It turned out that more than 900 million Android terminals had a vulnerability to be hijacked devices, and how to check for vulnerabilities
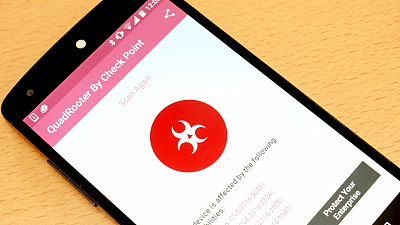
A vulnerability was discovered on an Android terminal equipped with a Qualcomm chip and it turned out that there was a possibility that the terminal could be compromised by an attacker. According to researchers, this vulnerability affects more than 900 million Android terminals. Following this situation, an application that allows you to investigate whether there is vulnerability on your Android device is released.
QuadRooter: New Android Vulnerabilities in Over 900 Million Devices | Check Point Blog
http://blog.checkpoint.com/2016/08/07/quadrooter/
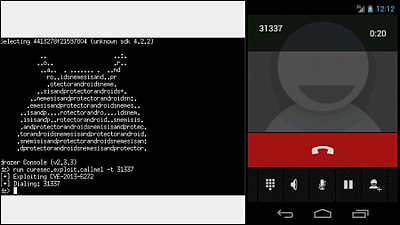
There are four vulnerabilities in Qualcomm's chip, and they are collectively called "QuadRooter". By using one of the vulnerabilities discovered this time, an attacker can make root access without special approval by letting the attacker install a specific application on the target. This allows an attacker to gain full access to internal data, functions such as camera and microphone.
An example of a terminal equipped with a chip where a vulnerability was found is as follows.
· BlackBerry Priv
· Blackphone 1 and Blackphone 2
· Google Nexus 5X, Nexus 6 and Nexus 6P
· HTC One, HTC M9 and HTC 10
· LG G 4, LG G 5, and LG V 10
· New Moto X by Motorola
· OnePlus One, OnePlus 2 and OnePlus 3
· Samsung Galaxy S7 and Samsung S7 Edge
· Sony Xperia Z Ultra
You can check if your device is vulnerable by using the following application.
QuadRooter Scanner - Android application on Google Play
https://play.google.com/store/apps/details?id=com.checkpoint.quadrooter
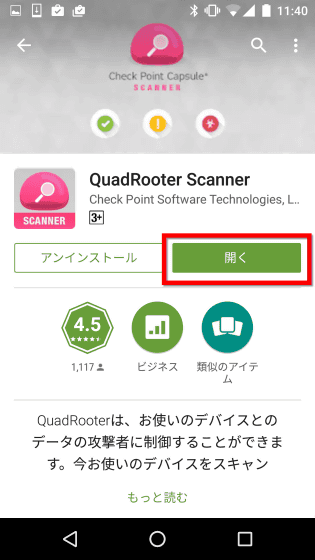
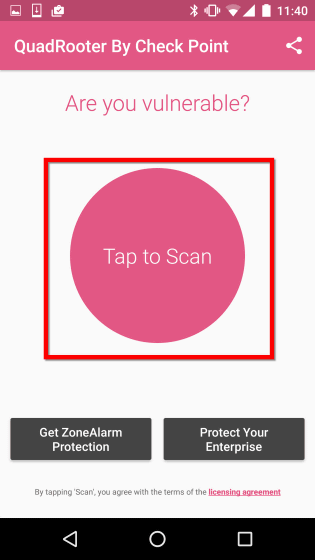
First, search QuadRooter Scanner on Google Play and tap "Install".

Tap "Open".
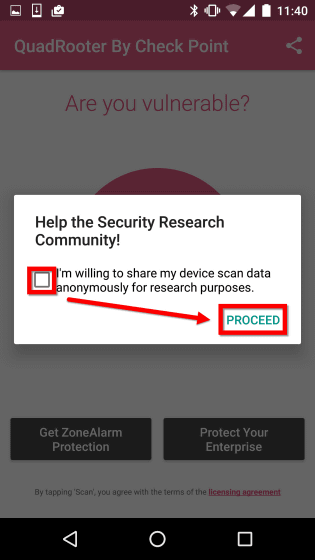
As checked in the checkbox "I will share device scan data anonymously for research", if you do not want to send, uncheck and press "PROCEED".
Since the home screen looks like this, tap "Tap to Scan" to check if there is vulnerability.
The scan will end in about 10 seconds.

The result is like this. When I checked Nexus 5, it contained a perfect vulnerability.

In addition, Google spokesperson announces that one of QuadRooter is expected to be revised in the September update, and Qualcomm also for partner companiesProvide a correction codedoing.
Related Posts:
in Software, Smartphone, Review, Security, Posted by darkhorse_log