A smart chastity belt that can lock male genitalia via Bluetooth has been found to have a ``vulnerability that allows it to be completely locked remotely by an attacker''

A ``security flaw'' has been discovered in a smart chastity belt for men that can be controlled remotely by connecting to a smartphone via Bluetooth, allowing a malicious attacker to remotely control it and prevent it from being removed once worn. It turned out that it would go away.
Smart male chastity lock cock-up | Pen Test Partners
Locked In An Insecure Cage
https://internetofdon.gs/qiui-chastity-cage/
Internet-enabled male chastity cage can be remotely locked by hackers - The Verge
https://www.theverge.com/2020/10/6/21504019/internet-enabled-male-chastity-cage-cellmate-qiui-security-flaw-remotely-locked
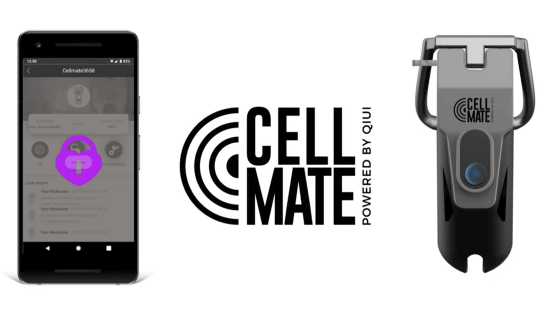
The device in question is a smart chastity device called the Cellmate Chastity Cage from sex toy maker Qiui .
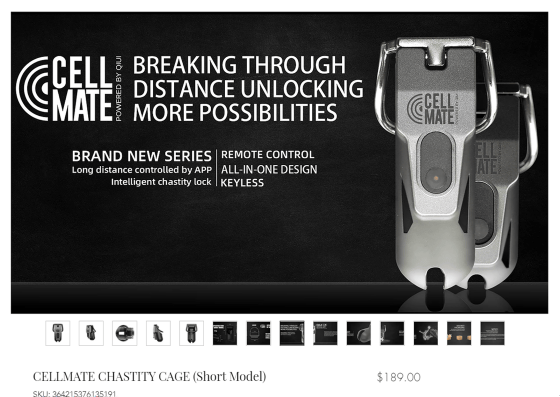
As Qiui says, ``We believe a true chastity experience is one that allows the wearer to lose control.'' The Cellmate Chastity Cage has no physical lock and is not controlled through a smartphone app. It is designed to stay in place as long as possible. Also, the waterproof and dustproof standard is IPX7, so you can even take a shower while wearing it.
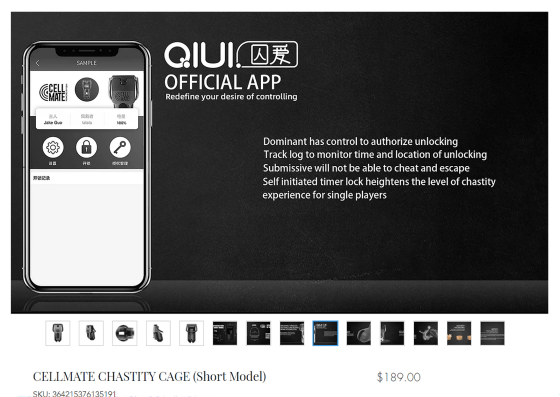
However, Pen Test Partners, a British security company, has discovered that a flaw in the API used to communicate between the Cellmate Chastity Cage and the smartphone app could allow anyone other than the user to control the Cellmate Chastity Cage remotely. It is pointed out that there is.
The Cellmate Chastity Cage is fixed by passing the penis through a metal ring, so to remove it without using an app, you can directly drive the motor built into the Cellmate Chastity Cage to release the electric lock. Otherwise, the metal ring must be cut with a grinder in close proximity to 'delicate and sensitive areas,' and Pen Test Partners says it is 'extremely dangerous to release a locked Cellmate Chastity Cage.' is.
You can actually hack the Cellmate Chastity Cage circuit and directly drive the motor used for the lock in the movie below.
CellMate Teardown - YouTube
Pen Test Partners also said that all API endpoints authenticated only with a member code to make requests, which was determined based on the date the user registered with the service. . Requests made using just a six-digit friend code can reveal information such as the user's name, phone number, birthday, location when registering the app, member code, and unencrypted user password. It seems like it's gone.
Qiui updated the app in June 2020 to fix this vulnerability, but users who have not updated the app are still at risk of wearing a chastity belt forever. Although Pen Test Partners sent messages to Qiui many times, there has been no response since June 2020, and contact has been lost. After consulting with another security researcher who happened to notice the same vulnerability in September 2020, Pen Test Partners decided to release this information.
Pen Test Partners said, ``This case shows that many sex toy manufacturers have an almost complete disregard for privacy and security,'' and the risk of personal information leakage is a real threat. It warns that there is a high possibility that it will be exploited by attackers.
Related Posts: