Pros and cons of an investigation method using 'Stingray' that collects information on the target person by pretending to be a communication base station of a smartphone

By
With the advent of mobile phones and smartphones and the world becoming 'connected' to the Internet, society is changing even faster than ever before. Now that smartphones are used for crimes, a device called 'Stingray' that can grasp the activities of criminals at the terminal level is being used, but regarding its operation There are still many voices of pros and cons.
How a Hacker Proved Cops Used a Secret Government Phone Tracker to Find Him --POLITICO Magazine
https://www.politico.com/magazine/story/2018/06/03/cyrus-farivar-book-excerpt-stingray-218588
In the summer of 2008, a man in Santa Clara, a suburb of San Francisco, California, was marked by law enforcement agencies. An FBI agent conducting a secret investigation finds a man in the city and begins to follow him. The man noticed the trail and accelerated his steps.
The man emerged while investigating a bank account used for fraud, and according to the owner of the rental property he lives in, his name is 'Stephen Travis Broner' and his occupation is a software engineer. However, this is a pseudonym, and the actual name was not known until the investigator actually secured the identity, and it was called by the investigators as 'hacker'. From 2005 to 2008, the 'hacker' colluded with two colleagues to commit more than 1900 tax refund frauds, earn $ 4 million and transfer money to more than 170 bank accounts. It is believed that it was tax refunded.
A special device called 'Stingray' was used without a warrant to investigate a 'hacker' who claims to be Broner. 'Stingray' is a device that intercepts the communication of surrounding terminals by impersonating mobile phone base stations installed everywhere in the city and acquires individual identification numbers and location information. As of 2018, it seems that the device has already been introduced by many investigative agencies, but since its existence was hardly known at that time, it seems that the criminal side hardly marked it.
The actual state of the investigation method using 'Stingray' that collects individual identification information and location information of smartphones by pretending to be a mobile phone base station --GIGAZINE
A hacker who realizes that he is marked has an escape method such as jumping on a train and running away, or jumping high on an airplane, and is he actually being chased by an agent, or he just takes a delusion. It seems that he was in a state where he was just hung up, but he was convinced of the situation when a police car of the Santa Clara police appeared in front of him. I tried to escape immediately.
However, the hacker could not escape from the siege and was arrested. After that, when the police obtained a warrant and proceeded with the investigation of the surroundings such as the residence, the terminal of Verizon Wireless's data communication plan 'Internet Air Card' and 'Stephen Travis Broner' and 'Patrick' were found in the room with only a bed and a desk. A forged driver's license with a name such as 'Stout' was found. In addition, according to the contents announced by the FBI after that, multiple hard disks, cash of 116,340 dollars (about 12 million yen) and gold coins equivalent to more than 208,000 dollars (about 21 million yen), about 10,000 dollars (about 21 million yen) Silver coins worth (1 million yen), counterfeit IDs and counterfeit devices were also found.
Investigators have determined that the hacker's fingerprint belongs to a person named 'Daniel Rig Maiden,' who has been convicted of misdemeanor crimes in the past. Analyzing Rig Maiden's computer, he found in his email history that he was 'moving away from the United States to Dominican Republic', 'acquiring citizenship in another country', and giving a Dominican government employee bribe to give birth certificate. It is also known that the contents such as 'Getting a passport' were included.
One of the highlights of the investigation was 'Which law allowed the use of'Stingray'?' Said London-based privacy activist Erik King. Says. 'We know that police have and use Stingray, they don't admit it, and they've been using it for over a decade,' King said. It emphasizes the need for this matter to be the subject of public debate.

By
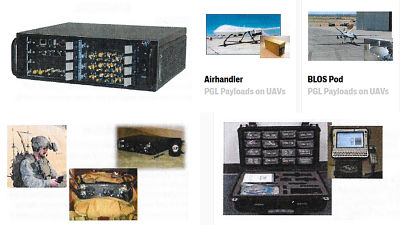
The 'Stingray' is a device whose main body is a device that is as small as a desk, and can be easily carried in a car. In the past, a secret catalog of equipment was leaked.
A secret catalog of equipment used for eavesdropping and eavesdropping on mobile phones leaked --GIGAZINE
Even after being sent to the detention center, Mr. Rig Maiden had a big mystery. For Rig Maiden, who used multiple IDs to keep his identity and paid in cash without using a credit card to leave no footprint, why the investigative agency found himself and was known to almost everyone. I couldn't understand whether the place where I shouldn't have lived was figured out. 'The investigative agency must have a secret that I haven't told myself yet,' said Rig Maiden, who tried to reveal the secret through a lawyer but didn't go as planned and fired two lawyers in quick succession. Eventually, I decided to defend myself.
Rig Maiden was allowed to use the legal library for five hours a day. After reading various materials, Mr. Rig Maiden discovered that the name 'Stingray' appeared in it. Rig Maiden, who was in custody, was not allowed to use the Internet, but he learned that Stingray was widely used by law enforcement agencies using all sorts of methods, including collaborators.
The problem that exists here is that the warrant was not used in the investigation. Regarding the pros and cons of using Stingray for investigation without a warrant, it is said that there is no common understanding among judges and judges, but a device that can determine the whereabouts of the subject and intercept the communication content is available. Some have expressed concern about being able to use it without a warrant.
By Esther Vargas
Rig Maiden finally summarized what he had investigated. According to the report, the police first tracked the IP address of the data communication terminal on the network to find out, and then referred the information to the Internet service provider Verizon Wireless, so that the contractor was Mr. Rig Maiden who used a pseudonym. I figured out. At this time, Verizon provided police with a record showing that the AirCard associated with the IP address was communicating through some specific cell towers in Santa Clara. Eventually, police probably used Stingray to find the exact area of the room where Mr. Rig Maiden lived.
Around 2010, Mr. Rig Maiden decided that he needed a collaborator to inform him of this, and he was involved in various organizations such as the American Civil Liberties Union (ACLU) and the Electronic Frontier Foundation (EFF). We have started activities such as sending the details and research files of. After that, the existence of Stingray gradually became known to people, and there were growing concerns about the actual situation of its use.
In January 2014, Rig Maiden and the federal prosecutor agreed on a judicial transaction. However, even after that, no conclusion was reached on the discussion about the operation of Stingray without a warrant, and it can be said that the investigative authorities are in a state where Stingray can be used freely. In today's society, where the forms of crime have changed, just as the advent of new technologies has changed people's lives, how have the methods of cracking down on crime changed, and what measures can be taken to prevent their operation and abuse. It can be said that society is approaching a turning point in thinking about whether it is necessary.
Related Posts:
in Note, Hardware, Smartphone, Posted by darkhorse_log