Discovered that millions of Windows PCs had been exposed to malware attacks for years due to Microsoft's outdated driver list

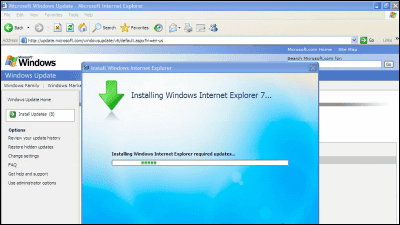
Microsoft updates the blocklist on devices with Windows updates. However, according to Ars Technica, Microsoft has not been able to properly protect Windows PCs from malicious drivers for about three years because this block list update was not actually working.
How a Microsoft blunder opened millions of PCs to potent malware attacks | Ars Technica
Microsoft's out-of-date driver list left Windows PCs open to malware attacks for years - The Verge
https://www.theverge.com/2022/10/16/23405739/microsoft-out-of-date-driver-list-windows-pcs-malware-attacks-years-byovd
It was pointed out that users were vulnerable to an attack called ' BYOVD ' and were able to install vulnerable drivers because the block list update via Windows update was not working properly. I'm here.
A driver is a file that the OS uses to communicate with external devices and hardware such as printers, graphic cards, and webcams. Since drivers have access to a device's OS or kernel core, Microsoft requires all driver providers to have their drivers digitally signed, which tells users that their drivers are safe to use. ” is guaranteed. However, if existing digitally signed drivers have security holes, hackers can exploit them to gain direct access to Windows.
Due to this vulnerability, in August 2022, hackers installed and distributed ransomware called ``BlackByte '' in the driver of the overclocking utility `` MSI AfterBurner ''. There have also been reports of exploiting a vulnerability in the anti-cheat driver installed in the popular free-to-play game Genshin Impact. In addition, security firm ESET reported that North Korean hacking group Lazarus launched BYOVD attacks against Dutch aerospace employees and Belgian political journalists in 2021. increase.

Microsoft uses something called Hypervisor Protected Code Integrity ( HVCI ) to protect your PC from malicious drivers. Microsoft claims this HVCI is enabled by default on certain Windows devices. However, according to a survey by Ars Technica and cybersecurity company Analysis, this HVCI did not provide sufficient protection against malicious drivers.
Will Dormann, Senior Vulnerability Analyst at Analysis, reports that malicious drivers on Microsoft's blocklist were successfully downloaded to HVCI-enabled devices. According to Dormann, Microsoft's blocklist hasn't been updated since 2019 and includes ' attack surface reduction rules (ASR rules) ' to prevent actions often abused by malware to compromise devices and networks. has also found that it is insufficient to protect devices from malicious drivers.
The Microsoft recommended driver block rules page states that the driver block list 'is applied to' HVCI-enabled devices.
— Will Dormann (@wdormann) September 16, 2022
Yet here is an HVCI-enabled system, and one of the drivers in the block list (WinRing0) is happily loaded.
I don't believe the docs. https://t.co/7gCnfXYIys https://t.co/2IkBtBRhks pic.twitter.com/n4789lH5qy
In other words, Ars Technica pointed out that Windows PCs have not been adequately protected from attacks using vulnerable drivers since 2019, when Microsoft stopped updating its driver blocklist.
Microsoft took no action against Dormann's investigative report until October 2022. However, Jeffrey Sutherland, Microsoft's project manager, told Dormann, 'We have updated our online documentation and added a download with instructions for applying the binary version directly.' We are also fixing the service process issue that was causing it,' he tweeted, stating that the issue was addressed.
Thanks for all the feedback. We have updated the online docs and added a download with instructions to apply the binary version directly. We're also fixing the issues with our servicing process which has prevented devices from receiving updates to the policy.
— Jeffrey Sutherland (@j3ffr3y1974) October 6, 2022
In addition, Microsoft has published a document summarizing how to manually update the driver's block list. However, it is unknown when Microsoft will automatically update the driver block list through Windows updates.
Microsoft Recommended Driver Blocking Rules (Windows) - Windows security | Microsoft Learn
https://learn.microsoft.com/en-us/windows/security/threat-protection/windows-defender-application-control/microsoft-recommended-driver-block-rules
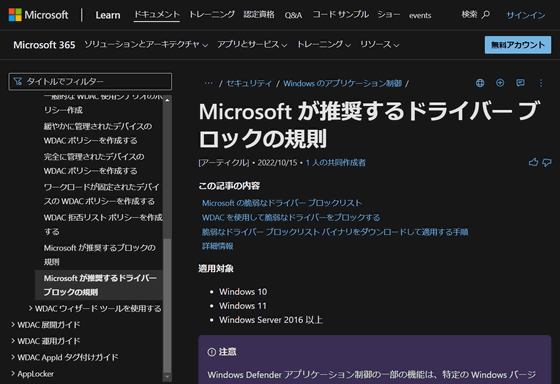
A Microsoft spokesperson told Ars Technica, ``While the list of vulnerable drivers is updated regularly, we have received feedback that there are gaps in synchronization between OS versions. , We plan to continue to provide service as usual with future Windows Updates. We will update our documentation page when new updates are released.'
Related Posts: