It is obvious that 32 million Twitter account information (user name, password, mail address) is sold
ByEsther Vargas
Number of active users per monthThere are 320 million people worldwide, and SNS with 35 million users surpassing Facebook etc. in Japan is Twitter. It was revealed that about 32 million Twitter account information was sold and sold among hackers on the Internet.
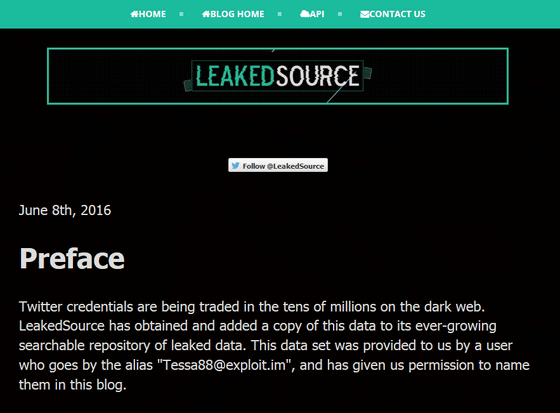
LeakedSource Analysis of Twitter.com Leak
https://www.leakedsource.com/blog/twitter
Passwords for 32M Twitter accounts may have been hacked and leaked | TechCrunch
http://techcrunch.com/2016/06/08/twitter-hack/
A reported 32 million Twitter passwords up for sale, but Twitter was not hacked
http://www.neowin.net/news/a-reported-32-million-twitter-passwords-up-for-sale-but-twitter-wasnt-hacked
In June 2016, we created a database of information-related security-related data "LeakedSource"Revealed that the account information for 32.88, 8300 Twitter accounts is traded on-line. The traded Twitter account information is a user name, registered e-mail address, and password, according to LeakedSource, although some of these account information is disabled, it seems that many of the account information can be used now is.
After LeakedSource revealed this situation, the official account of Twitter commented, "We are investigating this password leak to protect user safety and accounts."
To help keep keep people safe and accounts protected, we 've been checking our data against what's been shared from recent password leaks.
- Twitter Support (@ Support)June 6, 2016
The strange thing about the leakage of account information leaks this time is that information leakage is not "hacked Twitter", it is "it leaked from somewhere else". As per the above tweets, Twitter is starting to investigate information leakage, but it seems there was no sign of hacking.
Indeed, Michael Couttes, executive officer at Twitter's information security department, said, "We investigated a report that Twitter's account information is being sold secretly.As a result of our investigation our system is hacked I am convinced that it is not "I am tweeting, denying the possibility that Twitter was hacked and the information leaked out.
We have investigated reports of Twitter usernames / passwords on the dark web, and we confident that our systems have not been breached.
- Michael Coates ஃ (@ _ mwc)June 9, 2016
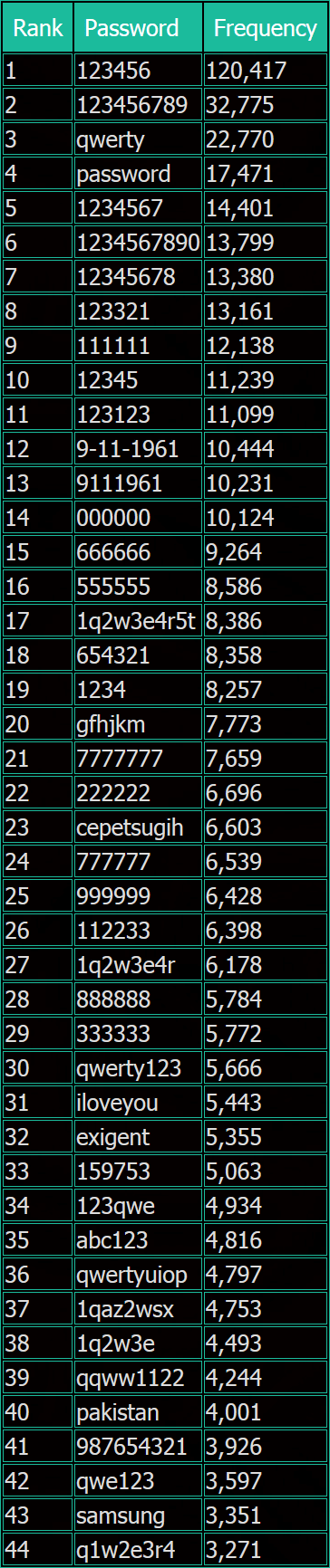
The most frequently used password ranking top 44 in about 32 million Twitter accounts actually traded on the Internet are as follows. The most frequently used password was "123456", and 12,477 were using this password. Other simple passwords such as "123456789 (33,775 cases)" "qwerty (22,770 cases)" "password (14,771 cases)" followed. As for the unique password which is used frequently in the leaked information, "9-11-1961 (10,444 cases)", "gfhjkm (777 cases)", "cepetsugih (6603 cases)" There are "pakistan (4001 cases)" and so on.
Please note that the Twitter account information that was being sold was in an unencrypted state, so it is safe to store confidential information such as passwords on its server without encrypting Twitter It is impossible, and the international news siteNeowinI point out. Even looking at the data format and the e-mail address domain of leaked account information, I can not think that it is information obtained by hacking Twitter. In addition, many of the Twitter accounts that were leaked were from domains popular in Russia, so it seems that there was some information leakage in relation to Russia.
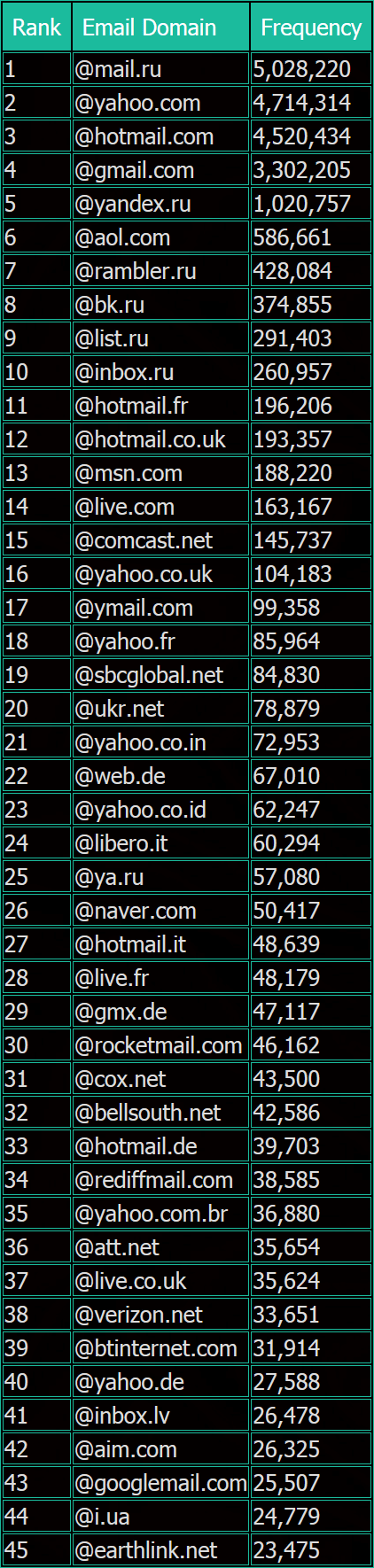
The following is an e-mail address that was used for approximately 32 million leaked account information, divided into the domains, and arranged in descending order of usage frequency. The most commonly used one was not Gmail's "@ gmail.com" or Yahoo!'s "@ yahoo.com" but the domain of Russian free e-mail service Mail.ru "@ mail.ru (5,020,282 ") Was.
In addition, Neowin recommends setting complicated and long passwords which are different for all web services, and we also recommend using 2 step authentication if possible.
· 2016/06 / 13 10:55 Additional description
Following the leak, Twitter is requesting reset of the password by e-mail to the Twitter account where account information leaked. Also, in order to prevent other account owner from accessing the corresponding account without permission, it seems that you can no longer log in to the corresponding account unless you execute the password reset notice sent to the user. In addition, Twitter has strong password setting,1 PasswordYaLastPassWe recommend using password manager such as.
Keeping your account safe | Twitter Blogs
https://blog.twitter.com/2016/keeping-your-account-safe
Related Posts:
in Software, Smartphone, Security, Web Application, Posted by logu_ii