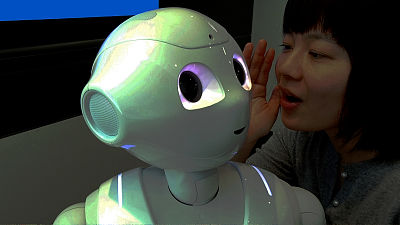
Peppers and researchers warn of security risks of robots
ByIbmphoto 24
Security service company ·IOActiveAccording to a report released by the company, important security problems were found from home and industrial robots sold by six companies. The list includes SoftBank'sA robot with emotion "Pepper"Also included.
(PDF file) Hacking Robots Before Skynet
http://www.ioactive.com/pdfs/Hacking-Robots-Before-Skynet.pdf
That Cool Robot May Be a Security Risk - The New York Times
https://www.nytimes.com/2017/03/01/technology/that-cool-robot-may-be-a-security-risk.html

Security problems were found in the following companies' robots.
·Softbank Robotics/NAO,Pepper
·UBTECH Robotics/Alpha 1S,Alpha 2
·ROBOTIS/ROBOTIS OP 2,THORMANG 3
·Universal Robots/UR3 robot,UR5 robot,UR 10 robot
·Rethink Robotics/Baxter,Sawyer
·Asura Tech/V-SidoMultiple robots with technology
The number of vulnerabilities found is close to 50, but the important thing is that the tests done by the researchers were not simple deep things that required significant investment and resources, they were very simple and rudimentary. An example of the vulnerability pointed out in this research is as follows.
· Communication problems
The user makes commands to the robot by programming, etc. However, in a robot using Wi-Fi or Bluetooth, this communication part may be hindered by an attacker or the secret information may be stolen Exist.
· Authentication problem
Although it is necessary for the user himself / herself to be recognized when programming the robot, some robots will be able to control the robot remotely without a user name or password.
· The problem that encryption is not enough
The robot has many user's private information such as password, encryption key, SNS account etc. However, researchers have seen that many robots are encrypted inappropriately whether they are not encrypted, exposing delicate information to potential attackers.
· Privacy information issues
Several robots are sending to a server at a remote location, such as "mobile network information", "current location information", "device information" without user consent.
· The problem of default security is weak
Many robots can access & program using software and others, but many robots can not change the default password. Researchers point out that users should be able to change their passwords because default passwords are open to the public or share passwords with robots of the same model.
Amazon's Voice Assistant Terminal "Amazon Echo"And "Google HomeAlthough the number of homes that adopt "is increasing, users will use these terminals because they trust companies. However, it is well known to manufacturers that there are few devices that properly handle vulnerable reports.

ByRick Turoczy
Lucas Apa, senior security consultant at IOActive says, "Manufacturers prefer to add features that the public is happy about, but they said that" robots are equipped with microphones and cameras, You can forget about the important problem of being able to grasp "and people are not aware of what results the robot can see, hear, and grab things about himself." I am talking.
Practical application of robots equipped with artificial intelligence such as automatic driving cars is getting real. On the other hand, it seems that researchers' view is that efforts on security problems are not sufficient. "As the necessity of e-commerce dropped encryption algorithms on a daily basis,Embedded systemIt will be the next big wave of the computer world. Failure to install safeguard is the same as forgetting to lock the door of the house "Afero"Said Joe Britt. The purpose of this research is also to "gather interest in that how robust security of today's robot is insufficient".
After notifying each company about this information, there were only four companies out of six who responded that only two companies said they would prepare patches against vulnerabilities. While there seems to have been an objection to the pointing out by researchers, Universal Robots said that he returned a comment saying "We are investigating the problem pointed out."
2017/03/09 Addendum
I have a comment from Astelak, so I will post it.
Current situation To the software for hobby robot which our company has released
For reference, it will be a sample limited to the end for hobby use.
In adopting it for commercial use, to a wider range of equipment and communication system
Since we will correspond, measures concerning security, too,
It varies greatly depending on the application.
Related Posts: