A clause that will allow the government to intercept citizens' encrypted communication content is about to be included in the EU's new standard regulation ``eIDAS 2.0''

The nearly final version of eIDAS 2.0 , a proposed amendment to
Article 45 Will Roll Back Web Security by 12 Years | Electronic Frontier Foundation
https://www.eff.org/deeplinks/2023/11/article-45-will-roll-back-web-security-12-years

Last Chance to fix eIDAS
https://last-chance-for-eidas.org/
Europe prepares to break browser security with eIDAS 2.0 • The Register
https://www.theregister.com/2023/11/08/europe_eidas_browser/
eIDAS defines electronic signatures within the EU, the legal framework surrounding them, time stamps, website certificates, and the scope of newly defined authentication services (trust services).
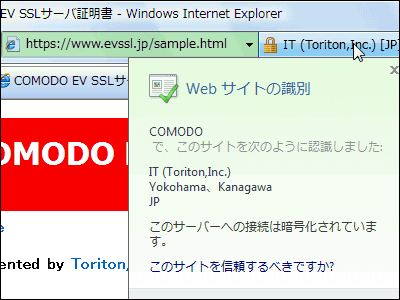
Article 45 of eIDAS 2.0, the proposed amendment, stipulates that ``browsers must trust a government-appointed public key certificate authority (certificate authority), It is prohibited to impose security requirements on certificate authorities beyond the scope approved by the ETSI . This means lowering the security standards that browsers require from certificate authorities, limiting competition and the ability of browsers to improve security for their users.
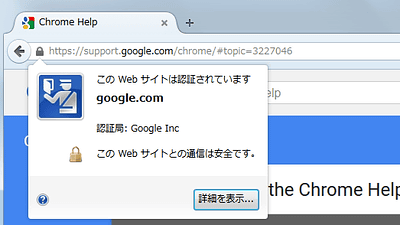
The role of a certificate authority is to issue root certificates to secure encrypted communications between websites and users, but if someone else obtains the same root certificate, they cannot intercept the encrypted communications. becomes possible. This allows governments to request copies of root certificates from certificate authorities they control and perform man-in-the-middle attacks.
In fact, in the past, Kazakhstan, known for its one-party dictatorship, required citizens to install a government-certified root certificate, and it was pointed out that encrypted HTTPS communications could be intercepted by the government. . Mozilla and Google responded by blocking the root certificate issued by the Kazakh government.
Google and Mozilla announce that they will block root certificates authenticated by authoritarian countries - GIGAZINE
However, if the security standards for government-appointed certificate authorities are lowered, browsers will no longer be able to exclude certificate authorities and take measures even if they suspect that their encrypted traffic is being intercepted. He said he would put it away.
Mozilla, which develops the Firefox browser, said in a statement: 'This allows governments in EU member states to issue certificates for websites for purposes of interception and surveillance. It can be used by all EU citizens, even if they are not registered or have no affiliation with a Member State.There are independent checks and balances on the certificates that Member States allow and the decisions they take regarding their use. does not exist.”
Google's Chrome security team also said, 'Section 45 of eIDAS impedes the ability of browsers to enforce specific security requirements on certificates, potentially hampering advances in web security for decades.' 'We, along with many past and present leaders of the international web community, have grave concerns about the security implications of Section 45,' they wrote in a blog post , calling for changes to the law.

Related Posts:
in Web Service, Security, Posted by log1h_ik