Google has identified North Korean hacker group 'UNC1069' as the perpetrators of a supply chain attack against the open-source Axios.
Google's security researchers have submitted a report investigating the Axios JavaScript library's supply chain attack that resulted in the installation of a remote access
North Korea-Nexus Threat Actor Compromises Widely Used Axios NPM Package in Supply Chain Attack | Google Cloud Blog
https://cloud.google.com/blog/topics/threat-intelligence/north-korea-threat-actor-targets-axios-npm-package?hl=en
axios Compromised on npm - Malicious Versions Drop Remote Access Trojan - StepSecurity
North Korean hackers blamed for hijacking popular Axios open source project to spread malware | TechCrunch
https://techcrunch.com/2026/03/31/hacker-hijacks-axios-open-source-project-used-by-millions-to-push-malware/
Hackers compromise Axios npm package to drop cross-platform malware
https://www.bleepingcomputer.com/news/security/hackers-compromise-axios-npm-package-to-drop-cross-platform-malware/
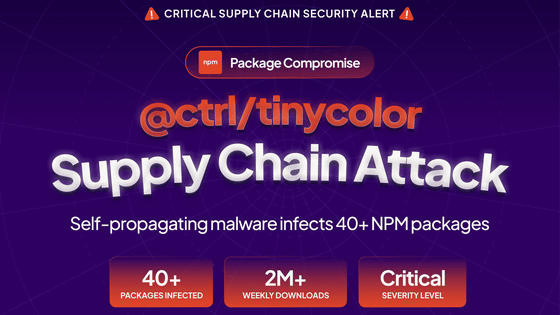
On March 31, 2026, the Axios npm distribution package was compromised, and two malicious versions were released. Installing these versions could allow remote control of a PC. According to security researchers, the hackers incorporated a mechanism into the malware and the code for distributing it that would automatically self-delete after installation, in an attempt to evade detection by anti-malware engines and researchers.
Axios is a popular package downloaded tens of millions of times every week. The distribution of malware could have put millions of developers at risk. This hijacking was discovered and stopped within three hours.
When the attack first occurred, Axios maintainers were unable to regain control of the project. In a public issue on GitHub, one contributor stated that 'the attacker's privileges exceeded ours, so we were unable to revoke access from the account that made the malicious posts.'
Hackers successfully compromised the account of one of the project's main developers, planting malicious code. This developer had the authority to distribute updates. It is reported that the hackers replaced the legitimate email address registered to the account with their own, making it difficult for the developer to regain access.

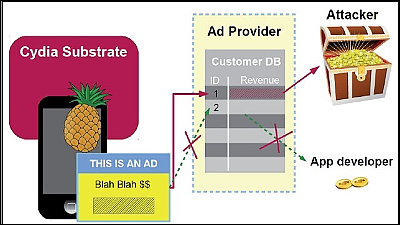
After gaining access to the package, the attacker inserted a malicious dependency called plain-crypto-js@^4.2.1 into the package.json file, but did not modify the Axios code. This dependency executes a post-installation script during package installation, launching an obfuscated dropper (setup.js). This dropper connects to a command and control server and retrieves the payload for the next stage based on the detected OS.
On Windows, this attack uses a combination of VBScript and PowerShell to launch a hidden command prompt window and execute malicious scripts. To evade detection and continue operating after a restart, the malware copies PowerShell to %PROGRAMDATA%\wt.exe, then downloads and executes the PowerShell script.
On macOS, this malware uses AppleScript to download a binary file to /Library/Caches/com.apple.act.mond, mark it as an executable, and run it in the background. On Linux, the dropper uses /tmp/ld.py to run in the background. In either case, the malware infects the host with a remote access Trojan, allowing the attacker to execute commands and remain persistently active on the infected system.
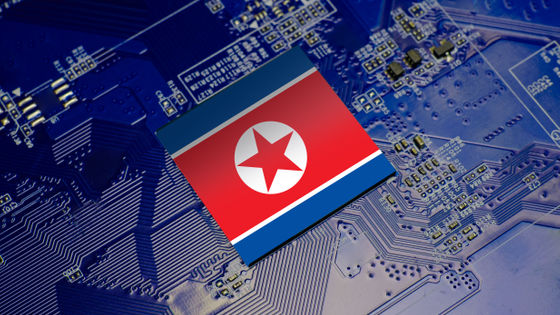
Google has linked the breach to a financially motivated North Korea-linked threat actor known as 'UNC1069.' The investigation revealed that the connections originated from a specific AstrillVPN node previously used by UNC1069.
John Hartquist, principal analyst at Google's threat intelligence group, said, 'North Korean hackers have extensive experience with supply chain attacks, which they have previously used to steal cryptocurrencies. The full extent of this incident is still unclear, but given the popularity of the compromised packages, it is expected to have far-reaching consequences.'
Related Posts: