There are a number of problems that have emerged when looking at the security system of the airport with a hacker perspective

ByAnne Worner
Since the simultaneous terrorist attacks in 2001, security has been strengthened especially at the airport in the US, but it was introduced at that timeEven with a whole-body fluoroscopic scanner that can be seen in pants, it can easily pass with holding weaponsThe problem is clear. Various problems are becoming apparent as a result of examining the inspection equipment of such airports from the hacker's perspective.
BlackHat Review: Pulling back the curtain on Airport Security: Can a weapon get past TSA? | Alert Logic
https://www.alertlogic.com/blog/blackhat-review-pulling-back-the-curtain-on-airport-security-can-a-weapon-get-past-tsa/
This information is an international conference on information security held in Las Vegas, USA from August 2 to 7Black Hat USA 2014Those announced in. The characteristic of this conference is to think security from the perspective from the attacker's side, and it is a place to exchange information on various security technologies and equipment.
Black Hat USA 2014
https://www.blackhat.com/us-14/
The survey result was announced as a person named Billy Rios, and its presentation materials are published in PDF.
BH 2014 - Billy - Rios.pdf
(PDF file: 7.6 MB)http://xs-sniper.com/blackhat2014/BH2014-Billy-Rios.pdf
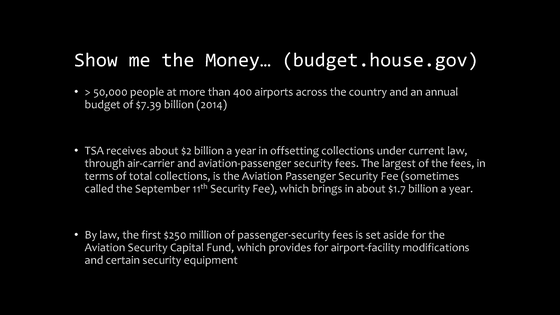
According to the American House Budget Committee, more than 50,000 staff are currently working at over 400 major airports in the US, and budget of 7,390 million dollars (about 770 billion yen) is spent annually . further,TSA(The American Transportation Security Agency) is supplemented with budget of 2 billion dollars (about 208 billion yen) annually by law, and it seems that the security fee paid by airline and passengers is financed. Among them, Aviation Passenger Security Fee (air passenger security fee), which is often referred to as "911 security fee", amounts to as much as $ 1.7 billion (about 177 billion yen).
Mr. Rios revealed that the equipment used for inspection at the airport baggage inspection siteSecurity holeThere is a danger that if you exploit this, dangerous goods such as explosives can be brought into the cabin without being perceived. However, when Mr. Rios consulted the authorities on this security problem, the response was such that "Our system never gets hacked or deceived" or "I'm protecting with my own countermeasure software" It is said that it returned.
Mr. Rios as "TSA's problem" I do not know the problem existing in software "and" I grasp the problem and take measures, but I do not inform the vendor who developed the system, We point out that vulnerabilities to attacks and possibly other government agencies may be left in a state of crisis.
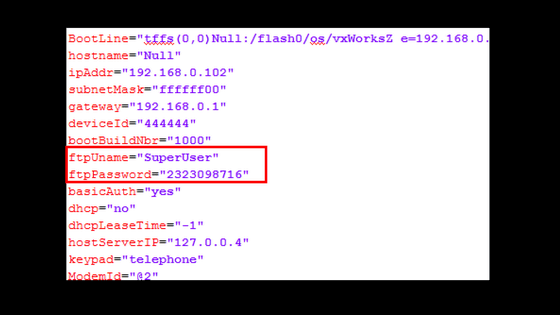
◆ The existence of backdoor
First of all, it is the representative of the security holeback doorIs left. "There is a malicious account by a third party" as the type of backdoor "Account for debugging left as it is no longer needed" "For the engineer created for service and maintenance Three accounts "are listed.
Accounts for engineers in particular often become backdoors. The cause is "The account itself is softwareHard codingIt is in "what is being done" and the operation of the software is controlled by that password.
Problems of the account exist "There are times when it can be seen by a third party", "Even if the user tries to change (for security), it can not be rewritten").
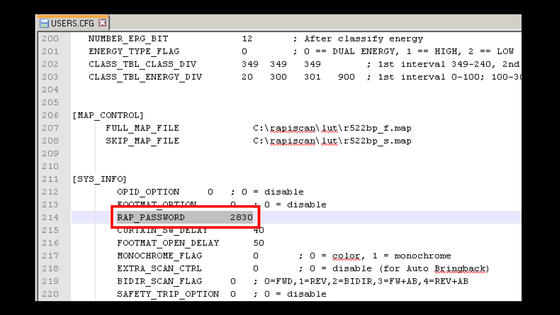
Also, in many cases the problem is that the password is a simple list of numbers. In a survey conducted by Mr. Rios, many simple passwords such as "1234" and "0011" have been found.
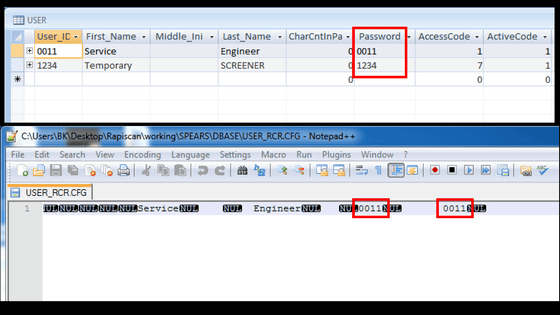
A service called "Super User" has been found in the account for the service, and using this account will make everything possible.
