Microsoft and Intel announce the ability to protect devices from 'cryptojacking' that mines cryptocurrencies on their own

Microsoft and Intel 2021 April 26, is a security platform for enterprise
Defending against cryptojacking with Microsoft Defender for Endpoint and Intel TDT --Microsoft Security
https://www.microsoft.com/security/blog/2021/04/26/defending-against-cryptojacking-with-microsoft-defender-for-endpoint-and-intel-tdt/
Intel Collaborates with Microsoft against Cryptojacking :: Intel Corporation (INTC)
https://www.intc.com/news-events/press-releases/detail/1461/intel-collaborates-with-microsoft-against-cryptojacking
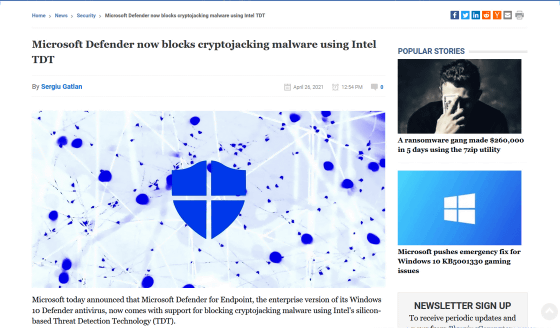
Microsoft Defender now blocks cryptojacking malware using Intel TDT
https://www.bleepingcomputer.com/news/security/microsoft-defender-now-blocks-cryptojacking-malware-using-intel-tdt/
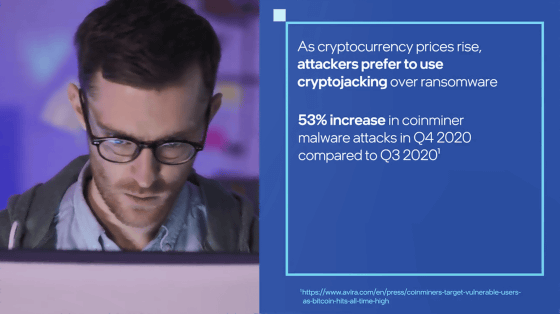
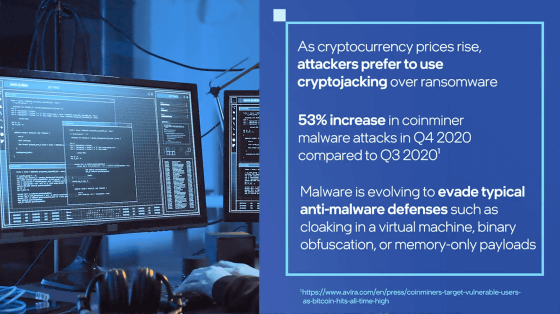
In recent years, under the influence of soaring prices of virtual currencies such as Bitcoin, malware that executes 'cryptjacking' to mine virtual currencies using third party devices is increasing rapidly. That thing. Malware that performs cryptojacking is becoming more sophisticated and harder to detect to circumvent typical malware defenses.
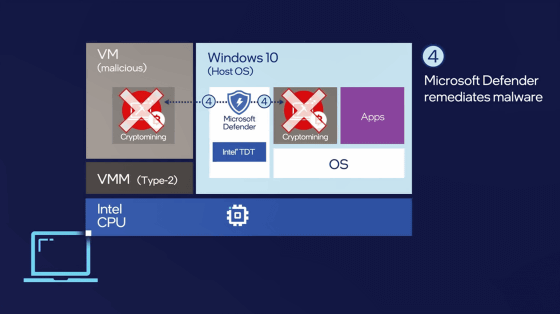
So Microsoft and Intel have worked together to develop a feature that uses CPU-based threat detection to detect signs of cryptojacking and protect devices even when malware is obfuscated. The new features are based on Intel's silicon-level threat detection feature set, Intel Threat Detection Technology (TDT), and will be integrated into Microsoft Defender for Endpoints, an enterprise security platform.
Watch the video below to see what threat detection technology looks like with TDT.
Endpoint Security with Microsoft Defender for Endpoint with Intel® TDT | Intel Business --YouTube
In recent years, cryptojacking has increased sharply due to the soaring price of virtual currencies, and according to a survey by Avira Protection Labs , cryptojacking increased by 53% in the fourth quarter of 2020 compared to the third quarter. thing. Cryptojacking takes away the resources required to mine cryptocurrencies without permission, which causes problems such as slowing down the device.
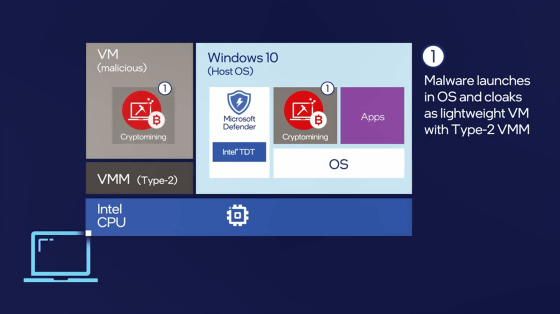
Cryptojacking malware is trying to circumvent typical security software by hiding virtual machines and obfuscating binaries.
When a user's device installs cryptojacking malware, cryptocurrencies are mined on the console or virtual machine.
Telemetry data , such as the performance of instructions processed by the CPU, is recorded by the CPU Performance Monitoring Unit (PMU).
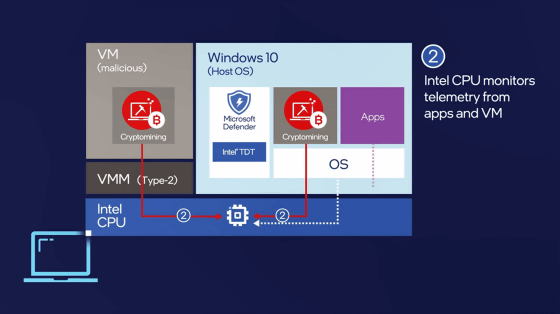
Intel's threat detection technology, TDT, applies machine learning to telemetry data sent by PMUs to detect unique signs when malware is executed with minimal processing. By performing CPU-based monitoring, cryptojacking can be detected regardless of security software measures such as malware obfuscation and virtual machine use.
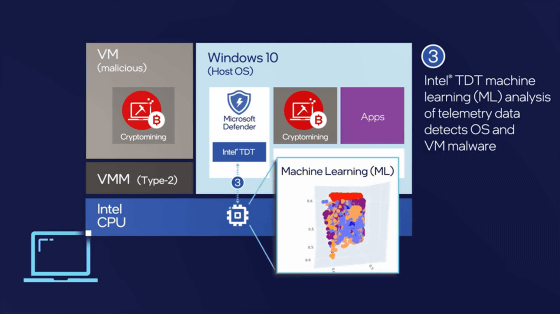
With TDT integrated, Microsoft Defender for Endpoints shuts down software and processes that perform cryptojacking in just seconds, avoiding wasting device machine power.
The new features will be available to users of 6th generation and later Intel Core processors and Intel vPro platforms. 'This partnership is an example of an ongoing investment in collaboration with OEMs and technology partners. Microsoft is working closely with chip makers to enhance hardware-based defenses,' said Karthik Selvaraj, Microsoft's Chief Security Research Manager. We are constantly exploring new possibilities for cyber threats and providing robust and resilient protection against cyber threats. '
Related Posts: