Log4j library zero-day vulnerability 'Log4Shell' is attacking vulnerable servers one after another, and you can do whatever you want, such as installing virtual currency miners, spreading botnets, and stealing data.

A zero-day vulnerability ' Log4Shell (CVE-2021-44228) ' for remote code execution was discovered on December 10, 2021 in the Java log output library ' Log4j' used in various programs, causing great confusion. Is calling. Apache, which releases Log4j, has released version 2.15.0, which resolves the vulnerability, but there have already been reports of exploits that exploited Log4Shell.
Hackers start pushing malware in worldwide Log4Shell attacks
https://www.bleepingcomputer.com/news/security/hackers-start-pushing-malware-in-worldwide-log4shell-attacks/
Microsoft: Log4j exploits extend past crypto mining to outright theft | VentureBeat
https://venturebeat.com/2021/12/12/microsoft-log4j-exploits-extend-past-crypto-mining-to-outright-theft/
Log4Shell is a vulnerability found in the feature 'JNDI Lookup' that has been included since version 2.0 beta 9 of Log4j, which dynamically reads a class file from any LDAP server with a specific input, so it is easy to malicious code. Was able to be executed.
Why does the vulnerability 'CVE-2021-44228' discovered in Java's Log4j library have a great impact on the world? --GIGAZINE

The following movie is a video demonstrating Log4Shell.
Log4shell | Remote Code Execution | 0day | CVE-2021-44228 | POC --YouTube
According to Bleeping Computer, an IT news site, there is a report of an example of executing a shell script that forcibly installs a virtual currency miner with Log4Shell immediately after Log4Shell is released. Bleeping Computer says it has identified an exploit that removes competing malware from the attacked device, then installs the container-targeted malware Kinsing and initiates cryptocurrency mining. Netlab 360 , a network security research firm, also reported a move to bring Linux devices to botnets such as Mirai and Mustik to install cryptocurrency miners and perform large-scale DDoS attacks.
this log4shell payload is ... a coin miner
— Kevin Beaumont (@GossiTheDog) December 10, 2021
the vulnerability has arrived pic.twitter.com/XUR7I5ydpP
Verification by security researchers has confirmed that vulnerable servers can access URLs and make DNS requests to callback domains. It is also reported that Log4Shell was used to successfully leak environment variables including server data such as host name, user name, OS and its version number without permission.
In addition, the Log4Shell exploit from the domain psc4fuel.com was confirmed on the Bleeping Computer web server. It's unclear whether this attack was by a security researcher or a malicious attacker, but pc4fuel.com was originally the domain of an oil service company, spoofing and exploiting it. It states.
Cloudflare, a CDN service company, seems to deploy a firewall to block HTTP requests related to JNDI Lookup. Cloudflare has already reported about 20,000 exploit requests per minute as of December 11. There are also reports on Twitter that we have observed the Log4Shell exploit.
???? ⚠️ New # 0-day vulnerability tracked under 'Log4Shell' and CVE-2021-44228 discovered in Apache Log4j ???? ️‼ ️ We are observing attacks in our honeypot infrastructure coming from the TOR network. Find Mitigation instructions here: https://t.co/tUKJSn8RPF pic.twitter.com/WkAn911rZX
— Deutsche Telekom CERT (@DTCERT) December 10, 2021
We are also observing # log4shell of # log4j on our dead server. It came more than I expected, and I see it in addition to URLs and UAs. #Honeypot observation (not exactly honeypot) pic.twitter.com/AxY2IZ8EAm
— S-Owl (@Sec_S_Owl) December 13, 2021
As a workaround for Log4Shell, you are required to update Log4j to version 2.15.0. However, since the operating environment of version 2.15.0 is Java 8, it is recommended to 'disable JNDI Lookup' and 'delete the JNDI Lookup class file' if you cannot update immediately in an environment prior to Java 7. It has been.
Jen Easterly, director of the US Cybersecurity and Infrastructure Security Agency (CISA), said on December 11, 2021, 'CISA will work closely with public and private partners to impact products that include the Log4j library. Actively tackle the issue of giving Log4Shell. ' 'Frankly, this vulnerability poses a serious risk. Government and private companies can work together to minimize the potential impact. We are all. We urge your organization to participate in this important effort and take action. '
Statement from CISA Director Easterly on “Log4j” Vulnerability | CISA
https://www.cisa.gov/news/2021/12/11/statement-cisa-director-easterly-log4j-vulnerability
CISA recommends three emergency measures for businesses and organizations:
-List all externally connected devices that have programs that use Log4j installed.
• Make sure that the Security Operation Center (SOC) responds to the device alerts listed above.
-Introduce an automatically updated web application firewall to narrow down alerts that SOC should focus on.
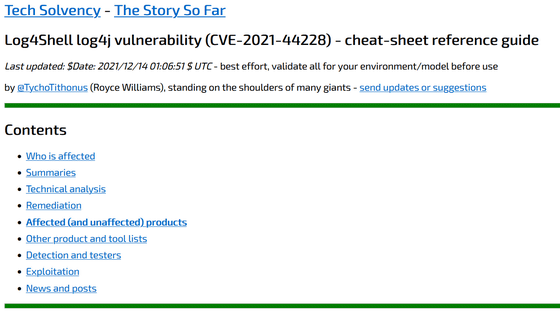
The Log4Shell security advisory is summarized on the following page.
BlueTeam CheatSheet * Log4Shell * | Last updated: 2021-12-12 2204 UTC · GitHub
https://gist.github.com/SwitHak/b66db3a06c2955a9cb71a8718970c592
In addition, cyber security company Silent Signal is developing 'a tool for discovering vulnerable hosts affected by Log4Shell' as open source, and the source code is published on GitHub under the GPLv3 license.
Our new tool for enumerating hidden Log4Shell-affected hosts – Silent Signal Techblog
https://blog.silentsignal.eu/2021/12/12/our-new-tool-for-enumerating-hidden-log4shell-affected-hosts/
In addition, cyber security company Cybereason has developed 'Logout4Shell', which is a 'vaccine' approach to 'use Log4Shell to apply patch for fixing vulnerabilities', and has released it on GitHub. Cybereason states that this Logout4Shell is only an exploit for vulnerabilities, and it is illegal to run it on a server managed by another person and it is not recommended at all.
Cybereason Releases Vaccine to Prevent Exploitation of Apache Log4Shell Vulnerability (CVE-2021-44228)
https://www.cybereason.com/blog/cybereason-releases-vaccine-to-prevent-exploitation-of-apache-log4shell-vulnerability-cve-2021-44228
Related Posts:
in Video, Software, Web Service, Security, Posted by log1i_yk