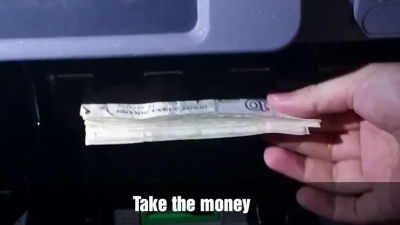
FBI warns of increasing ATM jackpot attacks, with losses expected to exceed 3 billion yen by 2025 alone

The Federal Bureau of Investigation (FBI) has issued a warning statement, including detailed technical information and indicators of compromise (IOCs), about a sharp increase in 'jackpotting attacks' across the United States, which use malware to fraudulently release cash from ATMs. Of the 1,900 jackpotting incidents reported since 2020, more than 700 occurred in 2025 alone, resulting in losses exceeding $20 million (approximately 3.1 billion yen).
Increase in Malware Enabled ATM Jackpotting Incidents
Across United States
(PDF file)
FBI says ATM 'jackpotting' attacks are on the rise, and netting hackers millions in stolen cash | TechCrunch
https://techcrunch.com/2026/02/19/fbi-says-atm-jackpotting-attacks-are-on-the-rise-and-netting-hackers-millions-in-stolen-cash/
At the heart of these attacks are malware such as the Ploutus family, which target a software layer called XFS (Extensions for Financial Services), which controls the ATM's hardware.
Typically, ATMs require approval from the bank before dispensing cash, but by sending commands directly to XFS, malware can bypass the bank's approval process and instantly dispense cash at the attacker's request. Because the malware exploits a vulnerability in the Windows operating system commonly used in many ATMs, a wide range of models, regardless of manufacturer, are affected. It is characterized by the theft of large amounts of cash in just a few minutes without using the customer's account information or card.

The most common infection route is for attackers to use a commercially available generic key to open the front panel of the ATM and gain physical access to the internal hard disk drive. Attackers then either remove the hard disk drive and write malware to it using an external computer, or replace it with a different drive or external device pre-installed with malware, then reboot the system to execute the malicious program. Therefore, attacks are often discovered through door-open alerts outside of maintenance schedules, unexpected drops in cash balances, sudden ATM shutdowns, or the connection of unauthorized devices to the ATM.
According to the FBI, unexpected executable files such as Newage.exe, Color.exe, Levantaito.exe, NCRApp.exe, sdelete.exe, Promo.exe, WinMonitor.exe, and Anydesk1.exe have been found in Windows-based ATM systems. Other important clues include unauthorized installation of remote connection tools such as TeamViewer and AnyDesk, as well as access logs from suspicious IP addresses. System monitoring may allow for detailed analysis of event logs, such as Event ID 6416, which detects the insertion of a USB device, and Event ID 4663, which records file operations, to identify the early stages of an attack.

The FBI recommends taking both physical and digital measures, such as replacing standard locks with unique ones, installing sensors to detect vibration and temperature changes, alarms that activate when maintenance hatches are opened, and additional barriers to cash boxes.
On the digital side, the FBI argued that the most powerful measures to prevent malware from slipping through network surveillance include hard drive encryption, boot-time integrity checks using TPMs, device whitelisting, and periodic comparison and validation of current hash values against a 'gold image' of a verified system state.

The FBI encourages people to report any suspicious activity they notice to their local FBI field office or Internet Crime Complaint Center (IC3) immediately.
Related Posts: