Nuclear power plants in the United States are exposed to cyber attacks

ByPeteburke 73
It became clear that the cyber attack was made to the control system of the nuclear power plant in the United States. If nuclear power plants become uncontrollable, there is a risk of serious damage, so on May 11, 2017 President Donald Tramp signed the Presidential Decree to strengthen cyber security measures for critical infrastructure We are strengthening security, but it seems there is one aspect of "self-interest" if you trace the originals in the first place.
Hackers Are Targeting Nuclear Facilities, Homeland Security Dept. and F.B.I. Say - The New York Times
https://www.nytimes.com/2017/07/06/technology/nuclear-plant-hack-report.html
Since May 2017, the US Department of Homeland Security and FBI have prepared an emergency joint report on the increasing number of server attacks targeting US energy facilities. Among the targets of this report is Wolf Creek Nuclear Operating Corporation (Wolf Creek), a nuclear power plant management company located near Burlington, Kansas. The New York Times who got the report have confirmed that the experts have reviewed the content and that it was the second highest threat level.

In the report, contents such as whether the cyber attack was the purpose of industrial espionage to steal confidential information or the work to destroy energy related facilities was not clarified, and the intruding by the hacker was permitted The number of facilities etc is also unknown. Wolf Creek officials responded to The New York Times' interview that "Wolf Creek's corporate network and network operating nuclear power plants are separate and operating systems are not affected by cyber attacks" It is.
According to two experts familiar with cyber attacks, it is mostly that the cyber attack targets engineers who have direct access to the system of energy facilities. A senior engineer with broad access right related to system control sends a Word document file embedded with malicious code called a resume attached to the e-mail, infects the PC, enters the network rampant It seems to be doing.
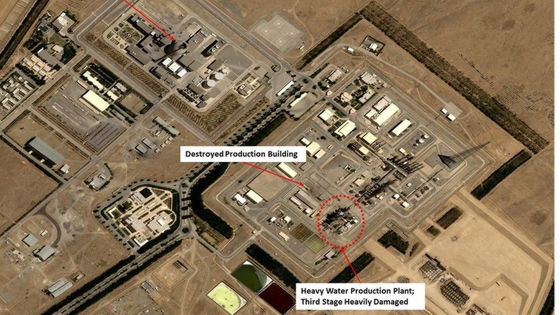
Attack aimed at nuclear power plants, etc. In 2008, the United States and Israel jointly developed Malware Stuxnet to attack the system of nuclear enrichment facility in Iran (Stax net) Is said to be the origin. It is believed that the US invaded the system controlling Iran 's nuclear power plants using Stuxnet and destroyed one - fifth of the centrifuges in Iran.

Mr. John Wellinghof, former Federal Energy Regulatory Commission chairman, said, "We could not expect that critical infrastructure control systems would suffer from malware damage, but the US government that executed the Stuxnet plan , The New York Times pointed out that it could have foreseen a cyber attack on important facilities such as today's nuclear power plants.
The hacking tool developed by NSA, an intelligence agency of the US Department of Defense's Department of Defense, was stolen by hackers, triggered a global disarray "Wanna Cry"Or"NotPetyaConsidering also that the malware such as "was developed, the cyber attack by the US government is rebounding as a cyber attack targeting the US domestically.
Related Posts:
in Security, Posted by darkhorse_log