Amazon's DNS service "Route 53" is attacked and virtual currency with a market price of 16 million yen is deprived from users

AWS's online DNS service "Route 53" was subjected to a cyber attack. The virtual currency service that used Route 53 was illegally redirected traffic, resulting in the service user stealing the virtual currency of about 150,000 dollars (about 16 million yen).
Hijack of Amazon's internet domain service used to reroute web traffic for two hours unnoticed
https://doublepulsar.com/hijack-of-amazons-internet-domain-service-used-to-reroute-web-traffic-for-two-hours-unnoticed-3a6f0dda6a6f
Suspicious event hijacks Amazon traffic for 2 hours, steals cryptocurrency | Ars Technica
https://arstechnica.com/information-technology/2018/04/suspicious-event-hijacks-amazon-traffic-for-2-hours-steals-cryptocurrency/
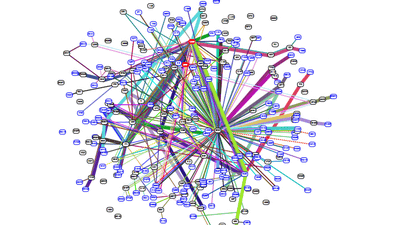
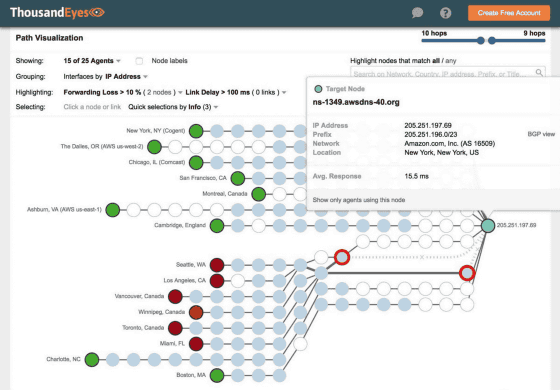
InternetIntelligence discovered that DNS traffic of AWS's cloud DNS service "Route 53" was hijacked for approximately two hours from around 11 o'clock on 2018, and reported it on Twitter.
BGP hijack this morning affected Amazon DNS. ENet (AS 10297) of Columbus, OH announced the following more-specifics of Amazon routes from 11: 05 to 13: 03 UTC today:
- InternetIntelligence (@InternetIntel)April 24, 2018
205.251.192.0/24
205.251.193.0/24
205.251.195.0/24
205.251.197.0/24
205.251.199.0/24
A cyber attacker is believed to have rerouted the DNS traffic of Route 53 by an intermediary attack using the Equinix server. According to InternetIntelligence, 1300 IP addresses were hijacked by a malicious redirect. It is also pointed out that attackers use BGP, a protocol that is used to route Internet traffic around the world, and Amazon and others have no effective means to prevent attacks.
At the time of article writing, it was only the MyEtherWallet that provides online wallet of the virtual currency that was damaged by the DNS traffic redirect of Route 53. The MyEtherWallet user is redirecting the traffic to the Russian domestic server and as a result of being clicked using the fake HTTPS certificate, the virtual currency Ethereum has been stolen and the damage amount is about 150,000 dollars (about 1600 Ten thousand yen) has been reported. Since it was confirmed that about 17 million dollars (about 1.9 billion yen) of virtual currency was held in the attacker's virtual currency wallet before the execution of the cyber attack this time, MyEtherWallet is the only one It is speculated that it will not be the target of.
Related Posts:
in Software, Web Service, Security, Posted by darkhorse_log