The popular @ctrl/tinycolor package, downloaded over 2 million times per week, has been compromised along with over 40 other NPM packages in a sophisticated supply chain attack called 'Shai-Hulud.'
On September 15, 2025, security firm StepSecurity reported that the popular NPM package '
ctrl/tinycolor and 40+ NPM Packages Compromised - StepSecurity
https://www.stepsecurity.io/blog/ctrl-tinycolor-and-40-npm-packages-compromised
The malware used in Shai-Hulud is capable of self-propagation, automatically infecting other packages managed by the maintainer of the infected package. It also harvests credentials from developer environments for cloud services such as Amazon Web Services, Google Cloud, and Microsoft Azure, and attempts to install a backdoor in GitHub Actions to gain persistent access.
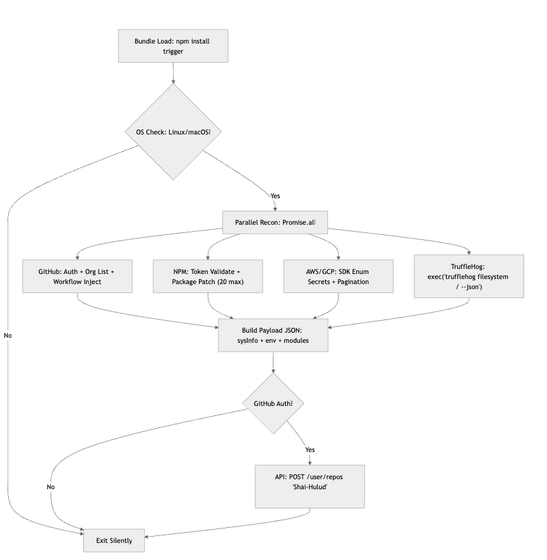
The attack begins when a developer runs the 'npm install' command, which executes a malicious script (bundle.js) that specifically targets Linux and macOS environments.
The malware first uses the open-source tool 'TruffleHog' to scan the developer's file system for sensitive information such as AWS access keys, and also collects credentials contained in environment variables such as 'GITHUB_TOKEN'. The collected credentials are packaged in JSON format and uploaded to a public GitHub repository named 'Shai-Hulud', where they are delivered to the attackers.
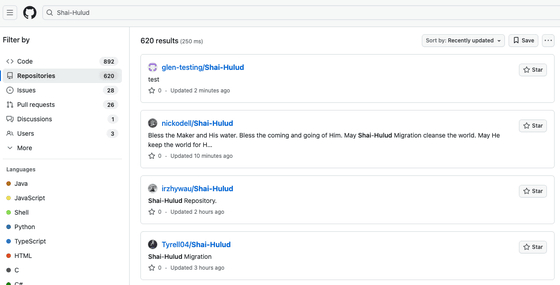
Furthermore, the malware self-propagates, exploiting the compromised maintainer's account to infect other NPM packages managed by that maintainer. To persist, the malware creates a malicious GitHub Actions workflow file named '.github/workflows/shai-hulud-workflow.yml' in the repository.
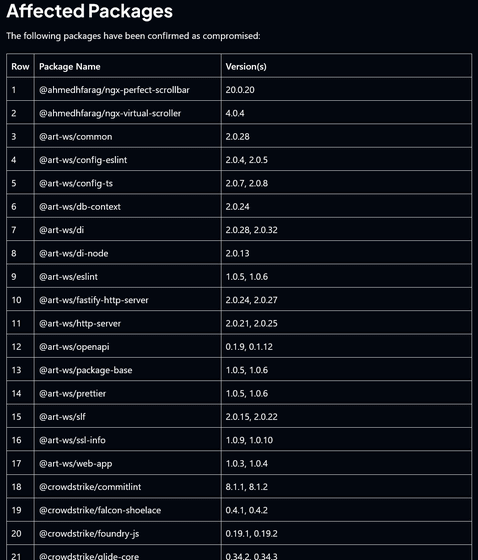
A table summarizing the packages affected by Shai-Hulud can be viewed by clicking on the image below.
StepSecurity recommends the following immediate actions to prevent damage caused by Shai-Hulud:
Identifying and removing compromised packages
Check whether your project contains any affected packages, and if so, uninstall them immediately.
・Repository cleanup
Check your repository for malicious GitHub Actions workflows and suspicious branches named 'Shai-Hulud' and delete them if they exist.
・Credentials rotation
Immediately revoke and reissue all potentially compromised credentials, including GitHub personal access tokens, NPM tokens, and AWS, Google Cloud, and Microsoft Azure credentials.
Cloud infrastructure audit
Investigate AWS CloudTrail, Google Cloud audit logs, etc. to determine whether there was any suspicious API access during the period of the potential breach.
Related Posts:
in Security, Posted by log1i_yk