ISP is beta testing SIM card dedicated to anonymous communication technology 'Tor'

by Alexandru Zdrobău
" SIM card " is indispensable to use call function and mobile network communication function with general smartphone or mobile phone. Today, British ISP has developed a dedicated SIM card that connects to the network only via "Tor" which is an anonymous communication technology, and is doing beta test.
This SIM Card Forces all of Your Mobile Data Through Tor - Motherboard
https://motherboard.vice.com/en_us/article/d3qqj7/sim-card-forces-data-through-tor-brass-horn-communications
In the online chat with the British grass-roots ISP · Brass Horn Communications, IT-related news site · Motherboard got information that Brass Horn Communications has developed Tor specialized SIM card and is currently conducting beta test .
"Tor (Tora)" is a technique that allows anonymous communication without knowing information such as "who accessed the website", by not leaving the IP address of the access source that is normally recorded It is software for using technology. Please refer to the following article to see how it works.
Commentary on how anonymous communication "Tor" works How to understand - GIGAZINE
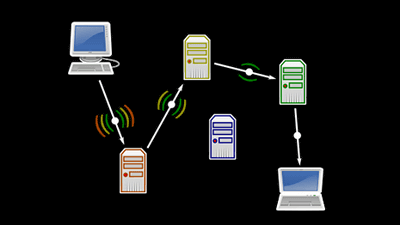
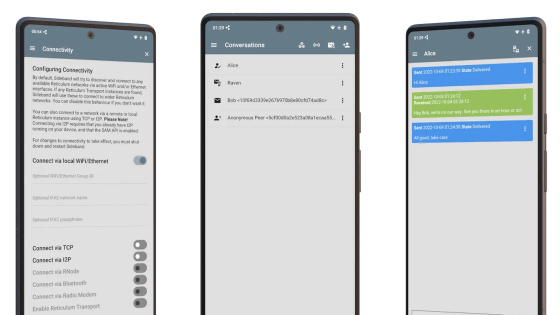
Brass Horn Communications is a service born as a "Tor-based ISP" to combat the global "eavesdropping" originally exposed by Edward Snowden . Since Tor can connect with Browser software from PC and "Orbot" application for Android, it was possible to use Tor with smartphone. But the problem is that Motherboard pointed out that there is a possibility that traffic that is not via Tor may occur, such as "using a software that generates a separate communication while launching the Tor browser".
This is the solution for Tor Toru SIM card. In fact, Gareth Llewelyn who made Brass Horn Communications talks about its significance, "What is important is" fail-safe. "When it is not a Tor connection, you can not connect in the first place.
In order to use this Tor dedicated SIM card, it is necessary to install Orbot on the terminal itself, and so far only services in the UK are offered.
Like Google, there is a service that attempts to unify and manage all information, but it is interesting that there is a mechanism that does not thoroughly leak information. The number of people looking for such services may be more than you think.
Related Posts:
in Hardware, Web Service, Smartphone, Posted by logc_nt