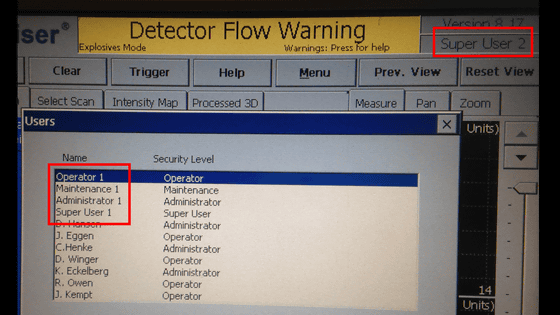
And it is found that this Super User's password is also an enumeration of numbers.
Also, there are cases that the backdoor opens in terms of hardware. The picture below shows the state that the LAN cable connected to the inspection equipment is visible from the outside. If you connect a PC etc. to this cable, it seems that it is also possible to take over the inspection equipment.

◆ Security hole in equipment
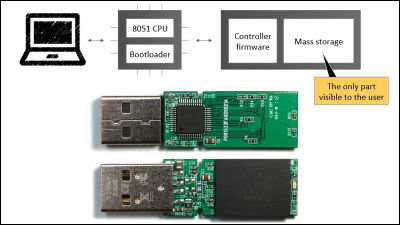
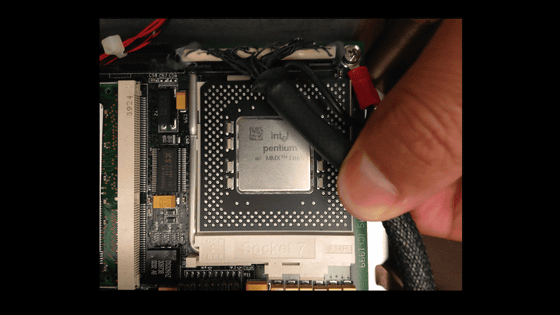
This is a picture of the board built in the inspection machine.
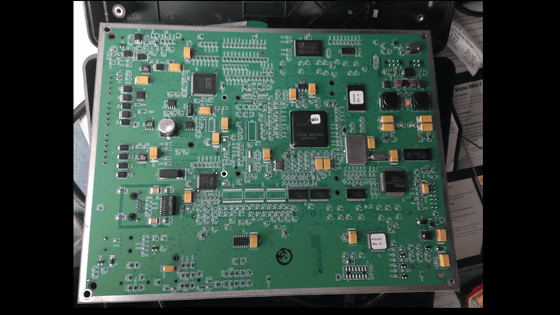
Mr. Rios doubts that it is the equipment of "Made in China".
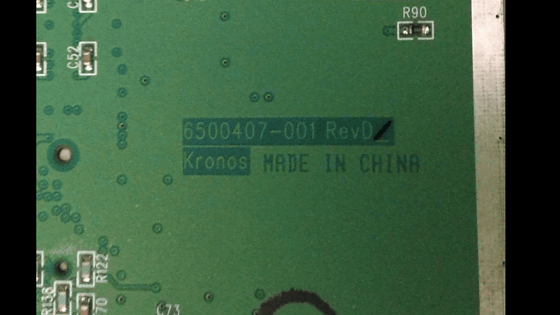
He pointed out that this point is also a risk because it was discovered that malware was sneaked into chips made in China beforehand and a chip that intercepts Wi - Fi was secretly installed, etc. It is.
Also, many of the facilities have been using Windows 3.x series of operating systems, and recently it has just been updated to Windows XP.
At the moment that Microsoft has already ended its support, it can be said that the dangerous behavior of keeping using Windows XP is dangerous.
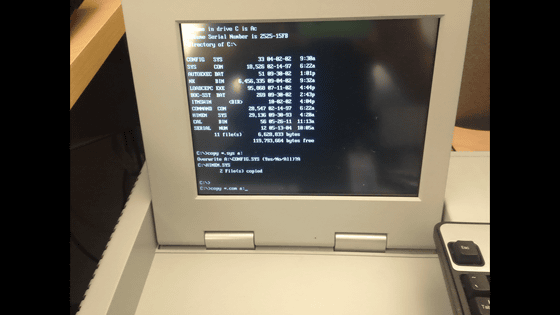
A screen that seems to be running or under maintenance. The DOS screen which almost never seems to be seen now is displayed, it shows a considerably outdated appearance.
There seems to be a device which has CPU mounted in "Pentium with MMX technology" which was mainstream in the 1990s.
In response to this situation, Mr. Rios advises "Trust but Vefify the Engineering" even if you put trust.
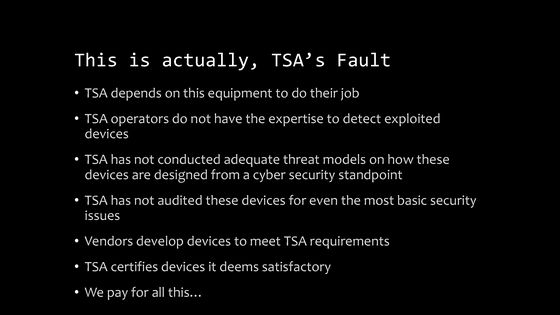
And Rios asserts that "TSA is responsible for this issue". Does not have knowledge about equipment, security measures are insufficient, vendors who delivered equipment are manufactured based on the specifications set by TSA, there is no problem, and that TSA will I regard it as "meeting the criteria" and approve it for reasons.
Related Posts: