A smart chastity belt that can lock male genitals via Bluetooth becomes prey to hackers and a ransom is demanded
The Cellmate Chastity Cage , a smart chastity belt that can be controlled via Bluetooth from a mobile app, has become the target of a hacker's attack, resulting in it being remotely locked and threatening users with the threat of paying a ransom if they want it unlocked. Did.
Hacker used ransomware to lock victims in their IoT chastity belt
https://www.bleepingcomputer.com/news/security/hacker-used-ransomware-to-lock-victims-in-their-iot-chastity-belt/
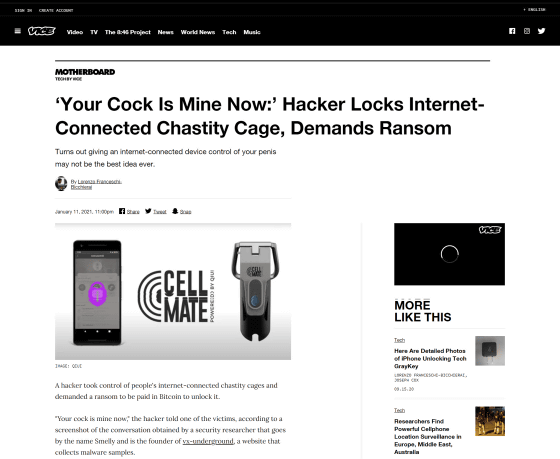
'Your Cock Is Mine Now:' Hacker Locks Internet-Connected Chastity Cage, Demands Ransom
https://www.vice.com/en/article/m7apnn/your-cock-is-mine-now-hacker-locks-internet-connected-chastity-cage-demands-ransom
In October 2020, British security company Pen Test Partners revealed that Cellmate Chastity Cage has a security vulnerability that allows remote control by anyone other than the user.
A smart chastity belt that can lock male genitalia via Bluetooth has been found to have a ``vulnerability that allows it to be completely locked remotely by an attacker'' - GIGAZINE

Pen Test Partners stated in a report that ``It takes less than a few days for an attacker to steal an entire user database and use it for extortion or phishing,'' but on January 9, 2021, It was reported that this became a reality. The attackers launched the attack targeting the mobile app that controls Cellmate devices, demanding a payment of 0.02 Bitcoin to unlock it. According to overseas news media BleepingComputer , 0.02 Bitcoin at the time of the attack was equivalent to $270 (approximately 28,000 yen).
Once the attack began, victims flooded with complaints that they were unable to control their devices. In addition, some victims reportedly received a message saying, ``Your penis is mine now.'' Some users were also concerned that ``the only way to unlock it would be to disconnect the device,'' but they were able to contact Cellmate support and request a reset, or they could manually disconnect the device. Manufacturer Qiui showed in a movie how to install the driver for this, and no users have been confirmed to have actually paid the ransom.
China-based manufacturer Qiui did not respond to requests for comment on this matter.
It has been reported that Qiui has fixed the vulnerabilities that were pointed out, so if you keep your app up to date, you are no longer a target of attacks. However, since such products are likely to have some kind of vulnerability, experts say, ``It is important that all companies have a way to contact researchers and stay in touch with them.'' points out.
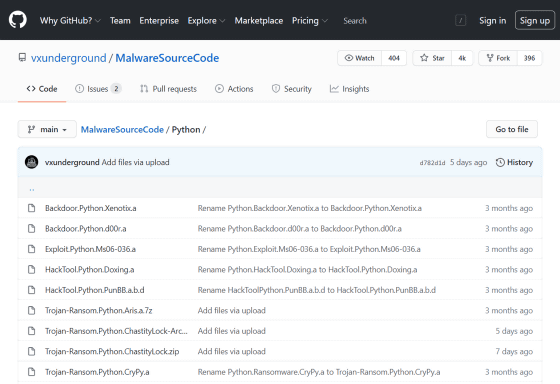
In addition, vx-underground , which collects malware source codes and samples, has also released the ransomware source code that it received from someone who said it was received from an attacker.
MalwareSourceCode/Python at main · vxunderground/MalwareSourceCode · GitHub
https://github.com/vxunderground/MalwareSourceCode/tree/main/Python
Related Posts:
in Free Member, Hardware, Security, Posted by darkhorse_log






