"SeaGlass" to elucidate the actual state of monitoring device "IMSI catcher" which makes eavesdropping of conversation of smartphone by government and hackers · Malware infection / location identification possible

ByErvins Strauhmanis
"IMSI Catcher(Imsi Catcher) "allows you to intercept phone calls on mobile phones and smartphones, track their location, and send malware to targeted devices. Although this device is known from public records etc. that law enforcement agencies such as New York, Baltimore, Milwaukee, Anaheim, Tacoma, Tucson, etc. use it for cars and aircraft to identify suspects , I also know that it is being used to escape judicial monitoring. A researcher at the University of Washington who was concerned about such a situation said "Sea Glass"IMSI catcher detection device has been developed and the actual state is clarified.
City-Wide IMSI-Catcher Detection - SeaGlass
https://seaglass.cs.washington.edu/
Catching the IMSI-catchers: SeaGlass brings transparency to cell phone surveillance | UW Today
http://www.washington.edu/news/2017/06/02/catching-the-imsi-catchers-seaglass-brings-transparency-to-cell-phone-surveillance/
IMSIIs a unique identification number assigned to all mobile phone users of GSM and W-CDMA and consists of 15 digits (or 14 digits) numbers. In Japanese, it is called "international mobile device subscriber identification information", and the information is stored in the SIM card issued by the communication carrier.
Occasionally IMSI is transmitted from the mobile terminal to the communication network, but it contains detailed information about the terminal. "IMSI Catcher" is a device that can intercept communication with a terminal by disguising a base station of a communication carrier and can extract IMSI information. And it is "SeaGlass" to clarify its existence.
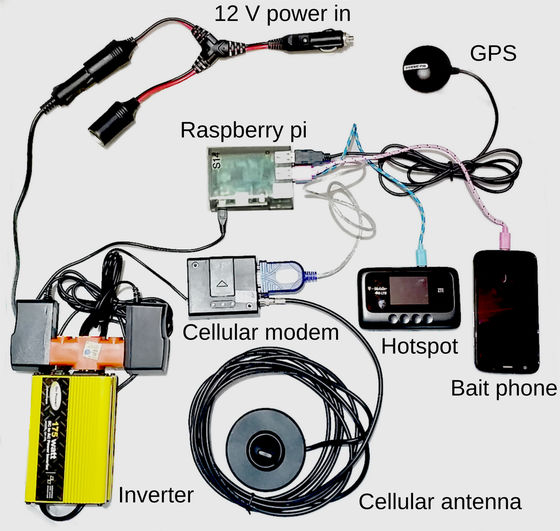
With Raspberry pi as the core, SeaGlass is a device connected with prepaid mobile phone, GPS, cellular modem and receiving antenna that scans the cell spectrum, router for uploading data, etc. Power is supplied via the inverter to the car Connect the battery.
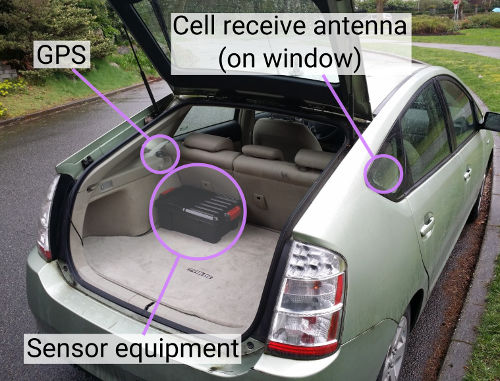
This "Sea Glass" sensor is installed in the trunk of the car, the receiving antenna and the GPS are installed near the window.
The research team analyzed the data of the cellular network obtained by running "SeaGlass" equipped vehicles in Seattle, Washington State and Milwaukee, Wisconsin for 2 months.
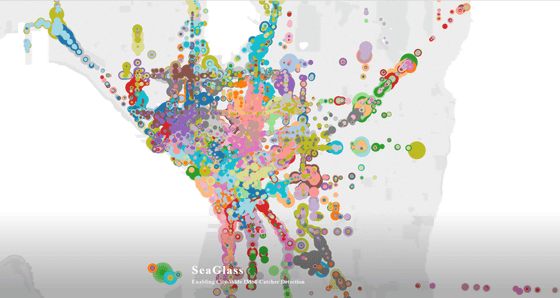
The IMSI catcher disguises as if it is one of ordinary cellular networks, and sends and receives it secretly on the same frequency (channel). At that time, it may mimic the identification characteristics of normal base stations, but at the same time, different channels may be used avoiding interference with the network. Most base stations transmit one or two channels, but if there are base stations that emit more channels in the data it means that there is a possibility of being an IMSI catcher.
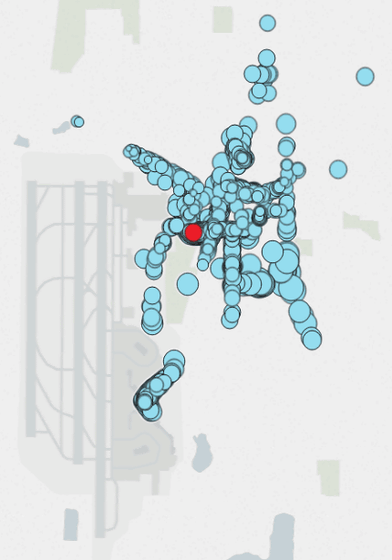
An example of this is found in the vicinity of the US Citizenship and Immigration Bureau building in southern Seattle. The circle indicates that SeaGlass received the data, and the color is divided for each channel. In Seattle and Milwaukee measurements, 96% of the base stations were transmitting on a single channel, but at the arrowhead, six channels were detected with the same cell ID.
Also, the base station has characteristics of configuration properties, which are almost the same for base stations where the same carrier is deployed in the same city. However, at Seattle-Tacoma International Airport, we found a case showing abnormal properties despite data measured for the same cell ID.
However, the researchers thought that it was not enough to judge that these were signals from the IMSI catcher immediately, and said that they would like to carefully consider the conclusions.
Mr. Ivan Smith, a member of the team, this problem is tremendously handled by one research team, so bring it to the community, gather more data in the cloud source and create the result in a meaningful way We want to find a partner to go on.
The code for making "SeaGlass" is released on GitHub.
GitHub - seaglass-project / seaglass
https://github.com/seaglass-project/seaglass

Related Posts: