What is amazing technique that breaks the IC chip security of credit card?

ByFrankieleon
Most current credit cards and cash cards are not traditional magnetic stripes, but boast more secure securityChip & PIN"IC chips are adopted. It is a Chip & PIN system thought to be unbreakable unless you know the PIN code, but it has become apparent that it has been forcibly broken by a tremendous hacking group and is no longer absolutely safe.
How a criminal ring defeated the secure chip-and-PIN credit cards | Ars Technica
http://arstechnica.com/tech-policy/2015/10/how-a-criminal-ring-defeated-the-secure-chip-and-pin-credit-cards/
X-Ray Scans Expose an Ingenious Chip-and-Pin Card Hack | WIRED
http://www.wired.com/2015/10/x-ray-scans-expose-an-ingenious-chip-and-pin-card-hack/
In the event of a credit card theft occurred in France in May 2011, the damage caused by the purchase of a large number of goods using a stolen credit card occurred. Since it is thought that the victim's PIN code itself is not leaked, the possibility that the security of the IC chip of the credit card was broken was pointed out, but details were not clear.
After that, a 25-year-old woman who was seen as one of the criminals of a credit card theft case was arrested and it was found that a large amount of cigarettes and the like were easily purchased on the black market using the stolen credit card. Credit cards, cash, etc. stolen in the search process will be confiscated. In this case, it is believed that the total of 600,000 euros (about 80 million yen) was caused by settlement of over 7000 credit cards by 40 credit cards.

The confiscated credit card was soldered so that the IC chip was remodeled and another chip engraved on the IC chip "FUN" covered.
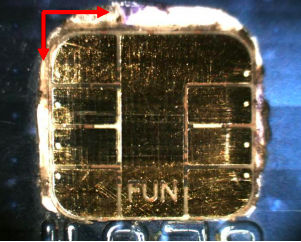
It seems that the thickness has increased from about 0.4 mm to 0.7 mm compared to the normal IC chip because of the chip on chip state.
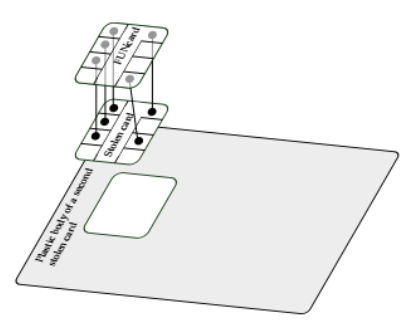
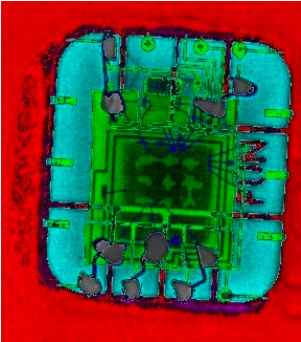
As this modified credit card was used as evidence for investigation and trial, it was not allowed to disassemble. Therefore, researchers analyzed IC chips using X-rays so as not to physically destroy them. The part colored in green of the following image is the original IC chip of the credit card.
The figure below shows the analysis of the IC chip used in the Chip & PIN method with X-rays. Number 1 indicates memory (AT 24 C 64), number 2 indicates micro controller (AT 90 S 8515 A).
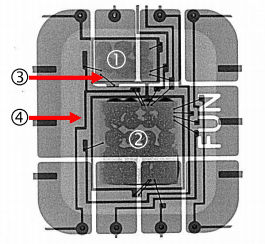
On the other hand, the X line of the chip remodeled with FUN chip is shown below. As indicated by No. 6 and No. 7, it became clear that wiring was added and the circuit was changed.

It is understood that the IC chip whose circuit was changed by FUN chip was changed to accept any PIN code on POS system. Actually, this technique of invalidating the security of the Chip & PIN method by physically modifying the IC chip itself is called "man-in-the-middle attackMan-in-the-middle attack) "Was invented by researchers at Cambridge University in 2010.
When Organized Crime Applies Academic Results A Forensic Analysis of an In-Card Listening Device.pdf
(PDF file)http://eprint.iacr.org/2015/963.pdf

Although this research revealed that there is vulnerability in the security of Chip & PIN system, at that time it is thought that realization would be difficult because it is necessary to craft a microscopic line to a very small size chip at that time It was done. However, in less than a year from the publication of research results, the hacking method was realized.
Professor Ross Anderson, who cooperated with the above research, thought that IC chip hacking of this credit card was not created by research being released, "While someone would have tried this technique "I said. It seems that introduction of a security method that changes to Chip & PIN method is desired since security of Chip & PIN method is no longer seen as breakthrough state.
Related Posts: