Vulnerability that can restore data that should have deleted on iPhone is found

Two hackers discovered that there is a vulnerability that allows iPhone to recover previously deleted photos and files and reported them in a mobile contest to discover iOS and Android bugs. This bug has already been reported to Apple, but the corresponding update has not come up at the time of article creation.
Apple Warned About iPhone X Hack That Stole "Deleted" Photo
https://www.forbes.com/sites/thomasbrewster/2018/11/14/apple-warned-about-iphone-x-hack-that-stole-deleted-photo/
The iPhone X can be hacked to pull your recently deleted files - The Verge
https://www.theverge.com/2018/11/14/18095621/iphone-x-hack-recently-deleted-files
Two victims of Richard Zhu and Amat Cama who found a vulnerability that makes it possible to repair iPhone data. The two vulnerabilities need to be able to access iPhone X, which is the target of attack, but researchers think that "attacks can be made from malicious Wi - Fi access points etc." .
The vulnerability was reported in "Mobile Pwn 2 Own" held in Tokyo. The vulnerability exists on Safari of iOS 12.1 and as a result of discovering this vulnerability, two people earn 50,000 dollars (about 5.7 million yen) from the contest.
Confirmed! The @ fluoroacetate duo combined a bug in JIT with an out-of-bounds Access to exfiltrate data from the iPhone. In the demo, they grabbed a previously deleted photo. In doing so, they earn themselves $ 50 K and 8 Master of Pwn points. # P2OTokyo
- Zero Day Initiative (@thezdi) November 14, 2018
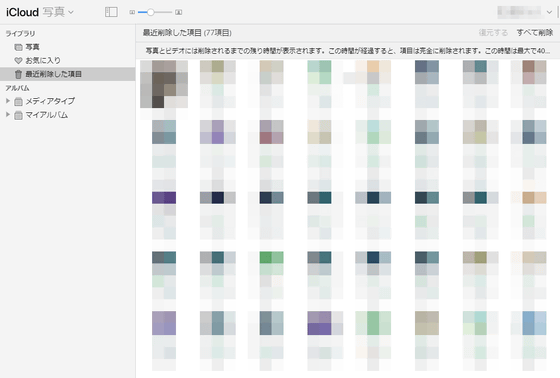
When trying to delete a photo on iPhone, "This photo will be deleted from" iCloud photo "of all devices." will be displayed. After that, the photo that actually deleted is stocked in "Recently Deleted Item" of "iCloud Photo" and will be deleted from the iCloud photo after a certain period of time (within 40 days) elapses from deletion. If there is no iCloud storage left, it will be deleted immediately.
However, Mr. Zhu and Mr. Cama discovered how to restore recently deleted photos with remote actors. According to two people, there is a vulnerability in the runtime compiler (JIT compiler) used to process computer code when the program is executed on iOS.
Through this JIT compiler, an attacker said that there is a possibility of getting recently deleted files. Also, in theory, it seems that all data processed by the JIT compiler may be vulnerable to attacks.
In addition, two hackers use these vulnerabilities to demonstrate the concept and restore the photos.
Related Posts: