Service "nomx" that says "the world's most secure e-mail protocol" can easily be hacked and experts point out
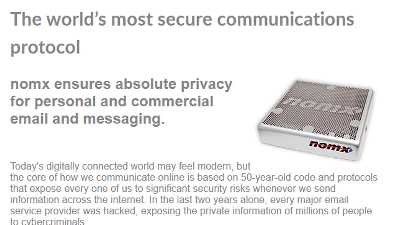
We provide protocols and hardware that send and receive e-mails as a phrase "the world's most secure communication protocol"NomxSecurity experts point out that the service of "Nomex (Nomex)" was actually able to hack easily in fact, and it is a situation that the manufacturer refutes.
Nomx: The world's most secure communications protocol
https://scotthelme.co.uk/nomx-the-worlds-most-secure-communications-protocol/
BBC exposes flaws in 'world's most secure' email service - BBC News
http://www.bbc.com/news/technology-38934822
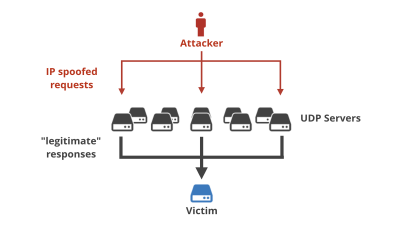
E-mails sent and received via the Internet are "brought" from source to recipient through a number of servers in that route. Actually, since the data only moves, there is no movement of the object, but the data of the mail is copied to the passing server. And since there are countless servers between the routes, and many of them are hacked by hackers and others, it can be said that no matter how data leakage happens at any stage it is quite noisy.
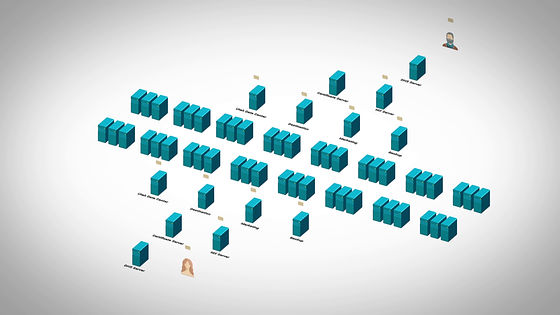
The service of nomx is to try to solve such a problem. According to the name meaning "no mail exchange server", nomx is a system with a mechanism that no third party intervenes using dedicated protocols and hardware. The catchphrase "Everything else is insecure (Other than this is not secure)" is listed on the homepage of the manufacturer site, and personal private mail servers are priced from $ 199 to 399 dollars (about 22,000 yen to 40,000 It is sold at a price of 5000 yen).
You can see the problem of existing mail system and how nomx's system is running in the following movie that the company creates.
Nomx - how it works - YouTube
About such nomx, security analyst Scott Helme got the real thing and conducted a survey to confirm safety on both sides of hardware and software, but I could not confirm the high level of safety that the company insists, It was easy to hack and browse mail and operate "spoofing" and so on.

The body of nomx.

The Ethernet panel on the rear panel and the Micro - USB terminal for the power supply are located on the side part.


A sticker with a MAC address written on the bottom is affixed, but Mr. Helme, who saw this, felt "It's a very familiar MAC address", he said that he felt a kind of "premonition".

Also, when Helme opened a case that had a bad premonition to the smallness of the board seen from the heat exhaust port at the upper part of the main body, the actual board is much smaller than the main body as expected Pattern.

The premonition held by Mr Helme was "Is not this Raspberry Pi?", But this is exquisite. Helme feels unbalanced in that Raspberry Pi of his own microcomputer has created a device singing out dedicated hardware while refusing that "Raspberry Pi is not good" Thing.

What he felt as "familiar" by Helme is the part where the beginning of the MAC address is "b 8: 27: e b". This is the address assigned to the Raspberry Pi Foundation, which also highlights the fact that it is based on Raspberry Pi.

And Helme who launched the power of nomx did a software verification. Helme suddenly succeeded in acquiring Root, he conducted a survey of the software running on the machine. Then, the following things have been found out, it seems that they found that old ones several years after release were used.
· Raspbian GNU / Linux 7 (wheezy): Last update date 7th May 2015
· Nginx version: nginx / 1.2.1: release date June 5th 2012
· PHP 5.4.45 - 0 + deb 7 u 5: Release date September 3, 2015
· OpenSSL 1.0.1 t: Release date May 3, 2016
· Dovecot 2.1.7: Release date May 29, 2012
· Postfix 2.9.6: Release date February 4, 2013
· MySQL Ver 14.14 Distrib 5.5.52: Release date September 6, 2016
In addition, due to the fact that the latest patch has not been applied, some software is left in a state where bugs exist, and the passwords set for some software are "password" and "death" There were also things like that. Helme also found several problems in the web UI used to manage secure mail services. It is pointed out that these are serious vulnerabilities because they will make it possible for hackers to attack the nomx system if these are exploited and they have administrator authority He said that he was also successful in making hidden accounts.
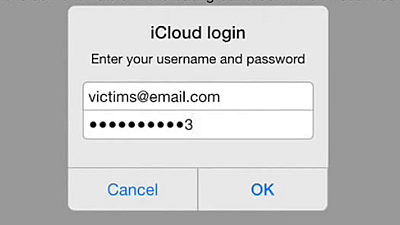
In fact Mr. Helme talked about in the interview of Motherboard that he was illegally looking at the contents of the mail, sending the mail, and deleting it successfully. About the cause of this problem HelmeCross site request forgeryWe are vulnerable to CSRF. Hackers can hijack nomx 's account by letting the user access the traped website.
In response, Will Donaldson, CEO and founder of nomx, has a counterargument. In a long objection e-mail, Mr. Donaldson said that CSRF issues only occur in cases where the user opens a specific page when the user opens the management page of nomx (Helme noted this as a mistake) , We have announced that this problem has been resolved with the indication of Mr. Helme. Donaldson also argues that the equipment he used for verification by Mr Helme is of old type and that the current machine does not use Raspberry Pi.
In addition, Mr. Donaldson said "We are taking actions such as updating, upgrading, and exchanging the terminals affected by this problem" "Notified to users" "One machine affected at this time He said that he had contacted him, "I'd like to send a modified machine as a thank you for pointing out" to Helme. However, Helme said, "How do you notify the update in the first place, how is it not disclosed?" "Please show me the contents of the notification that I sent it to the user" "How did the affected machine "Have you ascertained that there was no" one "?
In addition, when first contacting nomx, Helme had notified Mr. Donaldson "30 day disclosure policy" "to announce this content after 30 days" in consideration of the importance of the problem. The first communication was on March 14, 2017, the notice of 30 day disclosure policy was on March 18, the same year, and BBC Click, who had been investigating with Mr Helme, announced this case on April 27 and It is getting.
Mr. Helme's findings are scrutinized by security expert Paul Moore and Moore calls nomx "an overly expensive and outdated mail server". In addition, Motherboard does not construct e-mail system by its own, but "As many security experts think, there are some problems but taking the world's highest level of security measures like Google and Microsoft It is better to trust a company and use the service. "
Related Posts: