Research result that credit card settlement information can be guessed in only 6 seconds

ByRoxanne Tamayo
About the method which can guess information necessary for on-line settlement using credit card in only 6 seconds, the results of the research which VISA and MasterCard investigated by the University of Newcastle are published.
Ali MA, Arief B, Emms M, van Moorsel A. Does The Online Card Payment Landscape Unwittingly Facilitate Fraud? IEEE Security & Privacy 2017. In Press.
(PDF file)http://eprint.ncl.ac.uk/file_store/production/230123/19180242-D02E-47AC-BDB3-73C22D6E1FDB.pdf
Thieves can guess your secret Visa card details in just seconds | Ars Technica
http://arstechnica.com/security/2016/12/thieves-can-guess-your-secret-visa-card-details-in-just-seconds/
Trainee who aims at credit card settlement is attacking customer's payment information from hundreds of Internet shopping sites with browser bot signature. According to a survey of the University of Newcastle, there are several ways that attackers can guess the information necessary for credit card transactions, but each starts with obtaining a 16-digit credit card number. An attacker can purchase a credit card number one dollar (about 110 yen) or less from the black market, there is also a method of gulping up a 16-digit number by using an NFC reader attached to a smartphone,Luhn algorithmBased on the first six figures based on the card brand · issuing bank · card type can combine 16 digits can be guessed.
An attacker can guess "card expiration date" and "3 digit security code (CVV)" in only 4 seconds from the 16 digit credit card number. If you have these information and 16-digit card number, you can make payment at most online shopping sites. Some sites are more secure than asking for billing addresses, but in similar fashion it is only 6 seconds that you can guess to the exact billing address.
A screenshot of the software that is actually used for guessing attacks.
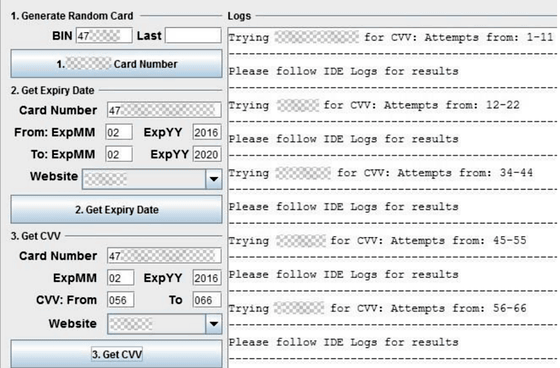
This is based on the technology that the browser bot randomly calculates the 16-digit card number through about 400 e-commerce sites, of which 26 sites have only two confirmation items for credit card payment On the other hand, 291 sites said there were three confirmation items. Since the items to be confirmed by the site are different, the bot is able to infer accurate settlement information by acquiring customer information from multiple e-commerce sites complexly.

ByFrankieleon
Researchers at the University of Newcastle explain, "Vulnerabilities that can be effectively exploited throughout the settlement system are being revealed by different security measures depending on the website." In the method pointed out this time, introducing more confirmation items for a website to strengthen security will give us speculation materials on the confirmation items of different websites, and the potential and unconscious payment system It leads to weakening the whole.
According to the research team of the University of Newcastle, VISA, the largest credit card payment system, does not use such a detection system for "mass speculation attack". On the other hand, rival MasterCard is operating a system that can shut down attacks before the mass speculation attack succeeds. The research team contacted 40 websites that are exposed to the most mass speculation attacks, and some websites reviewed the items to be checked. At least the credit settlement system vulnerability has been improved slightly, but the news media · Ars Technica reported this issue, "A better solution is that VISA will introduce the same detection system as MasterCard" I point out.
Related Posts: