Microsoft uses AI tool Security Copilot to discover unknown vulnerabilities in open source boot loaders such as GRUB2, U-Boot, and Barebox
Microsoft has reported that a new analysis method using its proprietary AI tool, Security Copilot, has found new vulnerabilities in open source boot loaders such as GRUB2, U-Boot, and barebox. This effort is part of the use of AI in the security field, focusing on the analysis of low-level software, particularly firmware and boot loaders, which are often overlooked in normal security scans.
Analyzing open-source bootloaders: Finding vulnerabilities faster with AI | Microsoft Security Blog
Microsoft uses AI to find flaws in GRUB2, U-Boot, Barebox bootloaders
https://www.bleepingcomputer.com/news/security/microsoft-uses-ai-to-find-flaws-in-grub2-u-boot-barebox-bootloaders/
Microsoft says it has identified previously undiscovered vulnerabilities in the open source boot loaders GRUB2, U-Boot, and Barebox. The 20 vulnerabilities discovered are as follows:
| Vulnerability | ||
|---|---|---|
| GRUB2 | CVE-2024-56737 | HFS strcpy buffer overflow |
| CVE-2024-56738 | Side-channel attacks using non-constant-time cryptographic comparisons | |
| CVE-2025-0677 | Integer overflow in UFS symbolic link handling | |
| CVE-2025-0678 | Buffer overflow in Squash4 read | |
| CVE-2025-0684 | ReiserFS symlink handling overflow | |
| CVE-2025-0685 | JFS symbolic link handling overflow | |
| CVE-2025-0686 | RomFS symbolic link handling overflow | |
| CVE-2025-0689 | UDF block processing out of bounds read | |
| CVE-2025-0690 | Out-of-bounds write in read command | |
| CVE-2025-1118 | Arbitrary memory reading using the dump command | |
| CVE-2025-1125 | Buffer overflow when opening HFS compressed files | |
| U-Boot | CVE-2025-26726 | SquashFS directory table parsing buffer overflow |
| CVE-2025-26727 | SquashFS inode parsing buffer overflow | |
| CVE-2025-26728 | SquashFS nested file read overflow | |
| CVE-2025-26729 | EroFS symlink processing buffer overflow | |
| Barebox | CVE-2025-26721 | Buffer overflow in storage during file creation |
| CVE-2025-26722 | SquashFS symlink resolution overflow | |
| CVE-2025-26723 | EXT4 symbolic link resolution overflow | |
| CVE-2025-26724 | CramFS symlink resolution overflow | |
| CVE-2025-26725 | Buffer overflow when parsing directory entries in JFFS2 | |
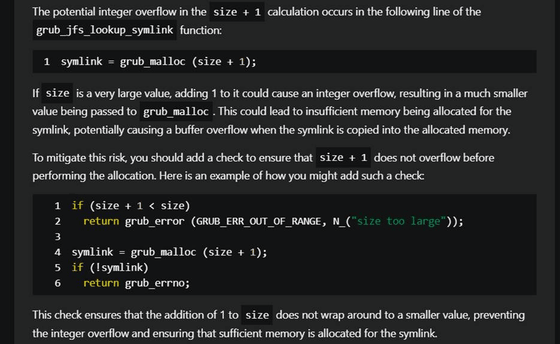
In particular, 11 vulnerabilities were discovered in GRUB2, including integer overflows and buffer overflows in the file system parser, flaws in command processing, and the possibility of side-channel attacks in cryptographic comparisons.
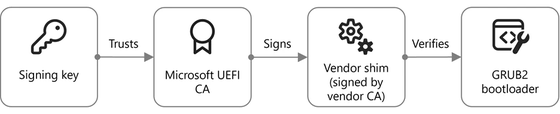
In addition, buffer overflows were discovered in U-Boot and Barebox that occur when analyzing file systems such as SquashFS, EXT4, CramFS, and JFFS2, as well as symbolic links. Although physical access is required, these vulnerabilities pose a risk of bypassing UEFI Secure Boot under certain conditions and allowing arbitrary code to be executed.
To discover these vulnerabilities, Microsoft revealed that it combined static code analysis tools such as CodeQL, fuzzing using the GRUB2 emulator, manual code analysis, and its proprietary AI tool, Security Copilot. Microsoft argues that 'Security Copilot has been shown to be effective in identifying potential vulnerabilities in areas such as networking, file systems, and cryptographic signatures.'
The company said it has been working with the open source community to report and fix the vulnerabilities, and encourages users and developers to apply relevant security updates to ensure the security of their systems.
Related Posts: