The timeline for attacks and countermeasures after the discovery of Microsoft's Exchange Server vulnerability looks like this

Security researcher Brian Krebs provides a timeline from reporting the vulnerability to releasing a patch and spreading the attack on the Microsoft Exchange Server vulnerability, which is believed to have targeted hundreds of thousands of organizations around the world. published. The vulnerability was first reported in January 2021, but its urgency can be seen in the patch being released a week ahead of schedule.
A Basic Timeline of the Exchange Mass-Hack — Krebs on Security
https://krebsonsecurity.com/2021/03/a-basic-timeline-of-the-exchange-mass-hack/
Attacks on Exchange servers expand from nation-states to cryptominers | The Record by Recorded Future
https://therecord.media/attacks-on-exchange-servers-expand-from-nation-states-to-cryptominers/
Microsoft hack: Biden launches emergency taskforce to address cyber-attack | US news | The Guardian
https://www.theguardian.com/us-news/2021/mar/08/microsoft-cyber-attack-biden-emergency-task-force
2021 March 2, Microsoft is about cyber-attacks by the Chinese government-based hacker group in the official blog report . Then, on March 5, 2021, Mr. Krebs said, 'Using a vulnerability in Microsoft's mail software, hackers attacked more than 30,000 organizations that form small and medium businesses, towns, cities, and local governments in the United States. I went. '
It is also pointed out that the government has issued an emergency directive due to a cyber attack by China, and more than 30,000 organizations have already been hacked --GIGAZINE

The attacker is believed to have exploited four newly discovered vulnerabilities in the email software Microsoft Exchange Server called 'Proxy Logon' to instill a web shell that allows complete remote control of the system. And according to information Krebs got from cybersecurity experts on condition of anonymity, Chinese hacking groups already control hundreds of thousands of Exchange Servers around the world, of which at least about US accounts. It is said that 30,000 cases will be included. On the other hand, it is also pointed out that 'the number of 30,000 is extremely modest.'
The Exchange Server vulnerability, which became a hot topic in March, was first reported in January. Krebs has published the following timeline from the discovery of the Exchange Server vulnerability to its response.
・ January 5 : Security consulting firm DEVCORE warns Microsoft of the findings.
January 6 : Cybersecurity company Volexity discovers an attack that uses an unknown vulnerability in Exchange.
・ January 8 : Microsoft reproduces and verifies the problem pointed out by DEVCORE.
January 27 : Security company Dubex warns Microsoft about an attack on a new Exchange vulnerability.
January 29 : Trend Micro posted on its blog that a web shell called 'Chopper' was planted via a vulnerability in Exchange.
February 2 : Volexity warns Microsoft about a new attack that uses a previously unknown Exchange vulnerability.
February 8 : Notifies Dubex that Microsoft has escalated the report internally.
-February 18 : Microsoft notifies DEVCORE that the target for security updates for Exchange vulnerabilities is March 9.
・ February 26-27: It is confirmed that attacks using vulnerabilities are gradually becoming global. During this period, the speed at which the attacker prepares the backdoor increases.
March 2 : DEVCORE security researcher Orange Tsai quoted a tweet on January 5 that 'reported the most serious RCE vulnerability ever' and said the patch was released. Tweet.
The patch release of this BIG ONE is coming soon, and a short advisory is also standing by! (BTW, no one guess the right target in comments ????) https://t.co/EX1XgBxlkW
— Orange Tsai ???? (@ orange_8361) March 2, 2021
-March 2 : Microsoft releases security updates for four vulnerabilities on a schedule one week ahead of schedule.
・ March 3 : Tens of thousands of Exchange servers have been hacked around the world, and thousands of new servers continue to be hacked every hour.
March 4 : White House Jake Sullivan posted on Twitter how important the patch is and how to detect if the system has already been hacked.
And, this article offers specific measures beyond just patching to determine if your systems are already compromised: https://t.co/JeO1YLV7kF
— Jake Sullivan (@ JakeSullivan46) March 5, 2021
・ March 5, 1:26 pm: White House spokesman Jen Paski expressed concern about the attack at a live briefing.
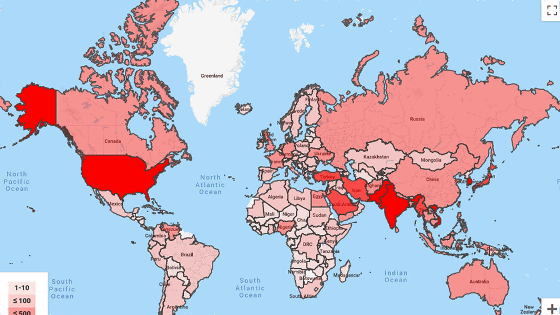
March 5, 4:07 pm: Krebs publishes reports that backdoors are installed in at least 30,000 organizations in the United States and hundreds of thousands of organizations around the world.
-March 6 : The Cybersecurity and Infrastructure Security Agency (CISA) of the Cybersecurity and Infrastructure Security Agency states that 'we are aware of the widespread domestic and international exploitation of Microsoft Exchange Server vulnerabilities.'
Looking at the timeline, Microsoft is releasing patches ahead of schedule, probably because of the rapid increase in speed and scale of the attack. In addition to the United States, security agencies in the Netherlands, Czech Republic, and Norway have already reported hackers breaking into Exchange. The affected organizations include the European Banking Authority and the Ministry of Labor.
In unattended countries, many security companies have confirmed attacks around the world, Kaspersky Lab reported a surge in attacks in Germany, and security software developer Malwarebytes has at least 1000 customers. It reports that it has found a ProxyLogon-related web shell on its system.
The patch released by Microsoft fixes the vulnerability and is effective for preventing damage to systems that have not yet been damaged, but it detects systems that have already been invaded and recovers from the damage. It's not a thing.
For this reason, Microsoft has also published a security script that confirms the intrusion into Exchange Serve.
CSS-Exchange / Security at main · microsoft / CSS-Exchange · GitHub
https://github.com/microsoft/CSS-Exchange/tree/main/Security
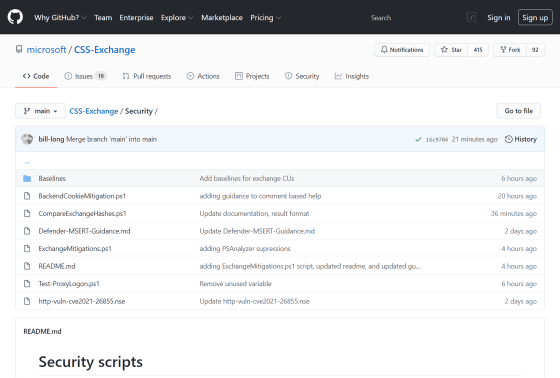
On March 8, cybersecurity company Netcraft reported that it 'detected 99,000 unpatched Outlook Web Access servers accessible from the Internet' even after the patch was released. Outlook Web Access allows remote access to Microsoft Exchange mailboxes, with Netcraft saying it has discovered a web shell backdoor in 10% of them.
Feeding Frenzy as criminal groups stake their claim on Outlook Web Access servers | Netcraft News
https://news.netcraft.com/archives/2021/03/08/owa-web-shells.html
Related Posts:
in Security, Posted by darkhorse_log