FireEye"About 70 pages of reports(PDF file), the company "APT 30(Advanced Persistent Threat: an advanced and strong threat) ", it is clear that domestic organizations in China are conducting company spy activities and attacking target companies. Targeted companies and organizations are only found in India, Malaysia, Vietnam, Thailand, Nepal, Singapore, the Philippines, Indonesia, and even in ASEAN countries including Japan, similar attacks It is suspected that it is being done, and the background is pointed out the existence of evidence indicating that the Chinese government is involved. Also, we know that this attack has been ongoing since 2005.

About the situation, Fire Eye's Asia Pacific CTO · Bryce Boland said, "Although there is no" immovable evidence "to show the involvement of the Chinese government, all signs point to China," said the government level It suggests that a large organization of involved is involved. And "In the Asian region, the development of intellectual property is done at tremendous momentum, and this is the new battlefield," he says.
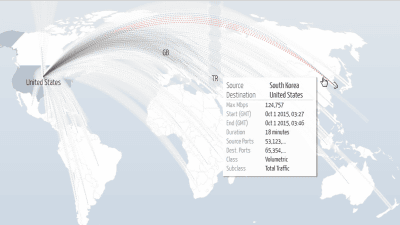
Also, at the University of Toronto · Munk School of Global AffairsCitizen Lab's revealed investigationIt occurred on 26th the same day as the DDoS attack on GitHub which was held on March 16Attacks on GreatFire.orgIs targeted to the page of GitHub hosted by the site. In the targeted page, it is thought that the file concerning technology to avoid the censorship system in China is placed and it was an attack to try to disturb it. In the investigation by GreatFire.org, malicious malware returned from Baidu's server is used for attacks, but Baidu denies that the company's server is infected by someone.
◆ China's Internet censorship system "Kin Shield" and attack system "Great Cannon"
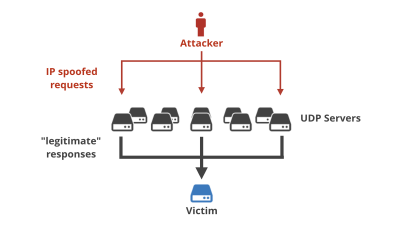
You can censor information on the net in China and block inconvenient informationGreat FirewallIt is already well known that there is a censorship system called Kim (Shinchi), but the mechanism of attack that can be said to be a dualist "Great CannonThe existence of "is becoming clear. Great Cannon takes over traffic for a specific IP address and replaces its contents as desiredMan-in-the-middle attackIt seems to have the ability to do.
Its motion image looks like the figure below.

As shown by "TAP" in the figure, all the net environments in China are "wiretapped" by Kim Shik (= government)Falun Gong"Or"TiananmenIf you put a prohibited keyword such as "You are searching for the user and the other siteRST packetMeasures such as forcibly stopping the communication by sending it are taken. This is the "defensive capability" provided for Kim shield.

On the other hand, Great Cannon has "attack capability" of redirecting to another site by hijacking communication itself and sending a malicious JavaScript file created for attack to make it the steppingstone of attack.

System screens and operation manual etc are all written in Chinese. Also in this regard, FireEye points out that the possibility of Chinese involvement is extremely high.

Although the Chinese censorship system of China that established its own Internet environment had so far had a "defense" attitude so far, this time the newly revealed Great Cannon has the opposite ability of "attack" What you can say. Given the DDoS attack on GitHub as an example, if you got the ability to attack against an unfortunate opponent, it is unlikely that new concerns will spread.
Related Posts:
in Note, Posted by darkhorse_log