Intel abandons countermeasure against vulnerability "Spectre" of old CPU such as first generation Core i7 and Core 2 series

IntelVulnerability inherent in CPU "Specter" "Meltdown"We have been promoting the release of patches to alleviate the damage. Since the patch provision status of the CPU of the 1st generation Core processor was "stopped" in the newly disclosed list, "Topic Intel stopped responding to the old product?" , But Intel officially acknowledged that it was a fact.
Microcode Revision Guidance (Apr 3, 2018) - microcode-update-guidance.pdf
(PDF file)https://newsroom.intel.com/wp-content/uploads/sites/11/2018/04/microcode-update-guidance.pdf
Intel Will No Longer Issue Specter Patch For Some Older Chips (Updated)
http://www.tomshardware.com/news/intel-spectre-patch-older-chips,36815.html
On the CPU "Microcode Revision Guidance" announced by Intel on April 2, 2018, patch release status to vulnerability Specter has been reported. The correction patch of Specter (Variant 2) up to the 2nd generation Core processor "Sandy Bridge" was released in March, 2018, but in the release note of April 2018 newly released, Core i 7-920 The status of the 1st generation Core processor such as "Stopped" has become.
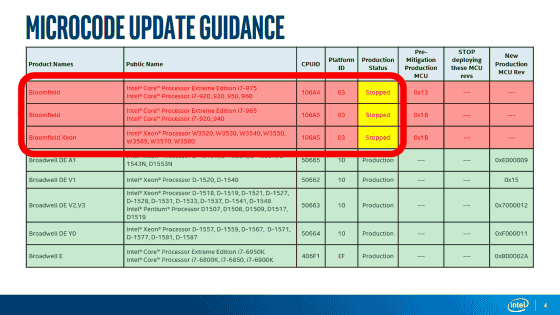
For this reason, it was talked as "Intel gave up on developing patches to alleviate vulnerabilities of CPUs before the 1st generation Core processor?" Intel, who was questioned about this, revealed officially discontinued the patch releases to the old CPU. CPUs decided not to release the patches are "Penryn" "Yorkfield" "Wolfdale" "Bloomfield" "Clarksfield" "Gulftown" "Jasper Forest (Nehalem)" "Harpertown" "SoFIA 3GR" Core 2 Duo E 8400 etc. Not only the former big hit CPU, but also the comparatively recently released Atom x3 C3000 series etc in 2015 are not supported.
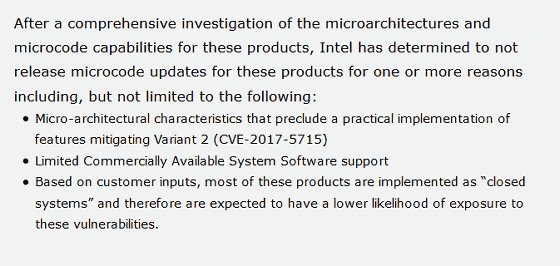
About the reason why Intel stopped supporting the old product, "The countermeasure to Specter Variant 2 on the design of the old CPU is not effective," "The support of the commercial software of the old product is limited," "The old product is a closed environment It is being used in, and the risk of damage is low "is cited.
Related Posts: