It has been pointed out that the White House app tracks users' precise location every 4.5 minutes.
A software developer has pointed out that
I Decompiled the White House's New App
https://blog.thereallo.dev/blog/decompiling-the-white-house-app#consentpaywall-bypass-injector
White House App Found Tracking Users' Exact Location Every 4.5 Minutes via Third-Party Server | IBTimes UK
https://www.ibtimes.co.uk/white-house-app-gps-tracking-controversy-1788974
The White House Built a Surveillance App and Calls It a News Feed
https://mitchthelawyer.substack.com/p/the-white-house-built-a-surveillance
The official White House app allows users to directly access government news and press conferences without going through the media. It also includes a reporting button that redirects users to the Immigration and Customs Enforcement (ICE) reporting page.
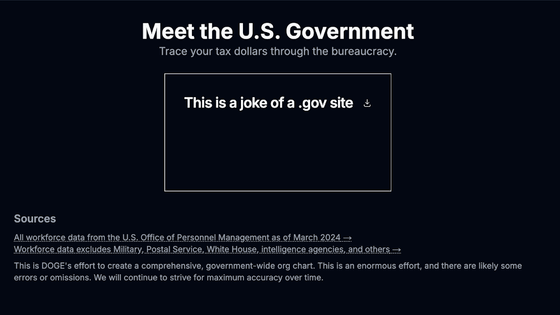
Software developer Thereallo analyzed the app and pointed out that the user's location information was being obtained using a tool called OneSignal.
OneSignal is a widely used tool for sending push notifications. Thereallo claims that the official White House app obtains location information every 4.5 minutes when the user has the app open, and every 10 minutes when the app is not open, and sends it to external servers such as OneSignal.
The White House App has OneSignal's full GPS pipeline compiled in, polling your location every 4.5 minutes, syncing your exact coordinates to a third party server. https://t.co/0HuNiSitA0 pic.twitter.com/UjLO9VdyVZ
— Thereallo (@Thereallo1026) March 28, 2026
However, the International Business Times quoted another developer who said that 'while the code for location tracking exists within the OneSignal SDK, the app itself does not call that function, and no prompt asking the user for location permission was displayed during installation.' OneSignal's documentation also states that location information is not collected unless the developer explicitly enables the function.
In addition, several other questionable aspects of the app have been pointed out.
For example, the app loads code for embedding videos from a GitHub Pages site run by an individual developer. If this GitHub account were compromised, there would be a vulnerability that allows arbitrary code to be distributed to all users of the app.
Furthermore, the app inserts JavaScript into all websites opened through its built-in browser, excluding cookie consent banners, GDPR (EU General Data Protection Regulation) consent dialogs, login screens, sign-up screens, and paywalls. While these screens are necessary for websites to comply with legal regulations, there are questions about the legal basis for deliberately hiding them.
In addition, it has been pointed out that the app is granted 'China-level surveillance privileges' because it requests a variety of permissions, including the ability to modify or delete shared storage contents, use fingerprint and biometric authentication hardware, network and Wi-Fi connectivity, prevent the device from going to sleep, and run at startup.
‼ ️🇺🇸: NEW WHITE HOUSE 'NEWS' APP HAS CHINA-LEVEL BIG BROTHER PERMISSIONS 👀
— Diligent Denizen 🇺🇸 (@DiligentDenizen) March 27, 2026
White House launched new app today claiming to let citizens to get news from source.
What they didn't tell you was that it logs your location, notifications, biometrics & more.
We pay for this 1984. 😒 pic.twitter.com/ssSjCnRns1
Furthermore, the sloppiness of the development process has been exposed, including instances where localhost URLs were found in the production environment.
Attorney Mitch Jackson pointed out that 'federal privacy laws do not specify how government apps can collect and use location data of American citizens, so users have no way of knowing what information is being collected.'
Related Posts: