A terrible mechanism of command and control of botnets via comments of Instagram's celebrity account

ByBlogtrepreneur
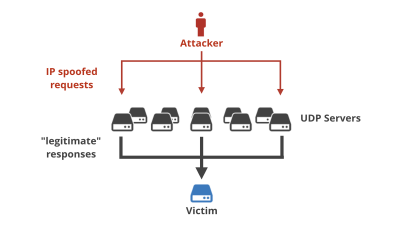
Watering hole attackIs a technique of risking a website that is highly likely to be visited by a target and attacking the target via a tampered web site. The cyber spy group that has been engaged in cyber attacks for many years targeting government, civil servants, diplomats, etc. "TurlaAlso utilizes watering hole attack, and develops Internet access management systemForcepointPosted in February 2017articleAccording to Turla, it is targeting government-related websites such as the Ministry of Foreign Affairs, the Embassy and political parties. In Turla like that, use it when launching a cyber attackBotnetNecessary to conduct and control "C & C serverIt is becoming a topic to get places in a special way.
Turla's watering hole campaign: An updated Firefox extension abusing Instagram
https://www.welivesecurity.com/2017/06/06/turlas-watering-hole-campaign-updated-firefox-extension-abusing-instagram/
A report summarizing what BitDefender has investigated about Turla's watering hole attack(PDF)Pacifier APTDetails on Spear phishing attacks using "malicious Word files" sent to several institutions around the world.
There is "Firefox extension function to set up backdoor on PC" very similar to what appears in this report. It is named "HTML5 Encoding", it is a back door for JavaScript and it is distributed on the Internet via the website of the Swiss security company. The backdoor by this extension seems to be very simple, but it seems to acquire the domain of C & C server in a special way, thereWeLiveSecuritySecurity researchers' attention paid attention.
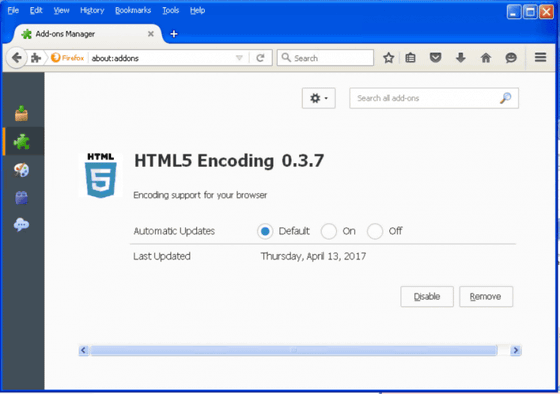
Firefox extension "HTML5 Encoding" accesses the C & C server via abbreviated URL by bit.ly, but the URL is not written anywhere. Then, how to acquire the domain of C & C server seems to use the comments made to the posting of a specific Instagram.
It was used as one of themBritney Spears' official Instagram accountis.
"HTML5 Encoding" parse comments on posts to Instagram and calculate custom hash values for each comment. If the hash value matches 183, execute the regular expression "(?: \\ u 200d (?: # | @) (\\ w)" to get the shortened URL. The hash value of the comment of the part matched 183.
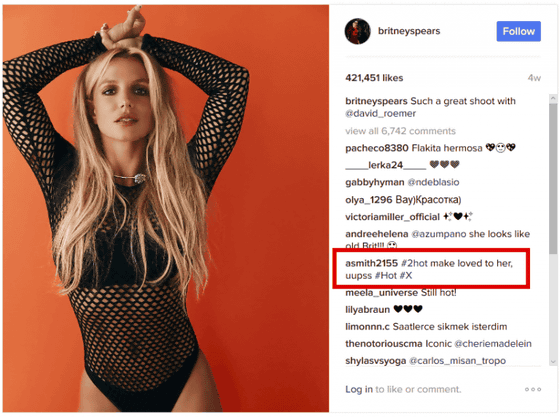
当該コメントを先ほどの正規表現で変換すると短縮URLの「http://bit.ly/2kdhuHX」(※アクセスしないでください)が取得できます。このURLは、Turlaが過去にウォータリングホール攻撃で使用したC&Cサーバーの「static.travelclothes.org/dolR_1ert.php」(※アクセスしないでください)につながるそうです。
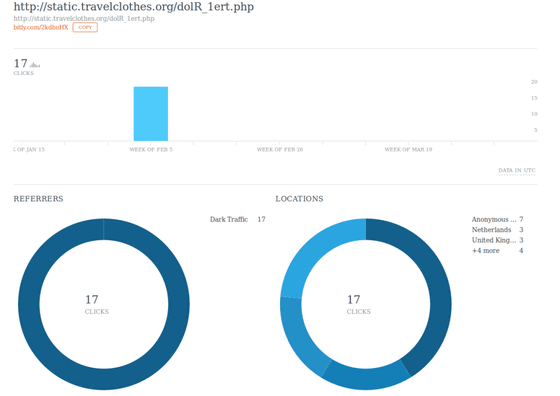
なお、この「http://bit.ly/2kdhuHX」という短縮URLを誰がクリックしたのかについての統計データは以下の通り。Instagramに写真が投稿されたのは1月初旬で、コメントが投稿されたのは2月6日。リンクへのアクセスは2月にわずか17回のみで、「これはテスト実行だった可能性がある」とWeLiveSecurityは記しています。
The Firefox extension "HTML5 Encoding" implements a simple backdoor, gathers information about running systems,AESEncrypted using. Then I will send the acquired information to the C & C server. For backdoor components, "execute arbitrary files" "upload files to C & C" "download files from C & C" "read contents of directories - send file list and size and date to C & C" It is said that four functions are included.
Turla's approach of using social media to recover C & C server addresses makes attackers' attacks easier and makes defensive security actions more difficult. It is very difficult to distinguish between malicious traffic and legitimate traffic to social media, changing the address of the C & C server can also erase all traces and give flexibility to attackers.
Related Posts:
in Security, Posted by logu_ii