ABBYY that stores scanned documents such as company contracts and internal notes turned out to have managed more than 20,000 documents without password lock
ABBYY , which provides OCR software and cloud service, revealed that more than 20,000 document data scanned by customers and saved in the cloud was made public on the server without using a password.
ABBYY exposed its document storage database with more than 200K scanned contracts, memos, letters. | Bob Diachenko | Pulse | LinkedIn
https://www.linkedin.com/pulse/abbyy-exposed-its-document-storage-database-more-than-bob-diachenko
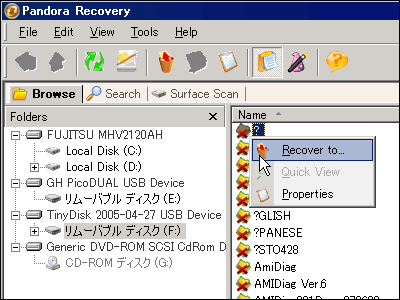
Security researcher Bob Dia Chenko discovered that there is no password lock for logging in to MongoDB hosted at AWS and that 142 GB of data is stored in the database.
Dia Chenko who confirmed security risks that could be the subject of cyber attacks conducted sample analysis of the database to identify and protect the owner and found that the data recognition company's infrastructure from the file name of "documentRecognition" "documentXML" It seems that we could guess that it was part. And from the company's email address and encrypted password in "user" information, we identified that MongoDB administrator is ABBYY. According to Mr. Dia Chenko, MongoDB in question stored more than 20,000 scanned document data consisting of agreements, NDA, memos, other internal documents and the like kept by ABBYY client companies That's right.
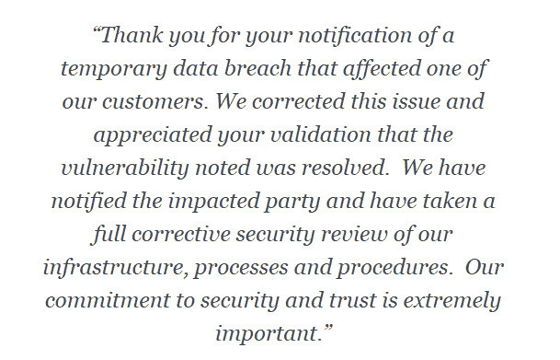
When Mr. Dia Chenko notified ABBYY officials extracted from the database by e-mail, on the next day, we received a reply from the information security officer and received a request to "provide detailed information on the problem" It was. After that, ABBYY received a report saying "We have notified the affected customers" along with a report saying "system vulnerability has been eliminated", but it seems that the customer company name was not revealed .
In addition, companies using ABBYY 's services can be confirmed on the following ABBYY page, which shows that large companies such as M - McDonald' s, PepsiCo, Volkswagen etc had their names.
ABBYY Customers Stories
https://www.abbyy.com/en-ee/case-studies/
According to Dia Chenko, it seems that access to the problem MongoDB finally became impossible to access immediately after sending its own IP address two days after the inquiry by the first e-mail, and the password lock is applied until then It is unclear how long there was no period.
Related Posts:
in Web Service, Security, Posted by darkhorse_log