An unknown backdoor capable of cyber attack can be found on a silicon chip made in China that is used for nuclear power plants and military
ByJurvetson
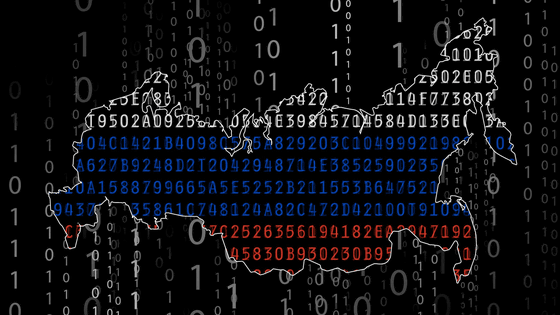
UK researchers seem to have noticed that if China is concerned about it, cyber attacks can be made to commercial facilities and military facilities, and important bases can be down. It was discovered in the survey that there was an unknown backdoor on the silicon chip made in China, and this chip is widely used in public transportation, nuclear power plants, and weapons related systems.
Hardware Assurance and its importance to National Security - Latest news on my hardware security research

Cambridge UniversityTAMPER InstituteofSergei SkorobogatovSenior research professorMI 5 (British Intelligence Agency Security Division)YaNSA (National Security Agency of the United States),IARPA (Intelligence Advanced Research Project Activity)We received information on the dangers of silicon chips from such as investigation.
The survey was conducted with the aim of decrypting the silicon chip used for military purposes and investigating whether unknown functions exist in the chip. The target is a chip that the US uses for military purposes, and it is made in China which was highly encrypted.
Professors Skorobogatov and others discovered an unknown backdoor without spending so much time investigating this chip. There was a key on the backdoor and it was also successful to extract this. Using this key, it seems that it was possible to disable or reprogram the chip even if the user locked it with his key.
ByAdmlCrunch
This chip is popular in many systems related to weapons, and it is also used in nuclear power plants and public transportation. It was mainly used for cyber attack against Iran in 2010Stuxnet (Staxnet) wormCaused results such as stopping the facilities of nuclear facilities, but using the backdoor found this time it is equally possible to launch a Stuxnet attack against millions of weapons. This will be a scale and scope that will have a major impact on the national security and public infrastructure that was attacked.

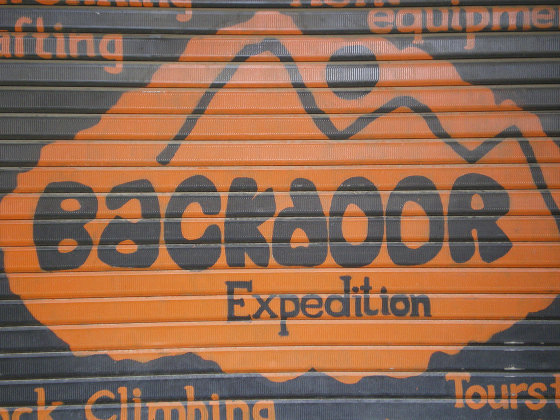
ByUNC - CFC - USFK
Stuxnet uses the vulnerability of Windows and it infects by merely displaying it with explorer, it was able to prevent the infection by adopting the patch patch and thoroughly defending the software, but it is necessary to investigate the vulnerability of the hardware Defense on the software side makes no sense when it is done.
This time, the investigation technique used by Professor Skorobogatov et al. Scan silicon chip and hardware to find backdoor and Trojan horse, unexpected behaviors at low cost, fast response time and high portability, many The high adaptability that can correspond to chips is attractive. We can develop better search algorithms to find out if there is further funds, whether it is being spy on a wider range or not, and the system is not vulnerable.
If this is true, it seems likely that Professor Skorobogatov will think about how to deal with it ... ....
Related Posts:
in Note, Posted by logc_nt