An attack that exploits the zero-day vulnerability 'Log4Shell' in the Java library that shakes the world has already started before it was discovered.

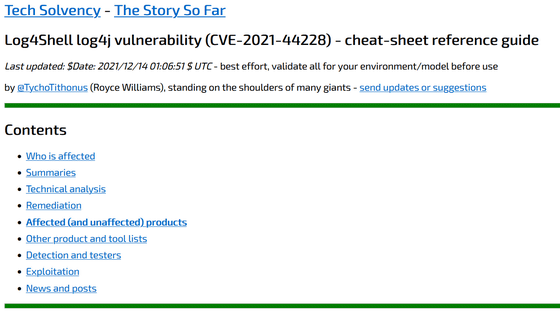
A proof-of-concept code for the zero-day vulnerability ' Log4Shell ( CVE-2021-44228 ) ' in Java's log output library, Apache Log4j , was released on December 10, 2021 Japan time. There are various confirmation reports of the exploit that enables remote code execution by poking this Live4Shell, but it turned out that this Log4Shell exploit was done from December 1st to 2nd before the proof-of-concept code was released. Did.
Log4Shell attacks began two weeks ago, Cisco and Cloudflare say --The Record by Recorded Future
https://therecord.media/log4shell-attacks-began-two-weeks-ago-cisco-and-cloudflare-say/
Log4Shell is due to a function called JNDI Lookup included in Log4j, which is a zero-day vulnerability that 'it is possible to load a class file on any LDAP server by sending a specially crafted string and recording it as a log'. It is sex. By exploiting this, it is possible to make a program using Log4j execute arbitrary code.
Why does the vulnerability 'Log4Shell (CVE-2021-44228)' found in Java's Log4j library have a major impact on the world? --GIGAZINE

There have already been a large number of reports of exploits piercing this Log4Shell, and there is no time to enumerate, such as installing virtual currency miners, spreading botnets, scanning server OS and user information.
Log4j library zero-day vulnerability 'Log4Shell' is attacking vulnerable servers one after another, and you can do whatever you want with cryptocurrency miner installation, botnet spread, data theft, etc. --GIGAZINE

According to Matthew Prince, CEO of Cloudflare, a CDN service company, the first log4Shell exploit to date was recorded at 4:36:50 UTC on December 1, 2021. .. Prince said that until the proof-of-concept code was released on December 10, there didn't seem to be a lot of exploits. However, there was someone who knew Log4Shell nine days before the proof-of-concept code was released.
Earliest evidence we've found so far of # Log4J exploit is 2021-12-01 04:36:50 UTC. That suggests it was in the wild at least 9 days before publicly disclosed. However, don't see evidence of mass exploitation until after public disclosure.
— Matthew Prince ???? (@eastdakota) December 11, 2021
In addition, Cisco Talos , a group of network threat experts, said, 'We have confirmed the activity of attackers related to CVE-2021-44228 (Log4Shell) since December 2, 2021, but unverified reports. According to the report, the threat activity itself was also on December 1. Companies and organizations have expanded their scope of analysis at least a few weeks ago, taking into account the possibility that the attack had taken place earlier. I highly recommend that you do it. '
Cisco Talos Intelligence Group --Comprehensive Threat Intelligence: Threat Advisory: Critical Apache Log4j vulnerability being exploited in the wild
https://blog.talosintelligence.com/2021/12/apache-log4j-rce-vulnerability.html
The Log4j library is so widely used that the impact of Log4Shell is enormous. Apache has already released version 2.15.0 that fixes the vulnerability, but it may not be possible to update depending on the JAVA runtime environment, so it can be said that it will take time to resolve. The threat intelligence service Kryptos Logic reports that more than 10,000 vulnerable hosts were found as a result of running the Log4Shell checker.
Kryptos Logic's log4j (CVE-2021-44228) scanner discovered more than 10,000 vulnerable host using simple HTTP header probing. As always, you can register for free vulnerability notification on https://t.co/kiZvKnnMXv . co / QnkGnp9SCx pic.twitter.com/g18eF2JsGm
— Marcus Hutchins (@MalwareTechBlog) December 12, 2021
In addition, IPA and JPCERT / CC also stated that they confirmed communications attempting to abuse Log4Shell in Japan, and recommend that they immediately consider upgrading Log4j and applying workarounds.
About Apache Log4j Vulnerabilities (CVE-2021-44228): IPA Information-technology Promotion Agency
https://www.ipa.go.jp/security/ciadr/vul/alert20211213.html
Alert regarding Arbitrary Code Execution Vulnerabilities in Apache Log4j (CVE-2021-44228)
https://www.jpcert.or.jp/at/2021/at210050.html
Related Posts:
in Software, Web Service, Security, Posted by log1i_yk