What are the three groups that carry out cyber attacks and espionage for the sake of 'China's national interest'?

Cybereason, a provider of cyber-attack countermeasure platforms, reported in a new report on three threat actors targeting Southeast Asian carriers and working for 'China's national interests.' Threat actors have been shown to be lurking in carriers' systems, extracting personal information about politicians and dignitaries, as well as being involved in large-scale hacking using Microsoft Exchange Server.
DeadRinger: Exposing Chinese Threat Actors Targeting Major Telcos
Five Southeast Asian telcos hacked by three different Chinese espionage groups --The Record by Recorded Future
https://therecord.media/five-southeast-asian-telcos-hacked-by-three-different-chinese-espionage-groups/
Research finds cyber-snoops working for'Chinese state interests' lurking in SE Asian telco networks since 2017 • The Register
https://www.theregister.com/2021/08/03/cybereason_deadringer/
In March 2021, a large-scale hack was reported that exploited a zero-day vulnerability in Microsoft Exchange Server. The targets of the attack are wide-ranging, including infectious disease research institutes, law firms, higher education institutions, defense contractors, policy think tanks, and NGOs in the United States. Issued an urgent order to request. Microsoft also distributed an emergency patch, but it was pointed out that at least 30,000 organizations had been hacked by the time the emergency order was issued.
It has been said that there is a 'very sophisticated hacker group backed by the Chinese government' behind the above attacks, but in this regard Cybereason targets Southeast Asian carriers. He reported that there are three threat actors working for 'China's national interest'.

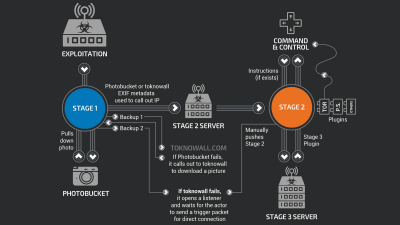
The five carriers targeted by the attack were not directly damaged by threat actors, but were used as a source of information to monitor politicians, business leaders, political activists, human rights activists, law enforcement agencies, etc. It was said that. According to Cybereason's Assaf Dahan, threat actors hide for long periods of time without being detected by the carrier's system, stealing information such as the target person's whereabouts, conversations, and message transmissions to profile the target. It is said that it was useful for.
In addition, 'The purpose of the attackers behind these intrusions is to allow persistent access to carriers, collect personal information, as well as billing servers containing CDR data,
The three threat actors mentioned in the report are 'Soft Cell,' 'Naikon APT group,' and 'Emissary Panda.' Of these, Emissary Panda is believed to be the group that installed the backdoor on the OWA folder in the early stages of the Microsoft Exchange Server attack. It is suspected that all groups are working for the national interest of China.
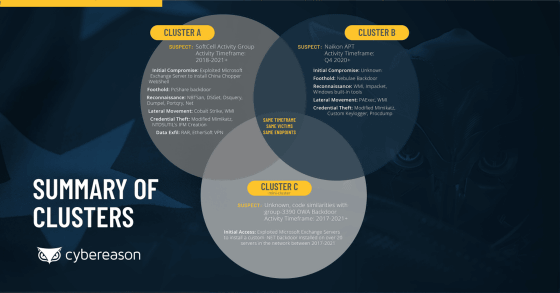
Emissary Panda's activity was observed between 2017 and the first quarter of 2021. Dahan gives some thoughts on why it wasn't detected for such a long time, prefaced by 'a difficult question.'
First, these threat actors may have been part of a group of
In addition, telecommunications carriers are taking security measures to protect the network, but the security tools used by each company are not the same, and there are tools that are not effective against sophisticated attacks. .. In addition, even if there are security measures that seem perfect, 'human error can occur' because it is humans who take the measures, Dahan said.
Cybereason pointed out that the three threat actors sometimes overlapped in terms of target environment, timeframe, and endpoints. 'At this point, we can't say what this duplication means, that is, we can't tell if the three groups are working independently or if they belong to one threat actor,' Cybereason said. increase. However, there are great concerns that national security could be threatened by Chinese government-backed espionage in any case.
Related Posts:
in Security, Posted by darkhorse_log