New evidence has been found for Supermicro's spy chip issue
On October 4, 2018, overseas media
Supermicro Hack: How China Exploited a US Tech Supplier Over Years
https://www.bloomberg.com/features/2021-supermicro/
Bloomberg spy chip story a misunderstanding: ex-GCHQ expert ―― 9to5Mac
https://9to5mac.com/2021/02/15/bloomberg-spy-chip-2/
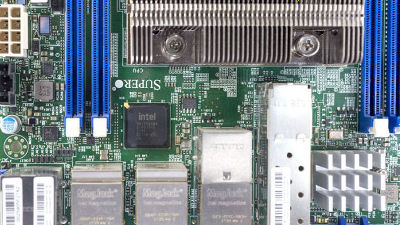
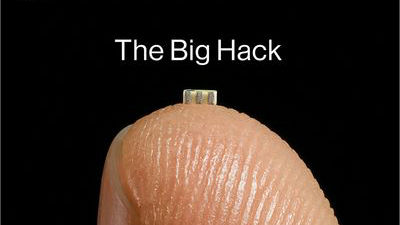
A 2018 Bloomberg report said, 'A chip smaller than a pencil lead was secretly placed on the base of a Supermicro motherboard, which allowed external access to network and system memory.' thing. Supermicro is an American company, but it was reported that the motherboard was manufactured in China and the PLA was charging the chip during the manufacturing process.
Bloomberg reports that Apple & Amazon server has been charged with a data stealing chip in the PLA's working force, Apple Amazon completely denied --GIGAZINE
On the other hand Supermicro and Apple, Amazon is the statement that 'the report of Bloomberg without any evidence, to request the withdrawal of the article' announcement was. From a technical point of view, Bloomberg's coverage remains questionable, according to experts. According to one expert, 'Given where the chip is allegedly embedded, the chip is presumed to be a'baseboard management controller (BMC) 'with system monitoring capabilities, but gaining root access to the BMC. Is not the same as getting full access to the main server OS, so Bloomberg's notation is misleading. '
Server expert explains why the 'Chinese spy chip suspected cyber attack' article is wrong --GIGAZINE
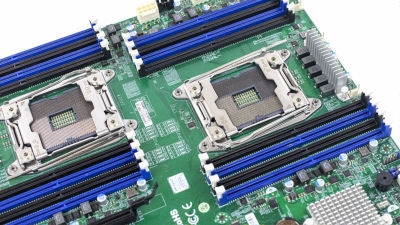
On the other hand, although there are technical inaccuracies in Bloomberg's coverage, many have said that cyberattacks such as those reported by Bloomberg are possible if such chips actually exist. Another expert than the one mentioned above said, 'If you succeed in changing the board design and component installation process, it is technically possible to intercept the SPI line between flash memory and BMC. the opinions of the ' says .
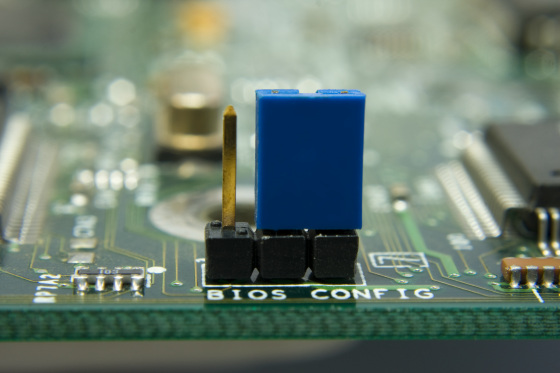
And on February 12, 2021, Bloomberg newly reported that 'expert investigations found malicious code in the BIOS of the Supermicro server used by the Pentagon.' According to media reports, the code discovered this time is 'embedded in unused memory in the BIOS chip and continues to send data to the outside as soon as the computer starts up.'
Manufacturers like Supermicro usually source most of their BIOS code from external companies. However, the experts who conducted this survey said that 'malicious code was found only in code designed inside Supermicro.' In addition, research has found that the same anomalous code was found on Supermicro servers manufactured at different times in different factories, 'this suggests that the code was introduced during the chip manufacturing phase. 'Bloomberg said.
However, some have already expressed negative opinions about this report. 'The origin of the'expert', the source of information, is very suspicious, and the coverage is vague,' said Matt Tate, a former British government communications headquarters employee and member of Google's security team. Pointed out. On his own Twitter, he tweeted, 'Well, do I have to follow the legend of the Supermicro chip again?'
Oh man, guess we have to do supermicro chip saga again
— Pwn All The Things (@pwnallthethings) February 12, 2021
Tate said the issue was so big that no one could support Bloomberg and called on Bloomberg to provide solid evidence.
Related Posts: